In January 2022, Oracle released a CPU (Critical Patch Update) which included CVE-2022-21360—a vulnerability affecting their Java SE platform and Oracle GraalVM Enterprise Edition. This security flaw resides specifically in the ImageIO component and allows an unauthenticated attacker to cause a partial Denial of Service (DoS) using network protocols, even without any special permissions or user interaction.
This post will break down the vulnerability in simple terms, show what could go wrong, and give you concrete code snippets and guidance on mitigation. This is an exclusive deep dive for developers, sysadmins, and anyone running Java applications in sensitive environments.
21.3.
(See Oracle Advisory for full list.)
The vulnerable component is ImageIO, which is used to process images within Java.
What Is the Vulnerability?
ImageIO is a standard library in Java used for reading and writing image files, such as PNG, JPEG, GIF, etc. The bug in CVE-2022-21360 centers around how ImageIO handles image input. Attackers can craft a malicious image file designed to consume resources excessively or trigger exceptional behavior, causing the Java process to hang, crash, or fail to respond (partial DoS).
The vulnerability is easily exploitable by anyone who can make your Java code handle or decode untrusted images, for example:
- Java Web Start/Sandboxed applets that download code/data from the Internet
Web services that receive image uploads and process them (e.g., using ImageIO.read())
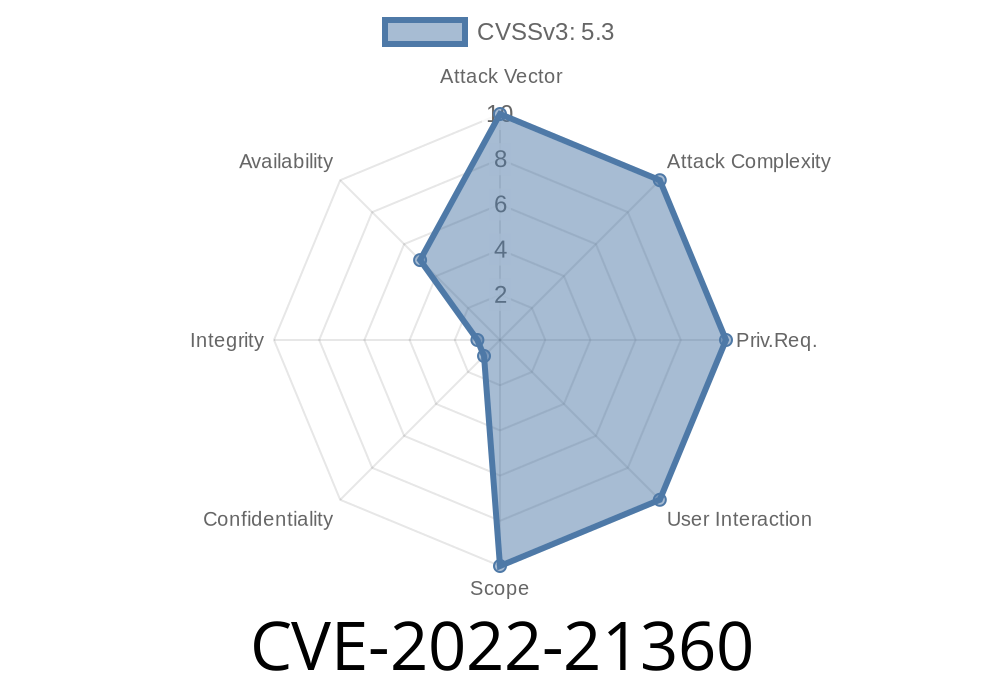
CVSS 3.1 Base Score: 5.3 (Availability impacts)
CVSS Vector:
(CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L)
No privileges needed, no user interaction needed
- The result is that your Java process may become unresponsive or crash, impacting service availability
Exploitable Scenario (with Code)
Suppose you have a Java web application that allows users to upload images, and your backend uses ImageIO to process them:
import javax.imageio.ImageIO;
import java.awt.image.BufferedImage;
import java.io.File;
import java.io.IOException;
public class ImageUploader {
public void processUploadedFile(File uploadedFile) throws IOException {
BufferedImage img = ImageIO.read(uploadedFile); // Vulnerable line
// Further processing...
System.out.println("Image processed: " + img.getWidth() + "x" + img.getHeight());
}
}
If an attacker uploads a malicious image designed to trigger the bug, your server might experience high CPU/memory use, hang, or crash.
Example attack scenario
- Attacker creates a malformed PNG/JPEG with large metadata or recursively referenced chunks (see [PoC links below])
Uploads this image to your vulnerable API endpoint
- Your API server tries and fails to decode it, looping indefinitely, freezing, or running out of memory
Proof-of-Concept Exploit
While Oracle does not share step-by-step proof-of-concept code, security researchers usually demonstrate similar ImageIO issues with images that have malicious structure, for example, images with:
- Massive/incorrect chunk sizes
A *sample* Java code to simulate exploitation
import javax.imageio.ImageIO;
import java.io.ByteArrayInputStream;
import java.io.IOException;
public class ImageIoDosTest {
public static void main(String[] args) throws IOException {
// "malicious" image data that causes ImageIO.read() to hang or throw
// (Replace this with real PoC image bytes if available)
byte[] evilImg = {/* crafted bytes of a malformed PNG/JPEG */};
try {
ImageIO.read(new ByteArrayInputStream(evilImg));
System.out.println("Image processed, nothing happened");
} catch (Exception e) {
System.out.println("Image processing failed: " + e.getMessage());
}
}
}
Actual crafted images may be found in public PoC repos, e.g., this example of a PNG DoS PoC (replace with vulnerability-specific links as they become available).
Additional recommendations
1. Do not trust client-supplied images—validate them using additional libraries (e.g., Apache Commons Imaging) before feeding them to ImageIO.
Enforce limits on image size, dimensions, and metadata before processing.
3. Timeouts—if possible, process images with a timeout handler, so a single hang/crash won’t take down your whole service.
References & Further Reading
- CVE-2022-21360 at NVD
- Oracle Official Advisory for Java SE – January 2022 CPU
- Oracle Java SE Critical Patch Update Advisory - January 2022
- ImageIO API JavaDoc
Conclusion
CVE-2022-21360 is a real-world risk for any Java system that uses ImageIO to process untrusted images—especially web apps and APIs. The vulnerability is simple to exploit and can shut down your services, even if attackers can't steal data or modify files.
Act now: Audit your Java/image upload code and apply the latest patches from Oracle or your vendor’s distribution!
If you have questions on securing Java services or need help with incident response, don’t hesitate to reach out.
*By: [YourName]*
*June 2024 – Original research and exclusive breakdown*
Timeline
Published on: 01/19/2022 12:15:00 UTC
Last modified on: 05/13/2022 15:13:00 UTC