WordPress is the world’s most popular free and open-source content management system (CMS), built with PHP and using MariaDB (or MySQL) as its database. Security is crucial for such a widely used platform, and sometimes weaknesses slip through. In late 2021, a critical security issue—CVE-2022-21664—was discovered that allowed potential attackers to inject malicious SQL queries through inadequate sanitization in one of WordPress’s core classes. If you run a WordPress site, it’s crucial you understand this issue, how it worked, and how WordPress fixed it in version 5.8.3 (with additional backports to much older versions).
Below is an exclusive, plain-English breakdown of CVE-2022-21664—including how the bug appeared in code, what the threat was, and why updating is the only safe path.
What Is CVE-2022-21664?
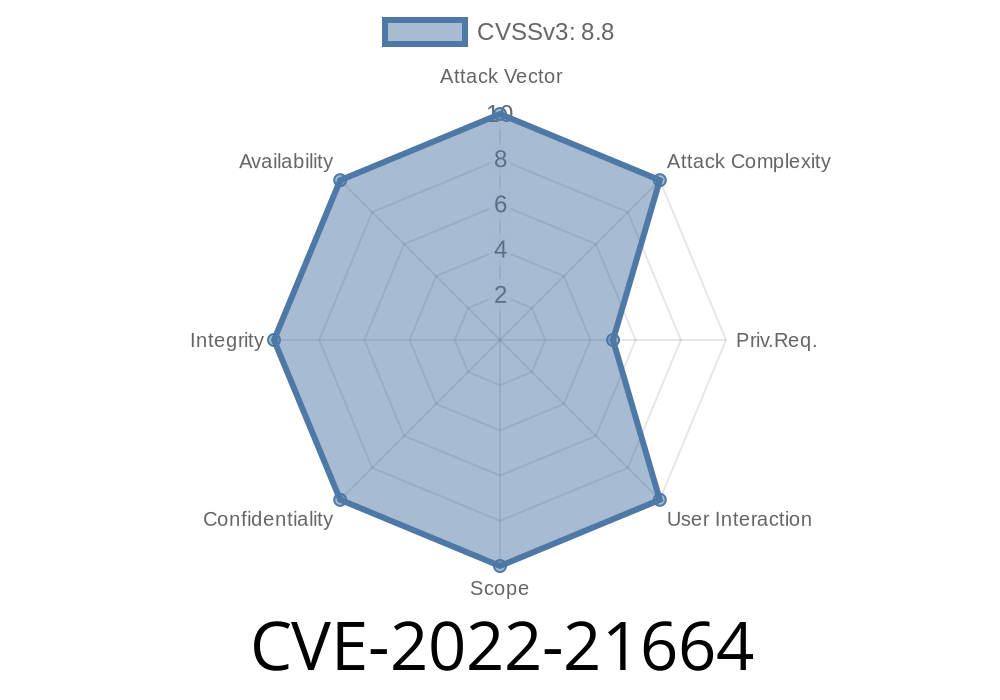
CVE-2022-21664 refers to a critical SQL Injection vulnerability that affected many versions of WordPress prior to v5.8.3. The root cause was a lack of proper sanitization of certain input parameters in a core WordPress class. This made it possible for an attacker, under specific conditions, to pass specially crafted user input that could be executed as part of SQL queries—potentially exposing or manipulating sensitive data stored in the website’s database.
Create new admin accounts for persistent control
WordPress’s reliance on its database for everything made this flaw very serious.
Vulnerable Code Example
To understand how this kind of issue happens, look at a simplified PHP example. Suppose WordPress had a function like:
function get_user_posts($user_id) {
global $wpdb;
// BAD: The $user_id is not sanitized here!
$query = "SELECT * FROM wp_posts WHERE post_author = $user_id";
return $wpdb->get_results($query);
}
If $user_id is taken directly from user input (e.g., a GET/POST parameter) without sanitization, an attacker could send something malicious as $user_id:
user_id=1 OR 1=1
Resulting query
SELECT * FROM wp_posts WHERE post_author = 1 OR 1=1
This would select all posts, not just those by user 1. More sophisticated attacks could even drop tables, extract admin accounts, and more.
The actual vulnerable code in WordPress was more complex and hidden inside a class, but the lack of proper escaping or sanitization of values inside SQL queries was the root problem.
Discovery, Impact, and Patch
The vulnerability was responsibly disclosed to the WordPress team, who quickly released WordPress version 5.8.3 with the necessary fixes (WordPress Security Release – 6 Jan 2022).
They also released patched updates all the way back to v4.1.34 for older sites that needed them
- WordPress 5.8.3 Security Release – WordPress.org
- CVE Details and Advisory
- GitHub Commit (fixes)
No workarounds are available: Only upgrading to a safe version addresses this issue.
Exploit Details
Though a public exploit for this specific flaw doesn’t exist (thanks to responsible disclosure and quick patches), a working attack would follow this logic:
1. Identify Input Path – Find a form, parameter, or API point which takes user input and passes it to the vulnerable class.
`
3. Trigger the Vulnerable Code – The vulnerable class, missing adequate sanitization, plugs raw input into an SQL query.
Suppose there’s an HTTP parameter author_id, and older WordPress code that fails to sanitize it
GET /?author_id=1+OR+1=1
This would fetch posts from all authors. If the code is more reckless
GET /?author_id=1;DROP+TABLE+wp_users
It might destroy your users table if multi-statement queries are enabled (rare but sometimes possible on misconfigured servers).
How WordPress Fixed It
The patch revised database query construction, ensuring all user-supplied input is sanitized either with prepared statements or by using strong escaping functions ($wpdb->prepare). For example:
// Proper use of parameterized query
$user_id = $_GET['user_id'] ?? ;
$query = $wpdb->prepare("SELECT * FROM wp_posts WHERE post_author = %d", $user_id);
$results = $wpdb->get_results($query);
This way, no input can ever be interpreted as SQL code.
Update WordPress, NOW!
- Turn on auto-updates in WordPress and keep your plugins/themes current.
- Check you’re on 5.8.3 or newer, or any of the corresponding patched releases (as far back as 4.1.34).
- There is NO other workaround—firewall rules, user permission tweaks, or plugin changes can’t close this hole.
Resources and References
- Official WordPress Security Release
- CVE-2022-21664 @ NVD
- WordPress Core Change Commit (GitHub)
- How to Enable Auto-Updates
Conclusion
CVE-2022-21664 shows how one small slip in input sanitizing can endanger millions of websites. If your WordPress isn’t updated, you could be one bad bug away from disaster. Upgrade immediately, leave auto-updates on, and always pay attention to security notices—it’s your best defense against the ever-evolving threats of the web.
Timeline
Published on: 01/06/2022 23:15:00 UTC
Last modified on: 04/12/2022 18:53:00 UTC