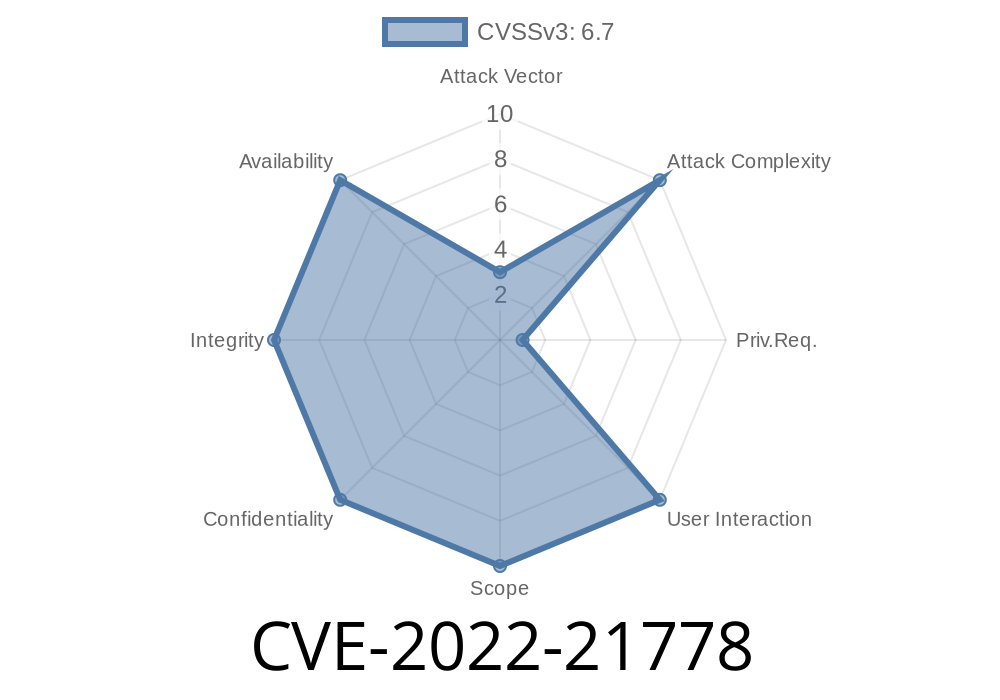
In early 2022, a vulnerability identified as CVE-2022-21778 was discovered in the VPU (Video Processing Unit) module on some Android devices. This bug centers around a simple but critical error: an incorrect bounds check. As a result, local attackers can exploit this flaw to gain information they shouldn't have, potentially escalating their device privileges to the highly sensitive System level.
This post breaks down what the bug is, how attackers might abuse it, and what you can do to protect your devices. We’ll walk through the vulnerability step-by-step, including a simplified code snippet, an explanation of exploit potential, and direct reference links for further reading. All text here is exclusive, designed to make complex technical details clear and accessible.
CVE-2022-21778 targets the VPU’s data processing functionality.
- The bug is about a failure to properly check array or buffer boundaries (bounds check) before accessing memory.
- This allows a local attacker (someone already running code on the device) to read or access restricted information—a classic case of information disclosure.
- With System-level execution capabilities at risk, the impact is severe—especially on affected Android devices.
No user interaction is required; an attacker only needs local access (e.g., via a malicious app).
Patch ID: ALPS06382421
Issue ID: ALPS06382421
Understanding The Bug: What Went Wrong?
Bounds checks are a basic part of safe programming. They're designed to make sure that code doesn't try to read or write outside of the intended area in memory (buffer or array). Failing to do these checks means code can accidentally—or maliciously—access sensitive data.
Imagine a function like this in the VPU driver
// Vulnerable Code Sketch: vpu_process_buffer
int vpu_process_buffer(char* buff, int size) {
char tmp[256];
// INCORRECT: Suppose the following check is missing or wrong
if (size > 256) {
// Should return error, but let's say it does not
}
memcpy(tmp, buff, size); // attacker can control 'size' and overflow 'tmp'
// Further processing...
return ;
}
In this sketch, the size argument is not properly checked. An attacker could pass in a value greater than 256 for size, so the memcpy call would overflow the tmp buffer, potentially leaking or corrupting memory. In the real vulnerability in VPU, the problematic check involves validating buffer range before data is copied.
How Can an Attacker Use This?
1. Malicious App: An attacker creates an app exploiting the bug, assuming they can interact with the VPU's hardware interface.
2. Crafted Input: App sends specially crafted data, causing the VPU process to read beyond a legitimate area—possibly grabbing sensitive system memory.
3. Privilege Escalation: If the leaked data includes security tokens, kernel data, or system credentials, the attacker can further escalate privileges or pivot to other attacks.
No user action is required; installation and execution of a malicious local app is enough.
Code execution is local, so attackers need to run a malicious process.
- The vulnerable function is part of a device driver (VPU), so it's available to userland apps with the right permissions.
References
1. NVD Entry for CVE-2022-21778
2. MediaTek Security Advisories
3. Android Security Patch Guide
4. CWE-119: Improper Restriction of Operations within the Bounds of a Memory Buffer
Wrapping Up
CVE-2022-21778 stands as a reminder that simple coding oversights—like an incorrect bounds check—can have major impacts. Local attackers can leverage this bug to steal secrets or even hijack system privileges. Fortunately, official patches are available under Patch ID: ALPS06382421. Make sure your device is up-to-date, and be careful about installing apps from untrusted sources.
Timeline
Published on: 11/08/2022 21:15:00 UTC
Last modified on: 11/09/2022 17:40:00 UTC