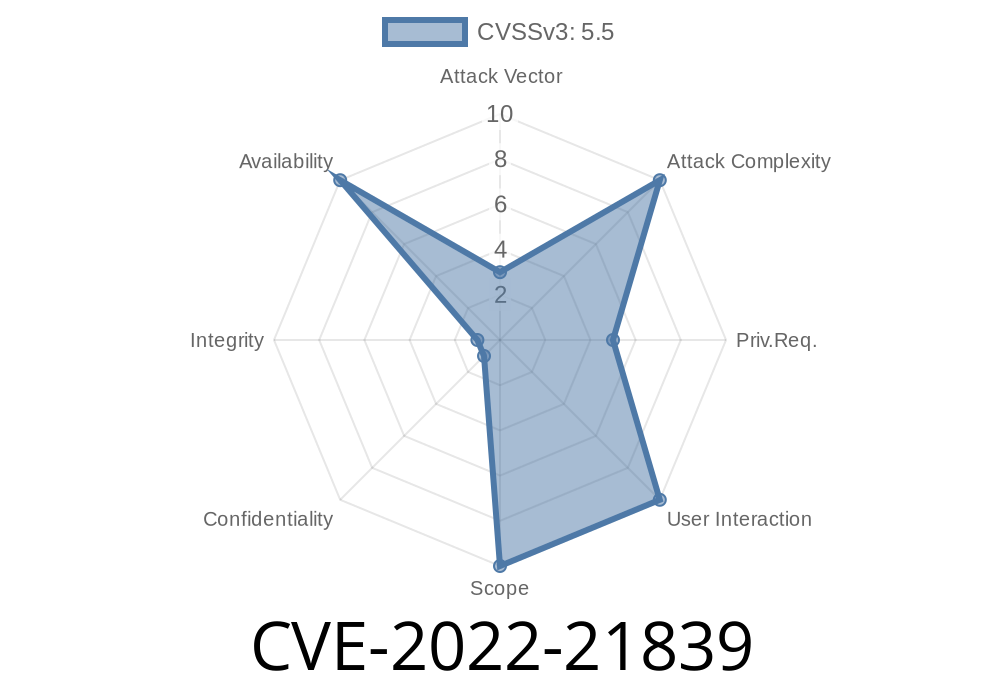
*In January 2022, Microsoft published a security update for a vulnerability titled CVE-2022-21839, which relates to Windows Event Tracing (ETW) and discretionary access control lists (DACL). This Denial of Service (DoS) vulnerability, though not the most widely publicized, could let malicious users or programs bring down critical logging functions or even impact host stability. If you’re responsible for systems running Windows, it’s important to understand how CVE-2022-21839 works, what the risks are, and what you can do to defend your machines.*
What is Windows Event Tracing?
Windows Event Tracing (ETW) is a built-in system that helps administrators and programs record diagnostic, performance, and security logs. System components use ETW to emit events, which can be collected by applications with proper privileges. Event Trace Sessions are protected with DACLs so only authorized users can create, access, or modify them.
What’s the Problem with CVE-2022-21839?
This CVE is about a Denial of Service flaw in how Windows applies DACLs to Event Tracing objects. An authenticated user with limited system rights could mess with ETW trace sessions, causing a Denial of Service for everyone else—including system components. This could halt or degrade critical system monitoring, and in some cases, hang or crash system services.
How the Exploit Works
The vulnerability exists because Windows fails to correctly check permissions when updating or setting DACLs on ETW sessions. If someone sets a restrictive DACL—one that allows only themselves or excludes everyone—they can block access to that session for other users and programs, including SYSTEM services.
Example Code Snippet: Setting a Deny-Only DACL on an ETW Session
Here’s a basic outline in C that shows how someone could restrict access to an ETW session. This example assumes the attacker has access to the trace session handle.
#include <windows.h>
#include <evntcons.h>
#include <sddl.h>
void SetRestrictiveDACL(HANDLE sessionHandle) {
// SDDL D: owner only, blocks everyone else
LPCWSTR sddl = L"D:PAI(A;;GA;;;SY)";
PSECURITY_DESCRIPTOR pSD = NULL;
if (ConvertStringSecurityDescriptorToSecurityDescriptorW(sddl, SDDL_REVISION_1, &pSD, NULL)) {
SetKernelObjectSecurity(sessionHandle, DACL_SECURITY_INFORMATION, pSD);
LocalFree(pSD);
}
}
int main() {
// ... code to start or obtain ETW session handle ...
HANDLE etwHandle = ...;
SetRestrictiveDACL(etwHandle);
}
*This code sets a DACL that only allows SYSTEM access and denies everyone else—blocking any further event tracing by unauthorized users or processes, including those that should have access.*
Interrupt regular ETW consumers, crashing apps or causing system instability.
In certain configurations, this could snowball into a more serious availability or security problem, especially in remote desktop or terminal server environments.
Microsoft patched this on January 11, 2022—see the official advisory here
- Microsoft Security Guide (MSRC)
- Patch details for various Windows versions
What you should do
1. Update your systems—Install the January 2022 security updates or later on all Windows machines.
2. Limit user access—Don’t give unnecessary local logins or group memberships to sensitive hosts.
Final Thoughts
CVE-2022-21839 is a reminder that local users can break things in subtle ways, especially when system APIs aren’t clear about access checks. If attackers can stop your monitoring tools, they can open a pathway to further compromise—or, at minimum, cover their tracks.
Stay updated, understand your system’s logging security, and always keep an eye on the principle of least privilege.
References
- CVE-2022-21839 Security Advisory – Microsoft
- US-CERT Vulnerability Note VU#200936
- Microsoft Event Tracing (official dev docs)
- Microsoft Patch Tuesday, January 2022
*If you enjoyed this breakdown, share it forward—and don’t forget to patch your systems!*
Timeline
Published on: 01/11/2022 21:15:00 UTC
Last modified on: 01/14/2022 03:37:00 UTC