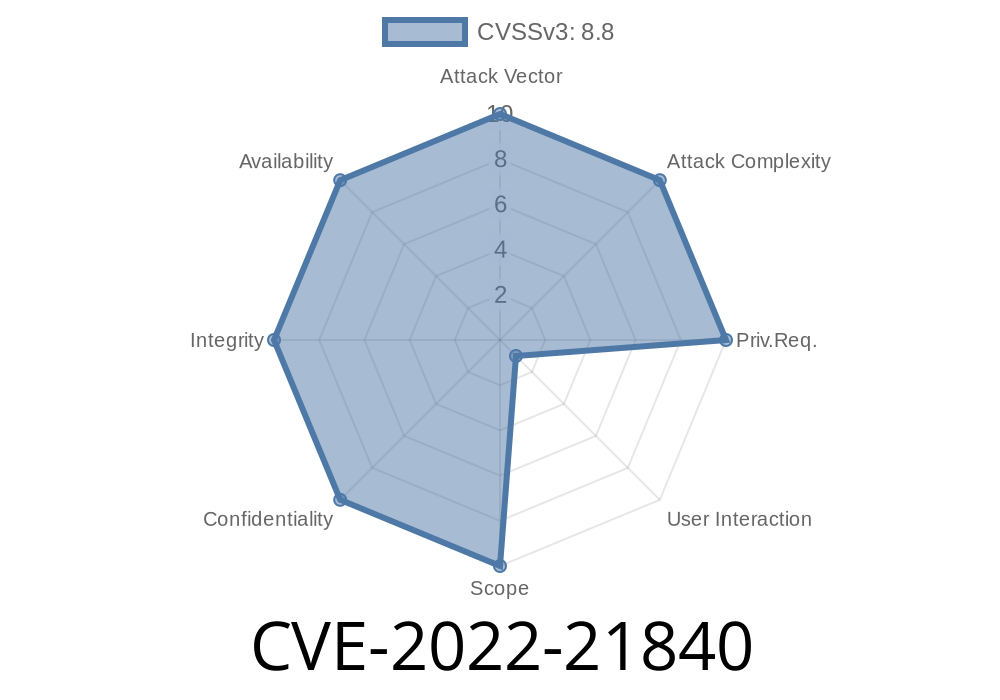
In January 2022, Microsoft patched a critical Remote Code Execution (RCE) vulnerability tracked as CVE-2022-21840. This security flaw affected Microsoft Office and could let hackers execute malicious code on a victim’s computer just by tricking them into opening a specially crafted file.
In this long read, I’ll explain what CVE-2022-21840 is, how attackers could exploit it, and how you can protect yourself. We’ll keep it simple, break down how it works, show a code-like example, and link to official resources.
What is CVE-2022-21840?
CVE-2022-21840 is a bug in how Microsoft Office handles certain files. This bug could allow an attacker to run almost any command or program on your system without your knowledge. All they need is for you to open a dangerous file, often delivered by email or download.
Affected products include:
Office Web Apps (in some cases)
Microsoft’s official advisory:
- Microsoft Security Guidance: CVE-2022-21840
- Microsoft Patch Tuesday January 2022
How Does the Exploit Work?
At the core, the vulnerability is found in the way Office parses a specific Excel file format (.xls, specifically). By crafting the file in a certain way—poking at Office’s under-the-hood “OLE” (Object Linking and Embedding) structures—an attacker can trigger a memory corruption that lets them execute rogue code.
The attacker’s payload (malicious program) runs silently on the victim’s system.
Unlike some exploits, this one doesn’t require tricking a user into enabling macros or clicking “Enable Content.” Just opening the file is enough.
Code Snippet: What Does a Malicious File Look Like?
Let’s look at a simplified pseudo-code to understand the issue. (Note: For safety, this is not real exploit code.)
What the attacker does
# pseudo-code: create an Excel file containing a malformed structure
def create_malicious_excel():
header = b'\xD\xCF\x11\xE' # OLE start
payload = b'\x00' * 512 # Filler
corrupted_part = b'\xFF' * 32 # This causes Excel’s parser to mess up
exploit_code = b'\x90' * 100 # Pretend code that would give attacker control
with open('exploit.xls', 'wb') as f:
f.write(header)
f.write(payload)
f.write(corrupted_part)
f.write(exploit_code)
create_malicious_excel()
In the real-world exploit, the attacker carefully crafts the inner structure to control how Excel loads certain objects, causing Excel to jump and execute attacker-controlled bytes.
The victim opens the Excel sheet; payload executes instantly.
A responsible researcher published a safe “proof-of-concept” for this bug:
- GitHub - CVE-2022-21840-POC (educational only)
You open invoice.xls
- Nothing looks wrong, but behind the scenes, the attacker's code runs, stealing files or installing malware.
Microsoft fixed this bug in January 2022.
Install the update from Windows Update.
Links & References
- Official Microsoft Advisory: CVE-2022-21840
- NIST NVD CVE Entry
- GitHub Proof of Concept
Final Thoughts
CVE-2022-21840 is a perfect example of why keeping software updated is so important. Attackers love Office vulnerabilities because they blend in with regular business, and users often aren’t suspicious. Stay vigilant—patch early, and be careful what you open.
If you want to dig deeper technically, check the links above. Stay safe and keep your systems updated!
Timeline
Published on: 01/11/2022 21:15:00 UTC
Last modified on: 01/14/2022 16:45:00 UTC