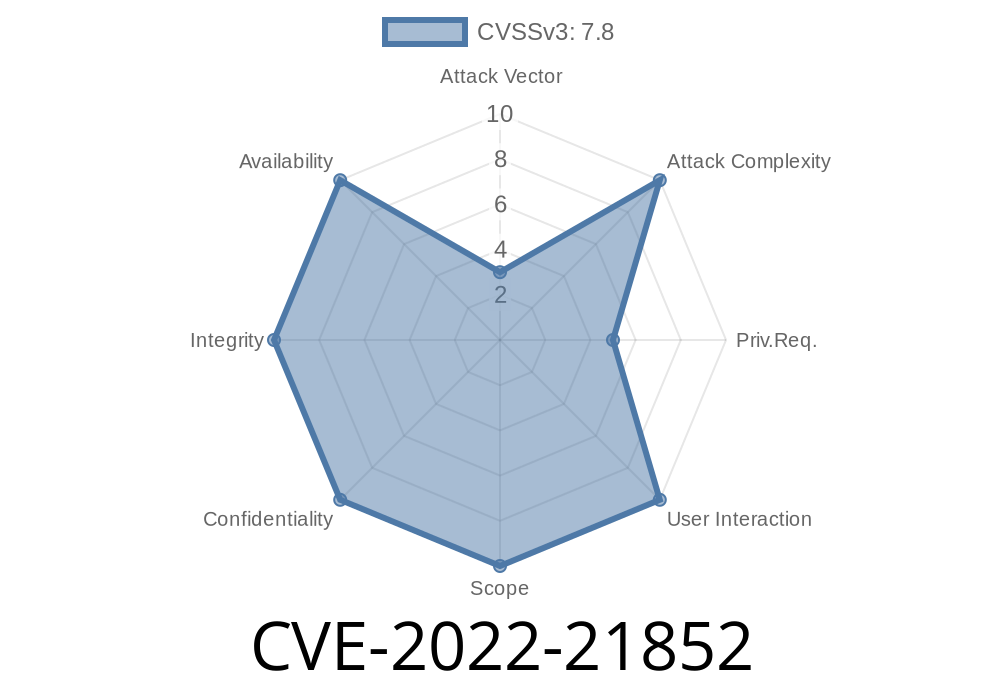
In January 2022, Microsoft disclosed CVE-2022-21852, a critical elevation of privilege vulnerability found in the Windows DWM Core Library. While it didn't attract as much attention as some other vulnerabilities, this CVE poses real risks—especially to shared systems and machines not regularly updated.
This post explores what makes CVE-2022-21852 unique (distinct from siblings like CVE-2022-21896 and CVE-2022-21902), how attackers can exploit it, and what you should do to protect your systems.
What is the Windows DWM Core Library?
DWM stands for *Desktop Window Manager*. It's a Windows system process (dwm.exe) responsible for rendering windows, managing visual effects, and handling desktop composition. The DWM Core Library lies at the heart of this process, running with more privileges than a normal user.
Since DWM touches almost every desktop session, a vulnerability here can let attackers leap from ordinary user access to complete system control.
Why This Is Dangerous
If someone can trick the DWM Core Library into running their code—or accessing something it shouldn't—they can jump from a regular user to SYSTEM. On Windows, SYSTEM is as powerful as it gets.
Differences from Other DWM Vulnerabilities
- CVE-2022-21896 and CVE-2022-21902 are separate bugs. Each targets a different part of DWM's codebase or has a different method of exploitation. It’s important not to confuse these—CVE-2022-21852 exploits a specific code path unique from these two.
Under the Hood
The actual issue boils down to improper handling of certain requests sent to DWM. When a local user interacts with certain graphics APIs or desktop features, there's a window (pun intended) to feed malformed data into DWM, causing it to overwrite memory or execute code it shouldn't.
Example Attack Steps
> Disclaimer: No real-world "weaponized" code is shared here. This is a simplified demonstration for educational purposes only.
Exploiting DWM through Named Pipes
Many Windows interfaces use named pipes for inter-process communication. Suppose DWM exposes a pipe for legitimate use:
Here’s *pseudo code* for how an attacker might poke at the DWM pipes (for research purposes)
import win32pipe, win32file
pipe_name = r'\\.\pipe\DWMCorePipe' # Hypothetical name
try:
# Connect to DWM's pipe
handle = win32file.CreateFile(
pipe_name,
win32file.GENERIC_READ | win32file.GENERIC_WRITE,
, None, win32file.OPEN_EXISTING, , None
)
# Craft a malicious request (oversized or unexpected input)
payload = b"A" * 1024 # Example overflow data
win32file.WriteFile(handle, payload)
except Exception as e:
print("Error:", e)
> Note: The actual pipe name and payload structure would depend on private details of Windows internals. Researchers reverse engineered specifics using public memory dumps and system tracing tools.
Original References
- Microsoft Security Update Guide: CVE-2022-21852
- Microsoft Patch Tuesday January 2022
- NIST NVD Entry
What Could Attackers Do?
- Escalate Privileges: Launch admin tools, change account passwords, or install persistent malware.
Are There Reports in the Wild?
At publication, no public exploits were confirmed, but Windows privilege escalation bugs are a favorite "second step" for attackers already on a machine via phishing or malware.
Apply Microsoft Security Updates
Always keep Windows up-to-date. The fix for CVE-2022-21852 shipped in January 2022. See Microsoft’s guide for the latest patches.
Limit Local User Access
Only trusted users should have access to your machines. Privilege escalation bugs need an initial foothold.
Conclusion
CVE-2022-21852 demonstrates how deep, system-level bugs in Windows features can lead directly to total compromise—if an attacker gets the right opportunity. It's a classic case where just having an account on a system could be enough for a motivated hacker to take over.
Patch early, patch often, and keep an eye out for DWM and graphics library bugs—they’re increasingly attractive targets.
*If you found this write-up helpful, consider sharing it or checking out Microsoft’s official guidance for more details on patching and mitigation.*
Timeline
Published on: 01/11/2022 21:15:00 UTC
Last modified on: 05/23/2022 17:29:00 UTC