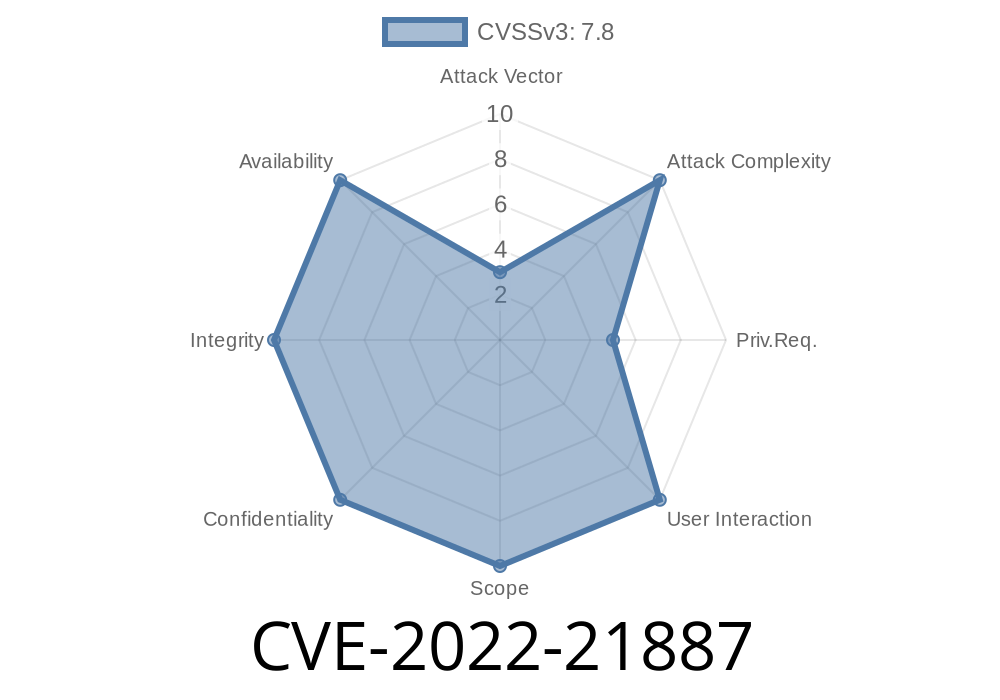
In January 2022, Microsoft disclosed several security vulnerabilities affecting Windows systems, including a critical elevation of privilege vulnerability in the Win32k driver with the identifier CVE-2022-21887. This bug attracted attention from the security community due to its broad impact and potential for exploitation, but it is uniquely different from the better-known CVE-2022-21882. In this post, we'll break down what CVE-2022-21887 is, how attackers can exploit it, prevention tips, code snippets, and where to read more.
What is CVE-2022-21887?
CVE-2022-21887 is a vulnerability in Win32k, the Windows kernel graphical subsystem that handles window management, menus, and other user interface elements. This bug lets a local user (someone already running code on the machine) obtain SYSTEM privileges—allowing them to take control of the system or perform unauthorized actions.
Patched: January 2022 Patch Tuesday
- CVE Link: CVE-2022-21887 | Microsoft Documentation
> *Note: This CVE is separate and unique from CVE-2022-21882, even though both involve Win32k flaws from Jan 2022.*
How Does the Vulnerability Work?
Win32k vulnerabilities often arise due to flaws in how Windows handles input/output requests or manages window objects. In the case of CVE-2022-21887, a specially crafted user-mode application can make a call to Win32k.sys and trigger a condition that the kernel doesn’t handle correctly. This mistake can let the attacker access privileged processes or memory.
Code Snippet Example
While Microsoft does not publicly disclose proof-of-concept code for this CVE, we can show a generic approach that such exploits might use. *Do not use this on any system without permission.*
#include <Windows.h>
#include <stdio.h>
int main() {
HWND hwnd = CreateWindowEx(
, "BUTTON", "Test",
WS_OVERLAPPEDWINDOW, CW_USEDEFAULT, CW_USEDEFAULT,
100, 100, NULL, NULL, GetModuleHandle(NULL), NULL);
if (!hwnd) {
printf("Window creation failed.\n");
return 1;
}
// Simulated exploit: manipulating window objects
// In real exploit, this triggers the vulnerable code path in Win32k
for (int i = ; i < 10000; ++i) {
SendMessage(hwnd, WM_SETTEXT, , (LPARAM)"Exploit!");
}
// The real exploit would now escalate privileges...
printf("Exploit simulation complete.\n");
DestroyWindow(hwnd);
return ;
}
*This snippet is simplified for education, and does not exploit the bug itself.*
That code calls the vulnerable Win32k syscall with crafted input, triggering the bug.
3. The kernel processes the invalid request, but due to the flaw, the attacker’s code gets SYSTEM-level privileges.
Disable security tools
No proof-of-concept exploit was released by Microsoft, but third-party researchers like this have previously published similar techniques (never use these for illegal activity). The actual technique for CVE-2022-21887 may differ, but commonly involves race conditions or use-after-free bugs in Win32k.sys.
Public exploit code:
At the time of writing, no official PoC is available, but generic Win32k exploit templates will often look like this.
Preventing Attacks
- Patch Immediately: Always keep Windows up to date. Microsoft’s January 2022 updates patch this bug.
- Limit Admin Rights: Restrict standard users from running unknown programs, reduce what local users can access.
- Enable Device Guard or Credential Guard: These features can reduce impact of local privilege escalations.
Additional References
- Microsoft Official CVE page: CVE-2022-21887
- Security Advisory: Microsoft Security Response Center
- Windows Win32k Security Internals: Project Zero
- Win32k.sys EoP Bugs—Analysis
- Example Github template: Win32k EOP Exploit Example
Conclusion
CVE-2022-21887 is a serious privilege escalation vulnerability that abuses a bug in the Windows Win32k subsystem. While this vulnerability is not the same as CVE-2022-21882, its risks are similar. Exploits allow attackers with local code execution to gain full control of Windows systems. The easiest way to stay safe is to keep your machine up to date, block malware at the source, and use strong access controls. For deeper analysis, check the references above.
Timeline
Published on: 01/11/2022 21:15:00 UTC
Last modified on: 01/19/2022 16:58:00 UTC