---
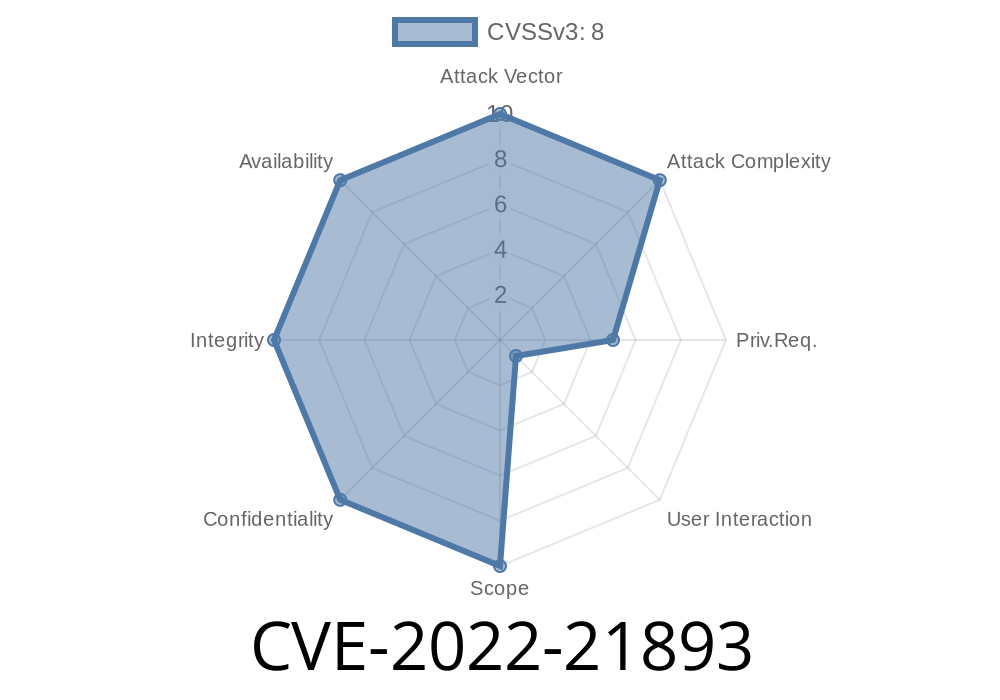
In early 2022, cybersecurity experts and Microsoft revealed a serious flaw in Remote Desktop Protocol—a technology used by millions worldwide to access and manage Windows computers remotely. This vulnerability, tracked as CVE-2022-21893, could allow a remote attacker to run malicious code on your machine—possibly taking total control. This article explains what CVE-2022-21893 is, how an exploit could work, and what you should do to stay safe. The goal is to give you clear, practical info, with code snippets for technical readers, and direct reference links to learn more.
What is CVE-2022-21893?
CVE-2022-21893 is a _Remote Code Execution_ (RCE) vulnerability in Microsoft’s Remote Desktop Protocol (RDP). RDP is basically the standard way Windows systems allow remote logins and desktop sharing. This vulnerability affects Windows Servers and Desktops that have RDP enabled.
The flaw is due to a logic error in how RDP processes specially crafted requests. If an attacker sends the right kind of request, they could execute arbitrary code _before_ any authentication takes place. In other words, the attacker wouldn’t need a password or valid account; just the ability to reach your RDP port over the network.
Microsoft Security Update Guide:
CVE-2022-21893 | Windows Remote Desktop Protocol Remote Code Execution Vulnerability
NVD CVE Record:
How Does This Vulnerability Work?
An attacker finds a server with RDP exposed (usually port 3389/TCP). By sending a specially-crafted sequence of packets, the attacker exploits the bug in the RDP service.
Once exploited, the attacker’s code runs with the same high privileges as the RDP service itself—often _SYSTEM_, giving them full control.
Exploit Delivery:
They send crafted data that triggers the vulnerable code path—often using a script or exploit tool.
System Takeover:
The attacker gains remote shell (like command prompt or powershell) and can steal data, install ransomware, or pivot deeper into the network.
Example Code Snippet: Simple RDP Scanner
Below is a sample Python snippet that scans for open RDP services. This is not an exploit; it’s just to help understand how attackers find targets.
import socket
def scan_rdp(ip, port=3389, timeout=3):
try:
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(timeout)
s.connect((ip, port))
print(f"RDP open on {ip}:{port}")
except Exception:
print(f"No RDP on {ip}:{port}")
finally:
s.close()
# Example usage:
scan_rdp("192.168.1.10")
Warning: Scanning systems you don’t own or have permission to test is illegal!
Exploit Details in Action
While Microsoft has not published full exploit code (to prevent abuse), several PoC (Proof of Concept) scripts circulated in private forums. The general idea is to create an RDP packet that breaks protocol handling and triggers arbitrary code execution.
Here’s a _conceptual_ sample, not an actual exploit
import socket
def send_malicious_rdp_packet(target_ip, target_port):
# Crafted packet that triggers the vulnerability (dummy data shown)
malicious_packet = b"\x03\x00\x00\x13\xe\xe\x00\x00..." # Example
with socket.create_connection((target_ip, target_port)) as s:
s.sendall(malicious_packet)
# If vulnerable, code execution may occur (attacker-side payload runs)
send_malicious_rdp_packet('TARGET_IP', 3389)
Important: Actual payloads are more complex and tailored based on OS version and memory layout.
Further Technical Reads & Exploit Analysis
- ZDI: Technical Analysis on CVE-2022-21893 RDP RCE
- Rapid7 Metasploit Blog (if/when module released)
Real-World Impacts
- Wormable: Like earlier RDP vulnerabilities (e.g., BlueKeep), this bug could be exploited to build self-spreading malware.
Ransomware: Many ransomware crews hunt for RDP, making this flaw highly valuable.
- Cloud risk: Exposed cloud VMs (Azure, AWS, Google Cloud) are at special risk if RDP is open to the Internet.
Microsoft fixed this vulnerability in the January 2022 Patch Tuesday updates.
- Download Security Updates (search your Windows version)
In Summary
CVE-2022-21893 is a dangerous bug that puts Windows systems with exposed RDP at risk of total compromise. Attackers don’t need a password; just access to port 3389. Patching is easy and should be done ASAP. Restricting RDP access is a vital second layer of defense.
References
- Microsoft Security Advisory for CVE-2022-21893
- NVD CVE-2022-21893 Entry
- Zero Day Initiative Post
If you liked this post or have questions, feel free to leave a comment or reach out to your IT/security support!
Timeline
Published on: 01/11/2022 21:15:00 UTC
Last modified on: 05/23/2022 17:29:00 UTC