This vulnerability has been assigned Common Vulnerabilities and Exposures classification of CVE-2022. This is a spooler elevation of privilege vulnerability. With attacker’s network connection, an attacker can send malicious print jobs to a vulnerable Windows 7/8/10 computer, and then that vulnerable computer will execute the malicious print jobs without any confirmation from the user, which will lead to the elevation of privilege on that vulnerable computer. By default, Windows does not provide any printing function. Users have to install a printing driver and then use print command to print a document to a printer. If a user does not install a printing driver on his/her computer, or if a user does not have a printer connected to his/her computer, then a vulnerable computer is not able to receive or send a print job, which means that a vulnerable computer can receive a malicious print job and then execute it without the confirmation from the user.
Vulnerable Packages and Systems
Vulnerable software packages:
Windows 7 SP1 and later versions; Windows 8.1 and later versions; Windows 10.
Systems affected:
All computers running Windows 7/8/10, with or without any printing driver installed.
Vulnerability overview
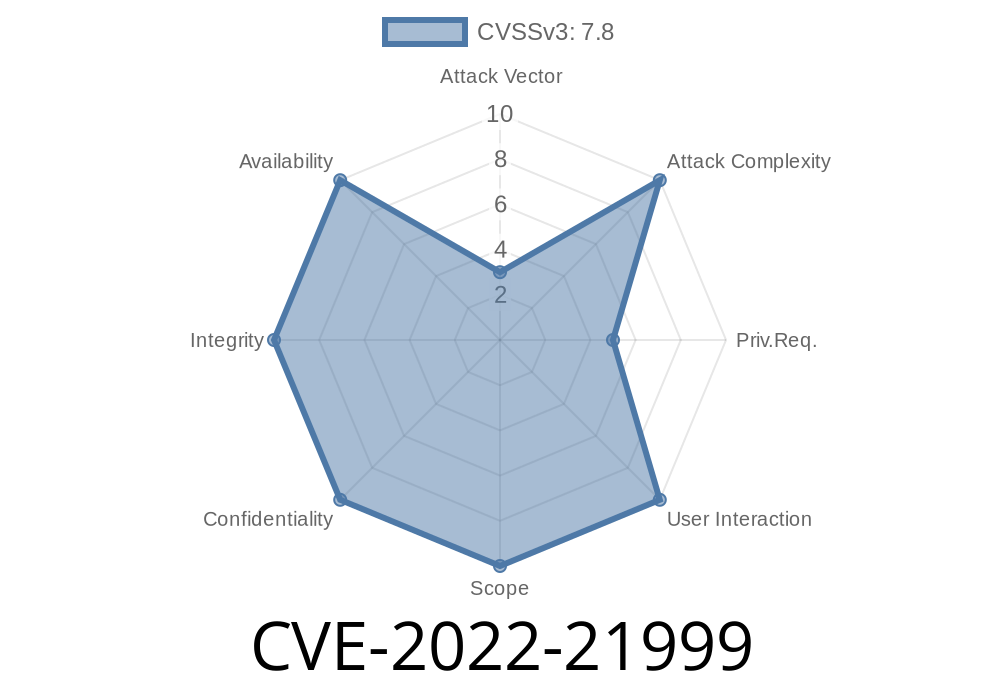
This vulnerability has been described in CVE-2022-21999, which is commonly known as "Elevation of Privilege Vulnerability in Windows Print Spooler". A vulnerable computer, which does not have a printer connected to it and does not have a printing device installed on their computer, will be able to receive malicious print jobs via the Internet and then execute them without any confirmation from the user. Such a vulnerability allows an attacker to gain control of a vulnerable computer.
A malicious print job can be sent by an attacker’s network connection without any confirmation from the user. So technically speaking, there is no confirmation needed for an attack. The vulnerability is found in windows print spooler service which executes when users try to send a print job.
Therefore, since there is no confirmation needed for an attack and since the vulnerability is found in windows print spooler service, it can lead to elevation of privilege on vulnerable computers that do not have printers attached or do not have printing devices attached
Vulnerability discovery and research
The vulnerability discovered was independent of the number of print jobs being sent. To exploit this vulnerability, an attacker only needs to send one malicious print job and then the vulnerable computer will execute it without any confirmation from the user. By default, Windows does not provide any printing function. Users have to install a printing driver and then use print command to print a document to a printer. If a user does not install a printing driver on his/her computer, or if a user does not have a printer connected to his/her computer, then a vulnerable computer is not able to receive or send a print job, which means that a vulnerable computer can receive a malicious print job and then execute it without the confirmation from the user.
Vulnerability discovery and exploitation
The vulnerability is caused by the spooler service of Windows. The spooler service is a process that manages print jobs. A malicious print job will be sent to a vulnerable computer, where this malicious print job will be executed by the vulnerable computer without confirmation from the user.
An attacker can exploit this vulnerability to send malicious print jobs via UNC path or IPP path to a vulnerable computer, and then that vulnerable computer will execute the malicious print jobs without any confirmation from the user, which will lead to elevation of privilege on that vulnerable computer.
Vulnerability details
This vulnerability can be exploited by sending a malicious print job to a vulnerable computer. The user does not have to install any printing driver on the computer in order for this vulnerability to be exploited. This vulnerability can be exploited if a user sends a fake print job with an executable file as an attachment. For example, if the user sends an email with a malicious Word document attached, then when the user opens that Word document, it will open and execute automatically without any confirmation from the user.
Timeline
Published on: 02/09/2022 17:15:00 UTC
Last modified on: 05/26/2022 20:30:00 UTC