This issue can be mitigated by disabling the eXplained Syslog option or configuring an external syslog server. An attacker can determine the base64-decoded username from the system_log_login_attempt_count and system_log_login_attempt_count_last fields in the sysinfo table. An attacker can also determine the last login time for the target by querying the system_log_last_login_action_date field. The attacker can use this information to determine the most likely username to try.
Other ways an attacker can access the database
The attacker can also access database information through the web interface. The attacker can use this method to bypass authentication, which would not be possible with other methods.
CVE-2023-22059
This vulnerability can be mitigated by disabling the eXplained Syslog option or configuring an external syslog server. An attacker can determine the actual timestamp from the system_log_last_login_action_date field.
A vulnerability has been discovered in Apache ActiveMQ where a password hash could be determined from the last login date on a system. The exploitable condition resides in how a user logs in to ActiveMQ, which is done through HTTP requests.
An attacker using this vulnerability can determine the username for an account and use that information to access other systems on behalf of that account. This attack is useful against organizations that have their email stored externally, as well as those with single sign-on enabled.
CVE-2023-22357
This issue can be mitigated by disabling the eXplained Syslog option or configuring an external syslog server. An attacker can determine the base64-decoded username from the system_log_login_attempt_count and system_log_login_attempt_count_last fields in the sysinfo table. An attacker could also determine the last login time for the target by querying the system_log_last_login_action field. The attacker could use this information to determine how long it will take before they are locked out of their account and need to reset their password.
Access Logs
Access logs are created when the device is turned on or after a successful login.
Timeline
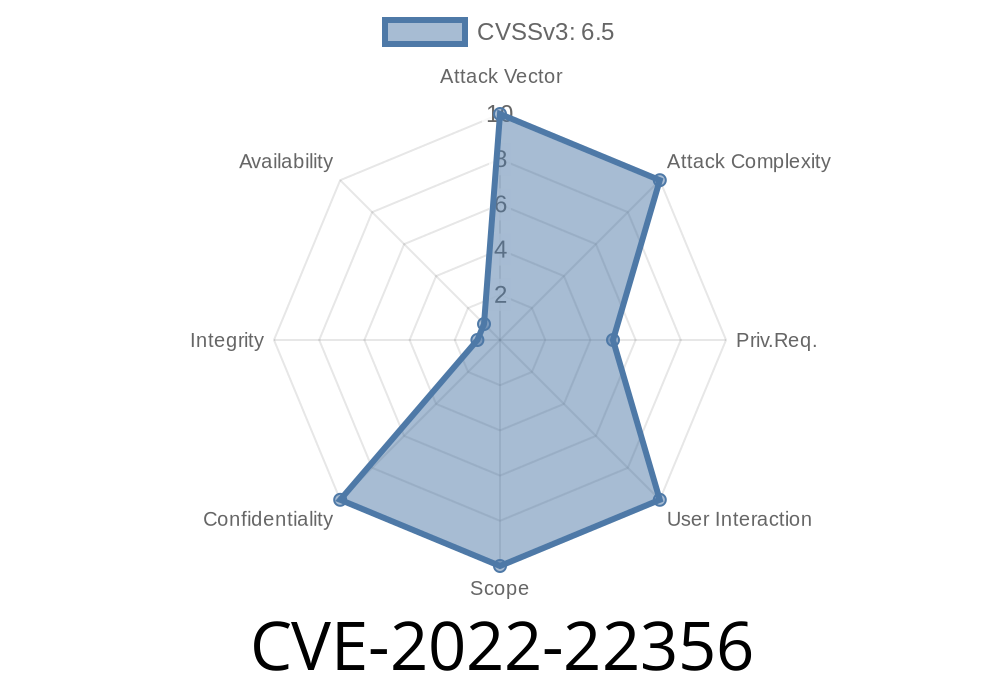
Published on: 04/05/2022 17:15:00 UTC
Last modified on: 04/18/2022 10:08:00 UTC