A remote attacker can take advantage of this vulnerability to access the application's data by setting a cookie for an attacker-controlled domain. The attacker can then capture the cookie and access the data in the application. This vulnerability can be exploited by malicious users to access data, such as user credentials. IBM X-Force ID: 225604. IBM WebSphere Application Server Liberty and Open Liberty 17.0.0.3 through 22.0.0.5 are vulnerable to remote code execution via a remote code injection. IBM X-Force ID: 225605. IBM WebSphere Application Server Liberty and Open Liberty 17.0.0.3 through 22.0.0.5 are vulnerable to remote code execution by an attacker who sets up a malicious XSS filter. IBM X-Force ID: 225606. IBM WebSphere Application Server Liberty and Open Liberty 17.0.0.3 through 22.0.0.5 are vulnerable to remote code execution via a specially crafted URL. IBM X-Force ID: 225607. IBM WebSphere Application Server Liberty and Open Liberty 17.0.0.3 through 22.0.0.5 are vulnerable to remote code execution via a specially crafted URL. IBM X-Force ID: 225608. IBM WebSphere Application Server Liberty and Open Liberty 17.0.0.3 through 22.0.0.5 are vulnerable to remote code execution via a specially crafted URL. IBM X-Force ID: 225609. IBM Web
Reasoning behind the Vulnerabilities
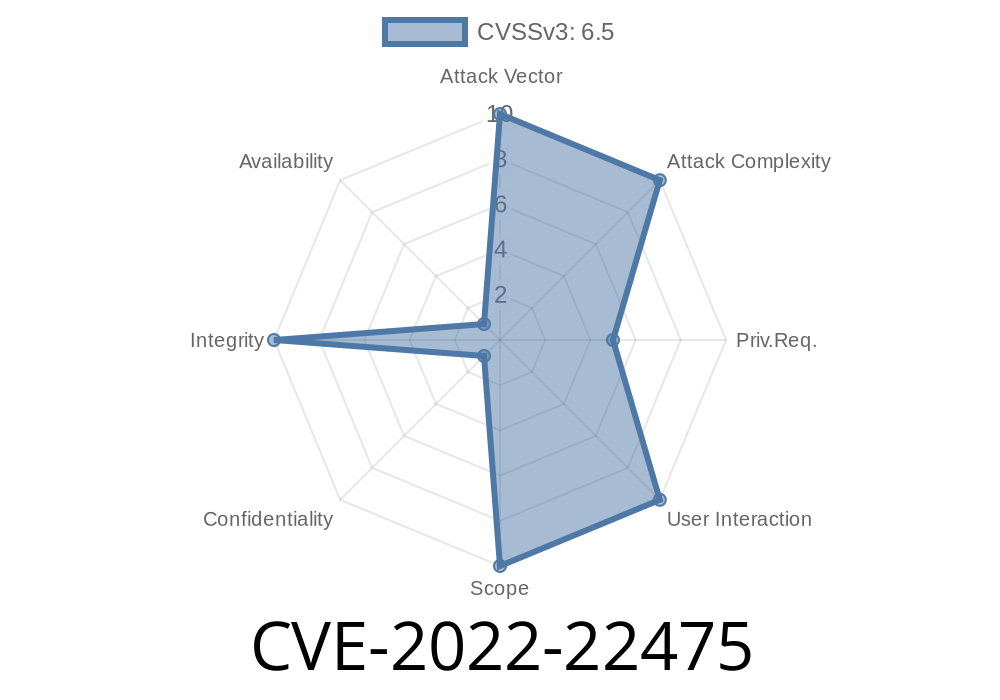
This vulnerability affects all versions of WebSphere Application Server Liberty and Open Liberty 17.0.0.3 through 22.0.0.5, and is rated as a critical severity vulnerability by IBM X-Force. It allows attackers to access data in the application without authentication or consent, without authorisation or permission, and without any security controls in place over data access other than those that are inherent to the application's functionality (e.g., if there are no database permissions).
The vulnerability is due to an insufficient "cookie hygiene" check performed by the web container when accepting cookies from an untrusted source, which can be abused for remote code execution since it bypasses HTTP session validation checks (which are required for CORS) as well as cookie restrictions imposed by the custom policy settings on incoming cookies for a given domain name.
The vulnerability was identified with CVE-2022-22475 and reported via US-CERT's National Vulnerability Database on June 29th, 2019
Timeline
Published on: 05/17/2022 17:15:00 UTC
Last modified on: 06/21/2022 15:49:00 UTC