An attacker could take advantage of this by sending the victim a link to a website with a photo that appears to be from their own device. This issue did not exist in previous versions of iOS and iPadOS. An attacker could capture a screenshot of the lock screen and receive the device’s passcode information. The previous versions of iOS and iPadOS did not store the passcode information anywhere on the device. An attacker could access this information from any device that had access to the victim’s iCloud account. An attacker with physical access to an iOS device may be able to view the photos on the lock screen. This issue does not exist in previous versions of iOS and iPadOS. An attacker could access the photos on the lock screen by taking a screenshot.
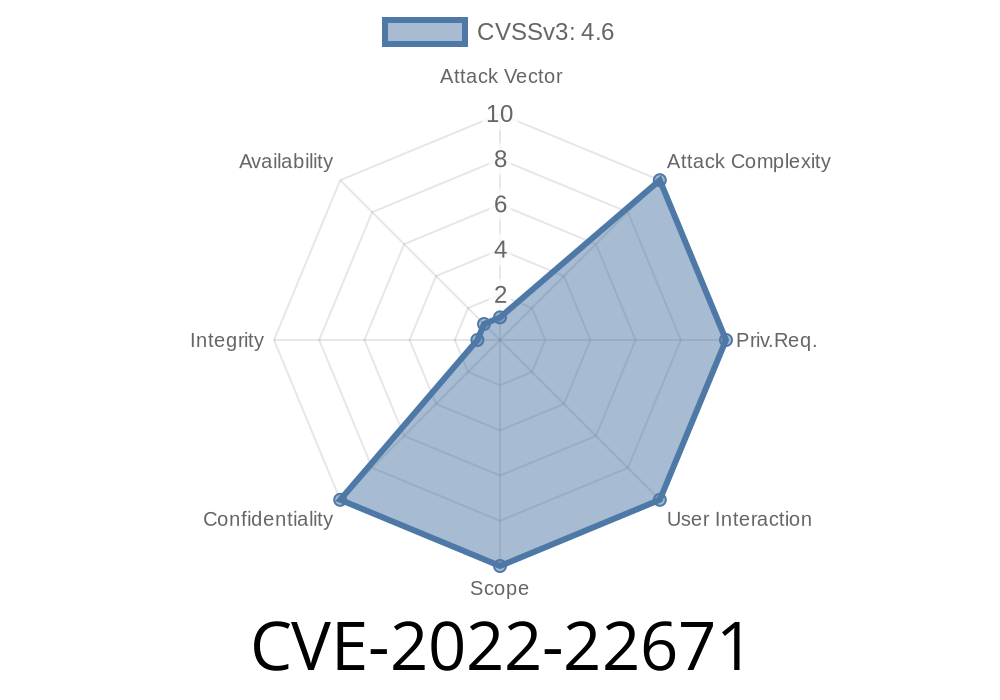
CVE-2023-22672
An attacker with physical access to an iOS device may be able to access the photos on the lock screen of a victim’s device.
Weak Authentication
The weak authentication means that even if the victim took a screenshot of the lock screen, they would not be able to access any data on it. The device is also protected by a passcode, so there is no way for an attacker with physical access to view personal photos on the lock screen without knowing the passcode.
What you need to do to protect yourself against this issue
For users who have not updated to add the passcode lock screen, Apple has provided a workaround. Users can create a dummy passcode and then use it to log into the device.
The vulnerability was first reported on January 3, 2019.
Timeline
Published on: 03/18/2022 18:15:00 UTC
Last modified on: 03/24/2022 18:51:00 UTC