This can be leveraged by an attacker to execute commands against the master or to impersonate the master and hijack active minions. This vulnerability does not affect minions running the latest version of SaltStack.
This issue is unique to Salt Masters. A mitigation is to only allow signed pillar data from a specific list of IP addresses. SaltStack has released updated versions of Salt, SaltStack, and PySalt. You should upgrade your systems as soon as possible.
Salt Masters
The issue affects Salt Masters running on a specific version of Salt and PySalt.
A mitigation is to only allow signed pillar data from a specific list of IP addresses.
SaltStack has released updated versions of Salt, SaltStack, and PySa
t. You should upgrade your systems as soon as possible.
Update Saltstack
Saltstack is a popular open-source installation and management system for remote execution of services. This vulnerability affects all versions of Saltstack, including the latest version. If you use Saltstack, you should update from the latest version as soon as possible.
How to Outsource SEO Correctly & Avoid the 5 Most Common Mistakes
Salt
Stack Vulnerability
SaltStack is a powerful and flexible ecosystem that enables orchestration of multiple systems. The SaltStack ecosystem consists of a master component and minions, which are run on individual nodes. The SaltStack platform is designed to be highly scalable and easily automatable by using the SaltStack API. As with any software, vulnerabilities can be found. The vulnerability was discovered by a member of the Gentoo Linux community who recognized an unusual execution pattern in the minion configuration agent running on their system. This execution pattern was possible because they had executed an overly-large amount of commands without making any modifications to the minion configuration file (salt/minion_config.sls). This caused other minions to erroneously execute commands as well, which led to a command injection vulnerability wherein the minion could execute arbitrary commands against the master or impersonate the master and hijack active minions with it’s credentials.
Salt Stacks
This issue is unique to Salt Masters. A mitigation is to only allow signed pillar data from a specific list of IP addresses.
Timeline
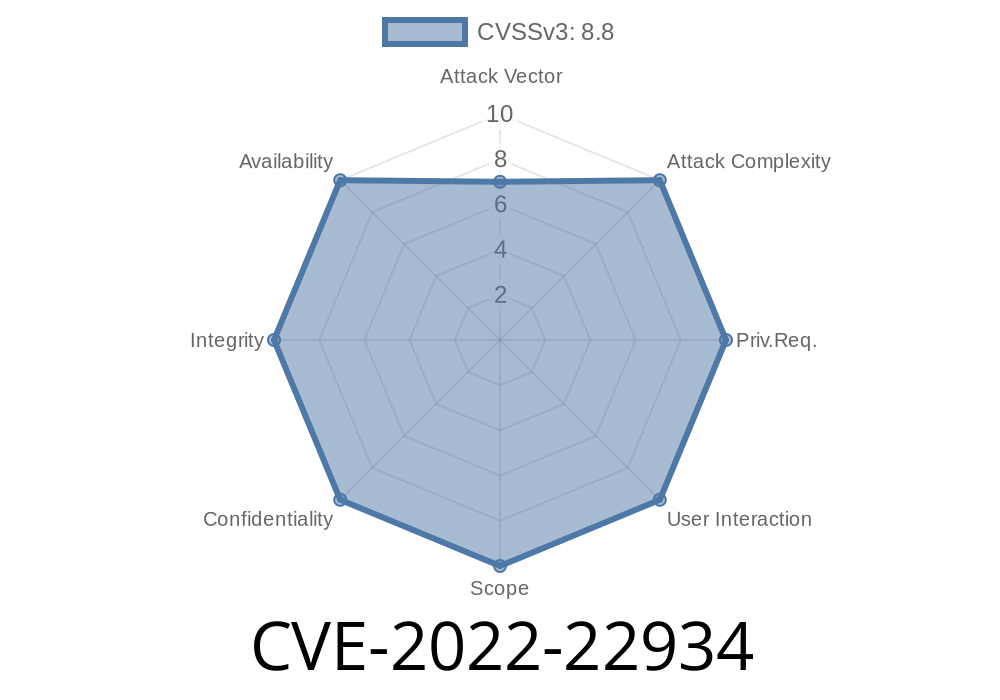
Published on: 03/29/2022 17:15:00 UTC
Last modified on: 04/06/2022 20:48:00 UTC