For example, if a malicious actor hosts a Windows virtual machine on a Windows host and installs VMware Tools, then the malicious actor may be able to gain system privileges in the Windows guest OS by exploiting an uncontrolled search path element in the Windows host OS. VMware Tools is only supported on Windows 7 and later, so Windows hosts that run Windows earlier than Windows 7 are not supported with VMware Tools. For more information, see VMware Tools Unsupported Operating Systems and End-User Licensing Agreement. VMware Tools is only supported on Windows 7 and later, so Windows hosts that run Windows earlier than Windows 7 are not supported with VMware Tools. For more information, see VMware Tools Unsupported Operating Systems and End-User Licensing Agreement. VMware Tools for Windows (11.x.y and 10.x.y prior to 12.0.0) contains a denial-of-service vulnerability. A malicious actor may be able to cause a denial-of-service condition in the Windows guest OS by sending a large amount of network traffic to the Windows guest OS that is connected to a network interface on the Windows host that has been configured to receive a large amount of network traffic. VMware Tools is only supported on Windows 7 and later, so Windows hosts that run Windows earlier than Windows 7 are not supported with VMware Tools. For more information, see VMware Tools Unsupported Operating Systems and End-User Licensing Agreement
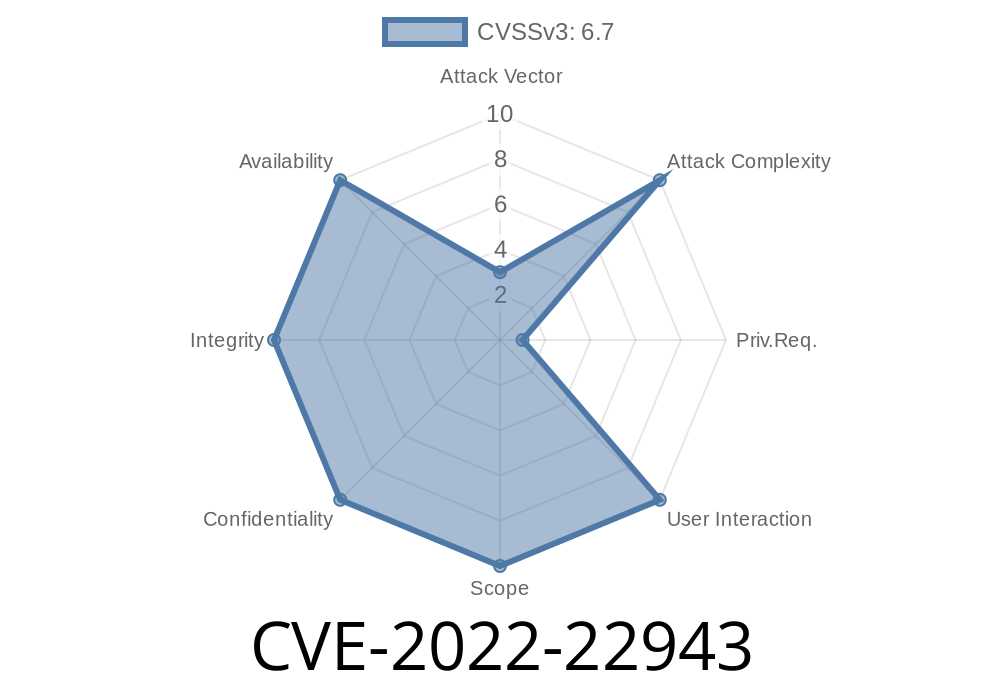
CVE-2022-22913
VMware Tools contains a vulnerability that could allow a malicious actor to execute arbitrary code on the host. Specifically, VMware Tools for Windows (11.x.y and 10.x.y prior to 12.0.0) contains a denial-of-service vulnerability that could allow a malicious actor to cause the ESXi host to crash by sending a large amount of network traffic to the ESXi host that is connected to a network interface on the ESXi host that has been configured to receive a large amount of network traffic.
VMWare tools for Solaris and Linux
VMware Tools is only supported on Windows 7 and later, so Windows hosts that run Windows earlier than Windows 7 are not supported with VMware Tools. For more information, see VMware Tools Unsupported Operating Systems and End-User Licensing Agreement. VMware Tools for Solaris and Linux contains a denial-of-service vulnerability. A malicious actor may be able to cause a denial-of-service condition in the Solaris or Linux guest OS by sending a large amount of network traffic to the Solaris or Linux guest OS that is connected to a network interface on the Solaris or Linux host that has been configured to receive a large amount of network traffic. VMware Tools is only supported on Windows 7 and later, so Windows hosts that run Windows earlier than Windows 7 are not supported with VMware Tools. For more information, see VMware Tools Unsupported Operating Systems and End-User Licensing Agreement
Checklist: VMWare Host Operating System Requirements
The following is a checklist of the minimum operating system requirements for running VMware Tools on Windows hosts:
-Windows Server 2008 and later
-Windows 7 and later
End-User License Agreement (EULA)
End-User License Agreement (EULA)
The EULA for VMware Tools (11.x.y and 10.x.y prior to 12.0.0) contains a denial-of-service vulnerability. A malicious actor may be able to cause a denial-of-service condition in the Windows guest OS by sending a large amount of network traffic to the Windows guest OS that is connected to a network interface on the Windows host that has been configured to receive a large amount of network traffic. VMware Tools is only supported on Windows 7 and later, so Windows hosts that run Windows earlier than Windows 7 are not supported with VMware Tools. For more information, see VMware Tools Unsupported Operating Systems and End-User Licensing Agreement
Timeline
Published on: 03/03/2022 22:15:00 UTC
Last modified on: 03/17/2022 19:03:00 UTC