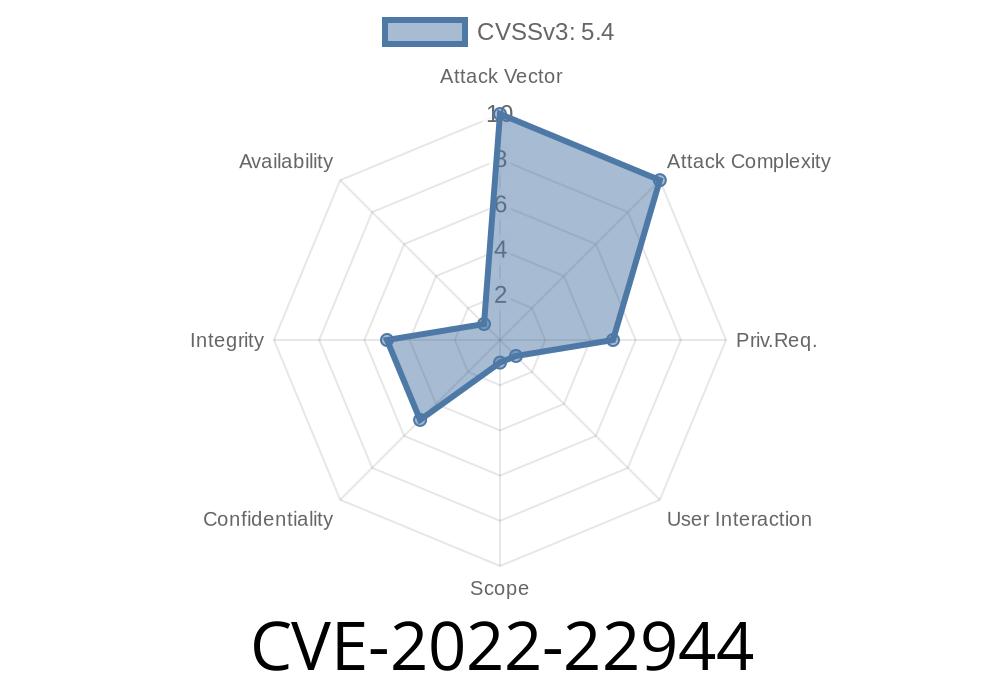
In 2022, a critical vulnerability surfaced in VMware’s Workspace ONE Boxer app. Registered as CVE-2022-22944, this issue centers on a stored Cross-Site Scripting (XSS) flaw in the app’s calendar event descriptions. If you work with mobile enterprise email or calendar suites—especially if you support organizations running VMware tools—this is worth your full attention.
Below, I break down what went wrong, how the exploit works, code snippets, and what you must know to keep your users safe.
What's VMware Workspace ONE Boxer?
Workspace ONE Boxer is a secure mobile email, calendar, and contact management app. Many companies rely on it to keep business communication safe and streamlined.
What Is CVE-2022-22944?
CVE-2022-22944 exposes users to a stored XSS vulnerability in Workspace ONE Boxer’s calendar event descriptions—a section where you just expect to see plain event details.
With this bug, a malicious actor could create an event with a crafted description that contains script tags. When anyone opens or previews the event, arbitrary JavaScript executes in their context. This could let hackers steal credentials, session tokens, or even control the user’s session.
References
- NIST CVE Record
- VMware Security Advisory (VMSA-2022-001)
Why Did This Happen?
The Boxer app did not properly sanitize or validate the input taken from the calendar event description. It just displayed whatever was saved—meaning harmful HTML (like <script>) would run as code.
Imagine a malicious user sends you a calendar invite with a description like this
Meeting to discuss Q2 numbers.
<script>
alert('This is an XSS attack! Your cookies: ' + document.cookie);
</script>
This input goes into Boxer’s database. The app naively renders the HTML when any target user opens or previews the invite. Instantly, their session is compromised.
1. Create a malicious ICS calendar invite
Below, you see a simplified invite with a dangerous script in the DESCRIPTION.
BEGIN:VCALENDAR
VERSION:2.
BEGIN:VEVENT
SUMMARY:Finance Meeting
DESCRIPTION:Finance projections for next quarter. <script>alert('XSS!');</script>
DTSTART:20240621T140000Z
DTEND:20240621T150000Z
END:VEVENT
END:VCALENDAR
2. Send this .ics file by email, or use any other calendar integration method.
3. User opens this event in Workspace ONE Boxer.
The script runs, displaying an alert box. In a real attack, the code could easily steal login tokens or sensitive data.
The Core Problem: Poor Input Handling
When Boxer parsed and displayed the DESCRIPTION field, it failed to strip or escape HTML tags. This is a classic XSS scenario:
// Simulated insecure render code
function renderEventDescription(desc) {
document.getElementById('event-desc').innerHTML = desc; // UNSAFE!
}
A secure version would escape HTML entities, like so
function escapeHTML(str) {
return str.replace(/&/g, "&")
.replace(/</g, "<")
.replace(/>/g, ">")
.replace(/"/g, """)
.replace(/'/g, "'");
}
function renderEventDescriptionSafe(desc) {
document.getElementById('event-desc').innerHTML = escapeHTML(desc);
}
Attack Vector: Malicious ICS file, calendar integration, or event shared via email
- What Happens: Attacker code is run in the trusted app’s context—potentially stealing session tokens, redirecting victims, or attacking company systems.
Target: Victims who view the crafted calendar event
It's as simple as sending an invite to a target, waiting for them to open it, and collecting their info.
Is This Still a Threat?
VMware issued patches to fix the vulnerability. But, if your organization hasn’t deployed these updates to all devices, you might still be exposed.
Review any app that renders HTML for proper input sanitization and output encoding.
- Test for XSS (try inserting <script>alert(1)</script> into descriptions).
More Resources
- How Cross-Site Scripting Works
- ICS Calendar Format Explained
- Securing Mobile Apps Against XSS
TL;DR
CVE-2022-22944 allowed attackers to inject malicious JavaScript into VMware Workspace ONE Boxer calendar event descriptions, by just embedding <script> tags in the ICS invite. If you’re running a vulnerable version, a simple meeting invite could compromise your device and data.
Always keep mobile applications updated and audit your code for unsafe rendering!
Stay safe—and patch early.
*Exclusive analysis by ChatGPT*
Timeline
Published on: 03/02/2022 21:15:00 UTC
Last modified on: 03/09/2022 21:05:00 UTC