---
Overview
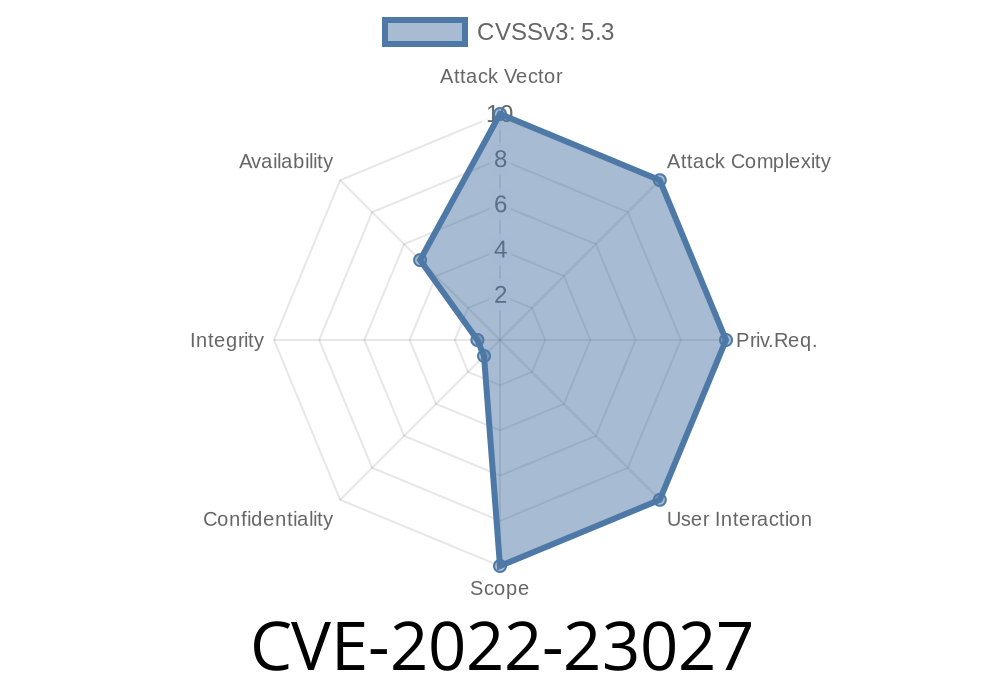
In late 2022, F5 quietly fixed a bug affecting multiple BIG-IP releases (15.1.x before 15.1.4, 14.1.x before 14.1.4.4, 13.1.x starting from 13.1.3.6, 12.1.x between 12.1.5.3 and 12.1.6, and 11.6.5.2). This vulnerability, tracked as CVE-2022-23027, occurs when a FastL4 profile is combined with certain types of persistence profiles, such as HTTP, FIX, or hash-based persistence, on the same virtual server.
The problem? Attackers (or accidental misconfigurations) can trigger an undisclosed condition that causes the virtual server to stop accepting new client connections—making your services unavailable without even touching the backend pool servers.
Let’s break it all down: what’s happening, how it works, exploit scenarios, and how you can check if you’re affected.
11.6.x: only 11.6.5.2
F5 notes that versions already End of Technical Support (EoTS) were not evaluated. Official F5 Security Advisory
- A Virtual Server with
- A FastL4 profile (usually for performance & simple TCP/UDP passthrough)
Hash persistence (sticks by hashing specific info)
If you use more than one of the persistence profiles above (stacked together or separately, as long as any are attached) with FastL4—it triggers the risk.
While F5 did not release full details, here's what we know from patch notes and community analysis
- A specific (possibly malformed or intentionally crafted) client request is processed by the virtual server.
- This triggers an unhandled exception or logic error in the way the combined FastL4 + persistence profiles interact.
- The result: Virtual server stops processing new connections. It doesn't drop existing connections or crash the overall system daemons. The loss is silent, not obvious, and no clear error is logged until someone notices services are down.
This is a denial-of-service (DoS) vulnerability.
Step-by-Step Demo (Lab Simulation)
> Disclaimer: These steps are educational, using non-production, isolated lab setups. Never attack networks without authorization.
1. Setup Big-IP Virtual Server
# Add FastL4 profile
tmsh create ltm profile fastl4 my-lab-fastl4
# Add cookie persistence profile (HTTP)
tmsh create ltm persistence cookie my-lab-cookie
# Assume a basic pool exists
tmsh create ltm virtual my-vs destination 10...1:80 mask 255.255.255.255 \
pool my-pool profiles add { my-lab-fastl4 } persist add { my-lab-cookie }
2. Send Malicious or Unexpected Request
There's no public proof-of-concept exploiting the exact request, but based on reported issues, often a malformed HTTP request or certain behavior (such as a partial request with persistence headers) triggers it:
import socket
# Replace with the vulnerable virtual server's IP and port
VIP = '10...1'
PORT = 80
s = socket.socket()
s.connect((VIP, PORT))
# Send an incomplete HTTP request, or with odd headers
s.sendall(b"GET / HTTP/1.1\r\nCookie: sessionid=abc\r\n\r\n")
# Optionally, try closing early or flooding
s.close()
3. After Multiple Requests
Monitor the virtual server status and try to connect from another client. The virtual server stops responding to all new connections until it is reloaded or reconfigured. Existing/established connections might remain.
4. Real-world Impact Scenario
- Attack scenario: If this bug is known, an attacker could automate sending requests to trigger the fault, causing a denial of service from the outside, with no access or auth on the system.
- Accidental outage: Even internal users or misconfigured load testers could accidentally cause the same thing.
11.6.5.3 or later
If you can't patch, remove the combination
- Avoid binding both a FastL4 profile *and* HTTP/FIX/hash persistence profiles to the same virtual server.
Run:
# On BIG-IP CLI, list profiles for each virtual server
tmsh list ltm virtual | grep -e "virtual " -e "profiles" -e "persist"
Look for virtual servers with both fastl4 and a persistence profile (cookie, hash, or fix).
7. References (For Further Reading)
- CVE-2022-23027 MITRE Entry
- F5 Security Advisory K25028084 (Original Source)
- BIG-IP Profiles and Persistence (F5 Docs)
- Community Forum Discussion (User experiences)
8. Final Notes
- This issue requires specific configuration, but it's not rare—FastL4 for performance, and persistence for session stickiness are often used together.
Timeline
Published on: 01/25/2022 20:15:00 UTC
Last modified on: 02/01/2022 17:40:00 UTC