or systems which access that Kibana instance. Users with this permission are responsible for creating index patterns and are advised to closely review their configuration to ensure no malicious script is being injected into that pattern. As a precaution, we recommend disabling index patterns until a secure version is released. We will provide more details on this XSS vulnerability as they become available.
Conclusion: Security in Kibana
We recommend disabling the vulnerable index patterns until a secure version of Kibana is released.
New Feature: Dashboard Enhancements
Create dashboard patterns and import/export them into external databases.
We have added the ability to create dashboard patterns and also to import/export out these patterns into external databases. This feature is currently in beta and should be considered experimental. We recommend that users visit the dashboard pattern guide for a comprehensive list of requirements, configurations, and best practices for this new feature.
What is Elasticsearch?
Elasticsearch is a full-text, distributed search engine. It is used for performing real-time aggregations and searches of large amounts of data. Elasticsearch supports the concept of a cluster or nodes, which allow it to scale horizontally.
Elasticsearch is a popular open source application that provides features such as:
* Full text search
* Data aggregation
* Data visualization
* Complex queries with nested fields such as geo proximity, time and score
* Automatic indexing via dynamic scripting patterns (Kibana)
Elasticsearch can be used in conjunction with Apache Hadoop YARN to perform streaming analytics on Hadoop clusters.
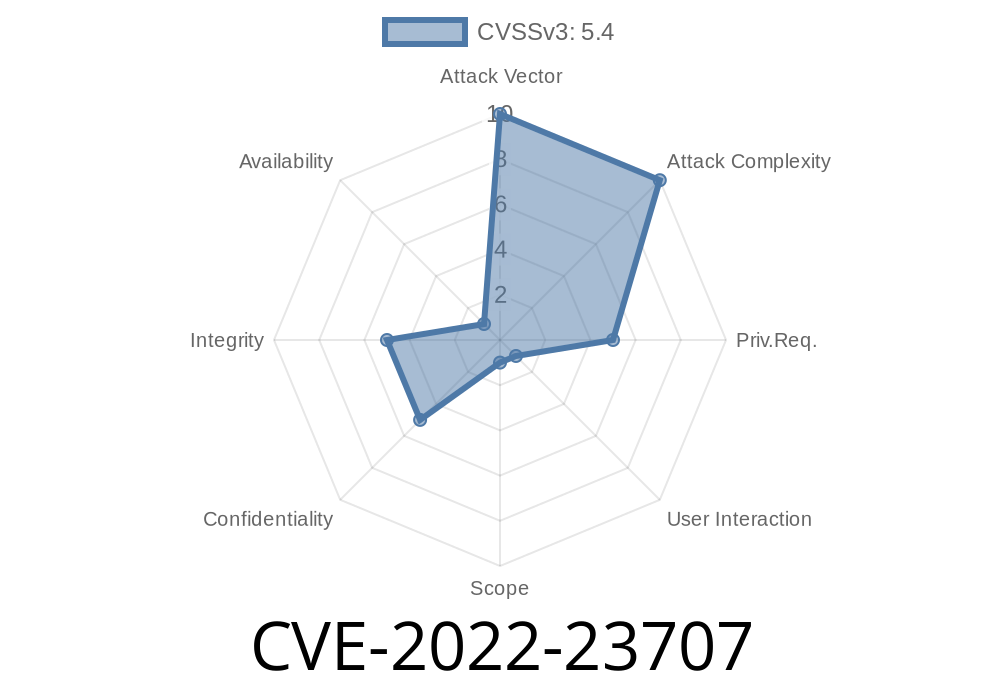
Instance Names and IP Addresses CVE-2022-23707:
A vulnerability in the application was discovered in which certain input is not properly filtered during processing. An attacker can exploit this vulnerability to inject arbitrary JavaScript into the main page of a web application, which will then be parsed and executed by Kibana.
This vulnerability is present on all versions of Elasticsearch from 1.x up to 6.0.
Timeline
Published on: 02/11/2022 18:15:00 UTC
Last modified on: 02/22/2022 13:36:00 UTC