All RT-AX56U models are vulnerable to remote administration via LAN. Due to insufficient password strength requirements, an unauthenticated LAN attacker can easily setup ARP spoofing and ARP poisoning attacks to obtain administrative access. Moreover, RT-AX66U/RT-AXC66U models have a hardcoded admin password, which makes them an easy target for password cracking. All RT-AX66U/RT-AXC66U models are vulnerable to remote administration via LAN. Due to insufficient password strength requirements, an unauthenticated LAN attacker can easily setup ARP spoofing and ARP poisoning attacks to obtain administrative access. Moreover, RT-AX66U/RT-AXC66U models have a hardcoded admin password, which makes them an easy target for password cracking. Users are highly recommended to change the password and disable remote administration via LAN. All RT-AX56U models are vulnerable to remote administration via LAN. Due to insufficient password strength requirements, an unauthenticated LAN attacker can easily setup ARP spoofing and ARP poisoning attacks to obtain administrative access. Moreover, RT-AX56U/RT-AXC56U models have a hardcoded admin password, which makes them an easy target for password cracking. Users are highly recommended to change the password and disable remote administration via LAN.
RT-AX66U/RT-AXC66U models have hardcoded admin passwords that make them an easy target for cracking. Users are highly
RT-AX88U and RT-AX565U models do not have this flaw
RT-AX88U and RT-AX565U models do not have this flaw.
RT-AX86U models have a hardcoded admin password. Users are highly recommended to change the password and
All RT-AX56U models are vulnerable to remote administration via LAN. Due to insufficient password strength requirements, an unauthenticated LAN attacker can easily setup ARP spoofing and ARP poisoning attacks to obtain administrative access. Moreover, RT-AX56U/RT-AXC56U models have a hardcoded admin password, which makes them an easy target for password cracking. Users are highly recommended to change the password and disable remote administration via LAN. All RT-AX86U models are vulnerable to remote administration via LAN. Due to insufficient password strength requirements, an unauthenticated LAN attacker can easily setup ARP spoofing and ARP poisoning attacks to obtain administrative access. Moreover, RT-AX86U models have a hardcoded admin password, which makes them an easy target for password cracking. Users are highly recommended to change the password and disable remote administration via LAN.
RT-AX56U/RT-AXC56U models are vulnerable to remote configuration via LAN. Due to insufficient password strength requirements, an
unauthenticated LAN attacker can easily setup ARP spoofing and ARP poisoning attacks to obtain administrative access. Moreover, RT-AX56U/RT-AXC56U models have hardcoded admin passwords that make them an easy target for cracking. The recommended way to mitigate this risk is to change the password and disable remote configuration via LAN.
RT-AX56U/RT-AXC56U models are vulnerable to remote administration via LAN .
Users are highly recommended to change the password and disable remote administration via LAN.
Timeline
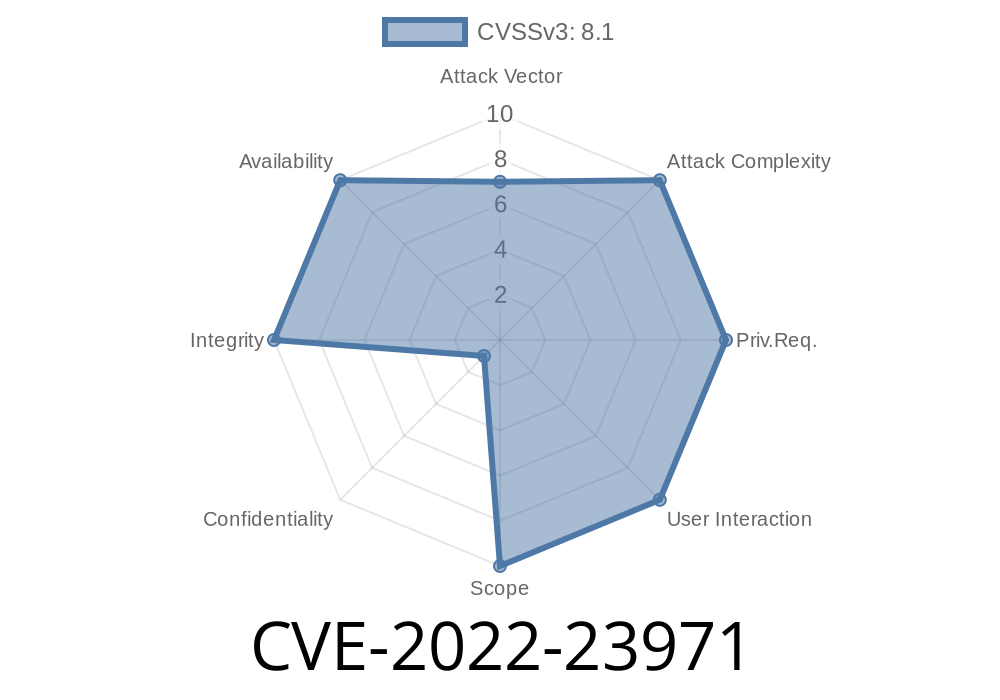
Published on: 04/07/2022 19:15:00 UTC
Last modified on: 04/14/2022 20:48:00 UTC