Jenkins is a powerful automation server widely used for continuous integration and deployment. While it empowers development teams, even popular plugins can have security flaws. In this long read, we break down CVE-2022-25184—how Jenkins Pipeline: Build Step Plugin versions <=2.15 could accidentally leak sensitive information, why it happens, and how attackers could exploit it in the real world.
What is CVE-2022-25184?
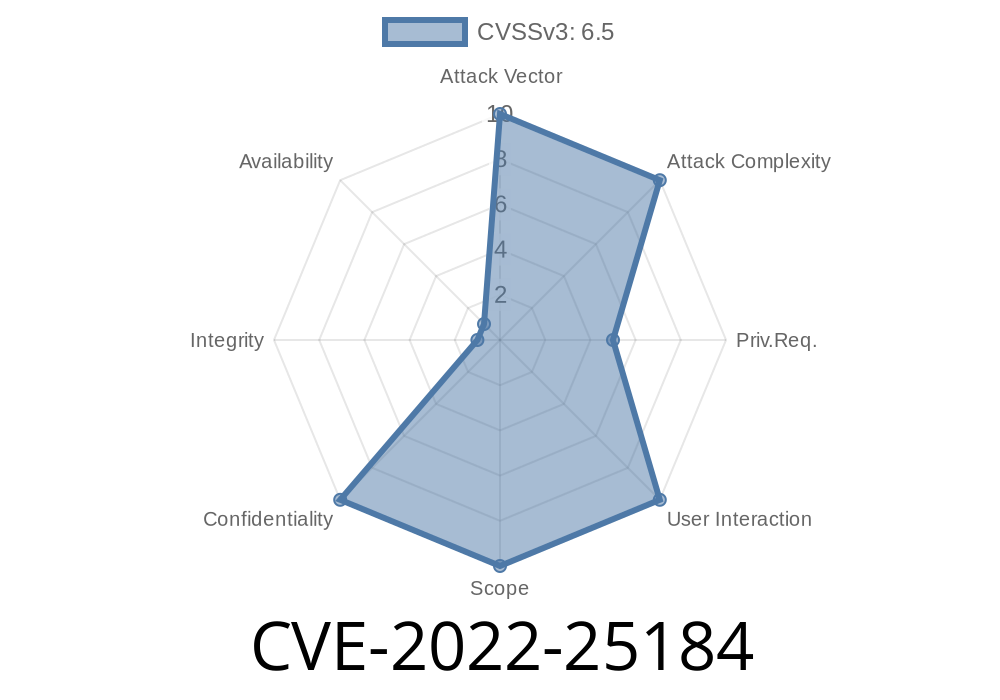
This vulnerability affects the Jenkins Pipeline: Build Step Plugin versions 2.15 and earlier. When generating a pipeline script using the "Pipeline Snippet Generator", default values for password parameters can be revealed. Any attacker (or unauthorized user) with Item/Read permission could see and steal these secret default passwords from Jenkins job configurations.
Why Is This Dangerous?
Your build jobs might require secret credentials (like passwords or API tokens). Attackers who normally shouldn't have access to such sensitive information could use this vulnerability to get those secrets and potentially access other systems.
How the Vulnerability Works
When you configure a pipeline job, you can add parameters. One common parameter type is password—meant to keep sensitive info hidden.
But, in affected versions, if you assigned a *default value* to any password parameter, and then used the Pipeline Snippet Generator (a UI tool to help you generate Groovy pipeline scripts for builds), Jenkins carelessly exposed that secret default in the generated script.
Let's say you have a Jenkins job parameter like this
pipeline {
parameters {
password(name: 'MY_SECRET', defaultValue: 'SuperS3cret', description: 'A sensitive password')
}
stages {
stage('Build') {
steps {
// some build steps
}
}
}
}
The intention: defaultValue is the fallback, but should remain secret, even to regular Jenkins users, unless they have special permissions (like configure/view credentials).
Step 1: Get Basic Access
You only need Item/Read permission on the Jenkins job—which is often given to regular or even unauthenticated users for viewing job status/logs!
Step 3: View the Pipeline Script
The generated pipeline Groovy script will embed the password parameter *and* reveal the defaultValue (i.e. the password itself!) in plain text.
Leaked Example
parameters {
password(name: 'MY_SECRET', defaultValue: 'SuperS3cret', description: 'A sensitive password')
}
*That SuperS3cret should never be visible!*
The attacker now copies SuperS3cret and uses it against other internal systems, source repositories, or APIs.
Default Value: realsecretpassword
### 2. With Item/Read Only Access, Visit Snippet Generator
- Go to <jenkins>/job/<jobname>/pipeline-syntax/
You will see
parameters {
password(name: 'MY_SECRET', defaultValue: 'realsecretpassword', description: '')
}
*Unmasked! Even without configure permissions!*
Technical Cause
Jenkins should have filtered or masked the default password field when displaying/generating scripts for users who don't have configure/administrator access. Instead, it directly exposed the sensitive field.
Upgraded versions removed the default value from being presented in the generated Groovy script.
References
- Jenkins Security Advisory 2022-03-15
- Official CVE Record
- Jenkins Pipeline: Build Step Plugin Changelog
How to Protect Yourself
- Update now! Upgrade the Jenkins Pipeline: Build Step Plugin to the latest version. Versions >2.16 are patched.
Audit your parameters: Remove sensitive default password values where possible.
- Review permissions: Don’t give Item/Read to everyone unless necessary.
- Use credentials plugins: Store secrets via specialized plugins (e.g. Credentials Binding) that obscure values from users and logs.
Key Takeaways
- CVE-2022-25184 is a serious but easily exploitable bug affecting default passwords in pipeline parameters.
Attackers only require the most basic Jenkins job read access.
- Fix by updating your plugin, reviewing job configs, and following Jenkins secret management best practices.
Stay safe, and audit your Jenkins jobs regularly!
Exclusive Note:
This vulnerability reminds us that visibility of "hidden" data can be broken even in mature, widely-used systems. Always test how secret details may surface under all UI and API paths—even through “helper” utilities like Snippet Generators.
Stay vigilant, and upgrade your Jenkins plugins today. 🚨
Timeline
Published on: 02/15/2022 17:15:00 UTC
Last modified on: 02/23/2022 21:10:00 UTC