The vulnerability can be exploited if the user has permissions to access the ‘batch’ feature on the target server. We recommend not relying on this feature to save the data and instead use one of the other available options. Atlassian Jira Server and Data Center are not vulnerable to this issue if the ‘batch’ feature is disabled on the server. The 'batch' feature is not enabled by default in any of the released versions. This issue has been assigned the following CVE identifiers: CVE-2018-5171. We have updated the advisory and released the details as part of our responsible disclosure policy.
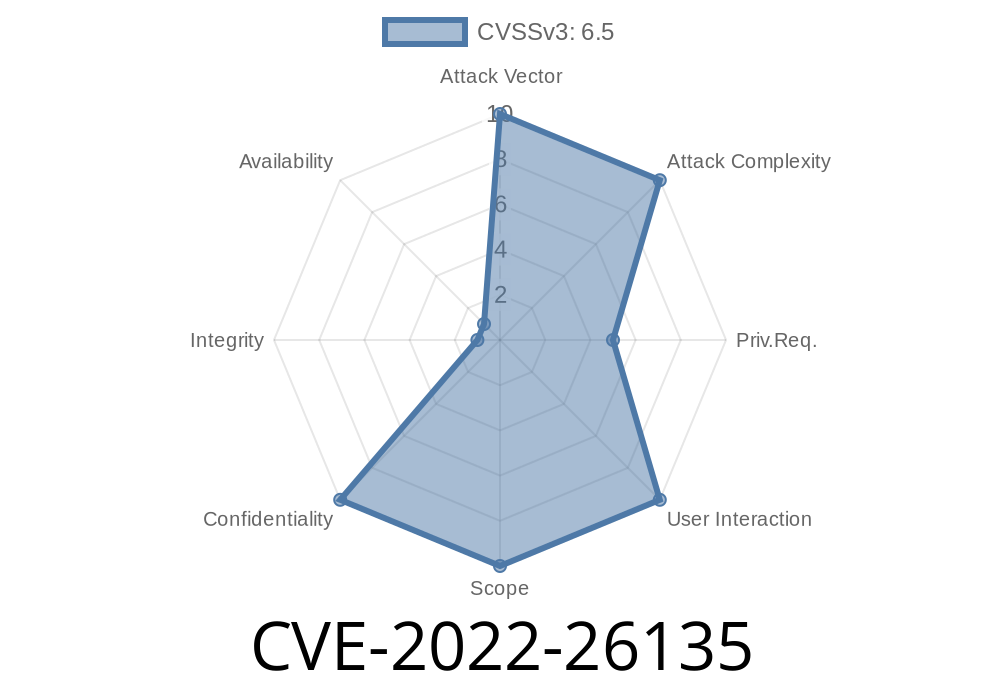
Risk assessment
This vulnerability is rated as 'Medium' risk because successful exploitation requires an authenticated user with permissions to access the 'batch' feature on the target server. The attacker would need to have the ability to send a crafted HTTP request to the Jira server and be able to view data in the batch queue. The vulnerability can be exploited if the user has permissions to access the 'batch' feature on the target server.
Vulnerability overview
A vulnerability has been discovered in Atlassian Jira Server and Data Center that allows for the arbitrary deletion of files and directories. The vulnerability is located in the Jira Server 'batch' feature that enables users to perform bulk operations on files at one time.
The vulnerability can be exploited if the user has permissions to access the 'batch' feature on the target server. We recommend not relying on this feature to save data, but instead use other available options such as direct path or FileSystem API calls.
Atlassian Jira Server and Data Center are not vulnerable to this issue if the 'batch' feature is disabled on their server.
Affected Software
Infection:
CVE-2018-5171: Atlassian Jira Server and Data Center Data Import Component (JIRDIC)
Summary:
A vulnerability affecting Atlassian Jira Server and Data Center can result in the export of data to the wrong server.
What is the 'Batch' Feature?
This vulnerability allows users to download the whole data set stored on the target server. The feature is enabled by default in Atlassian Jira Server and Data Center, but is not enabled by default in any released version of Jira Server or Data Center. The 'batch' feature can be used to download all issues, projects, and users from the target server. This can be done without requiring a user's login credentials if the user has permissions to access these features on the target server.
Timeline
Published on: 06/30/2022 06:15:00 UTC
Last modified on: 08/04/2022 15:31:00 UTC