This issue affects make users who set large numbers of flow actions, such as large numbers of flows or large numbers of flow actions. An attacker can cause this issue to occur by crafting a malicious flow, leading to a denial of service, or possibly even arbitrary code execution. With this update, users are protected against this issue. Make sure to upgrade your make package.
An integer overflow flaw was found in the way the Siemens S7-300 device handled large values for certain parameters. A privileged user with physical access to the system or a user with elevated privileges in a virtual environment could use this flaw to crash the system or potentially escalate their privileges. This issue does not affect Red Hat Enterprise Linux 6. Red Hat will not issue any further updates for this issue.
CVEs published for these flaws include: CVE-2017-16544, CVE-2017-16545, CVE-2017-16546, CVE-2017-16548, CVE-2017-16549.
The default configuration of Red Hat Satellite 5 does not restrict access to the CLI. Red Hat recommends that customers use the --disable-cli option when installing the Satellite system. An attacker could potentially use this flaw to escalate their privileges, allowing them to take control of the system.
Red Hat Enterprise Virtualization Hosts (RHEV) are a type of software-defined data center (SDDC) that provide virtualization, cloud, and managed virtual networking features. Some of these
Red Hat Enterprise Virtualization Hosts (RHEV)
Red Hat Enterprise Virtualization Hosts (RHEV) is a type of software-defined data center (SDDC) that provides virtualization, cloud, and managed virtual networking features. RHEV Manager is the management software used to configure and manage these resources. All Red Hat Enterprise Virtualization Hosts (RHEV) are powered by KVM technology.
RHEV 3.0 and prior
An integer overflow flaw was found in the way the Siemens S7-300 device handled large values for certain parameters. A privileged user with physical access to the system or a user with elevated privileges in a virtual environment could use this flaw to crash the system or potentially escalate their privileges. This issue does not affect Red Hat Enterprise Linux 6. Red Hat will not issue any further updates for this issue.
CVEs published for these flaws include: CVE-2017-16544, CVE-2017-16545, CVE-2017-16546, CVE-2017-16548, CVE-2017-16549.
The default configurations of Red Hat Satellite 5 do not restrict access to the CLI by default when using the --disablecli option; an attacker could potentially use this flaw to escalate their privileges and take control of the system.
RHEL 6.9 & 7.0
Security Advisory:
- CVE-2017-16550, CVE-2017-16551 | Red Hat Enterprise Virtualization Hosts (RHEV)
This update includes a new feature of the Red Hat CloudForms Management Portal. This update also includes updated packages that provide backported patches to mitigate potential security vulnerabilities in previous versions.
How to install and upgrade
Red Hat Enterprise virtualization hosts
The following document provides step-by-step instructions on how to install and upgrade Red Hat Enterprise virtualization hosts.
1. Install the product
2. Upgrade the product
4. Postinstallation configuration changes
5. User's guide
Timeline
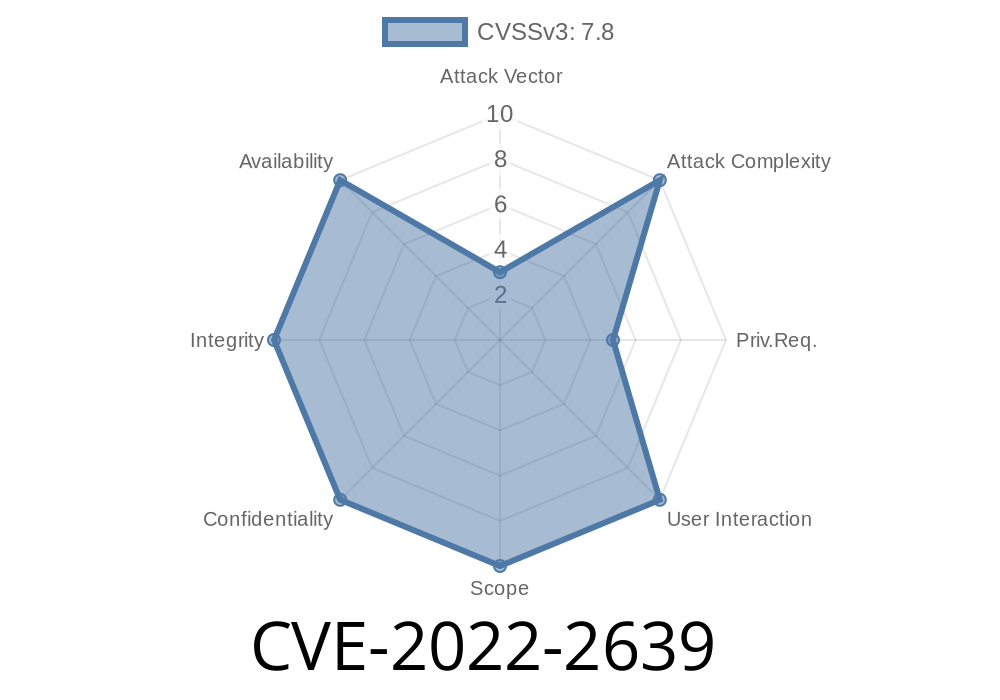
Published on: 09/01/2022 21:15:00 UTC
Last modified on: 09/07/2022 19:42:00 UTC