---
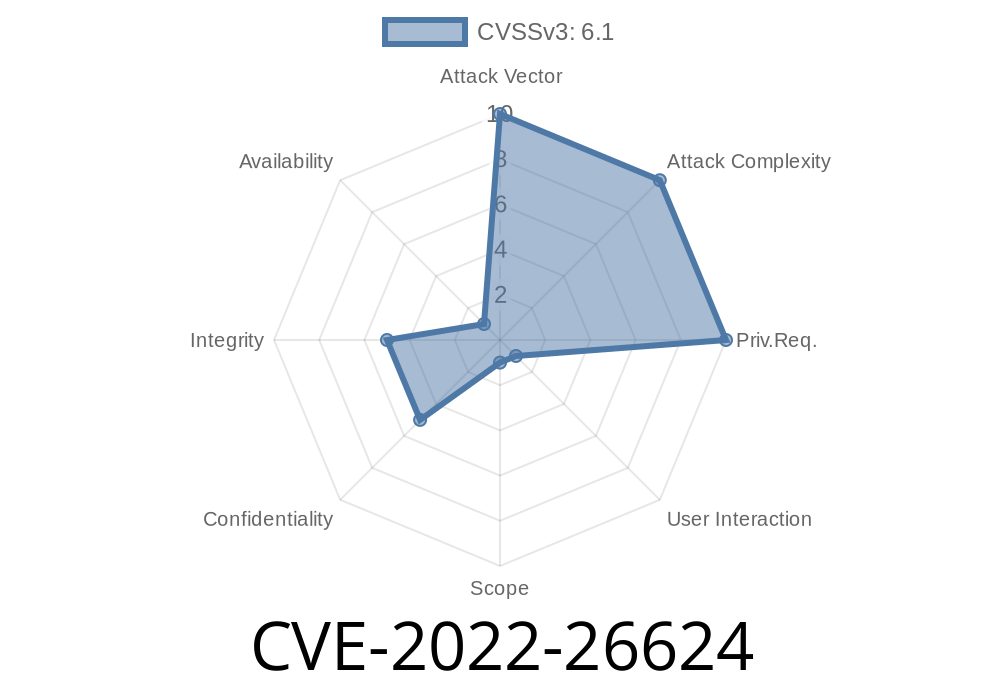
Cross-Site Scripting (XSS) is still one of the most dangerous vulnerabilities that can appear in web apps. It lets attackers inject malicious scripts into websites, which run on the browsers of visitors. In this long read, we’ll dig into CVE-2022-26624, a real XSS vulnerability found in Bootstrap v3.1.11 and v3.3.7. The issue is specifically in how the Title parameter is handled in the /vendor/views/add_product.php page.
Let’s break it down, step by step, show some real code, and reveal how an attacker can exploit this bug.
According to the official NIST CVE Record
> Bootstrap v3.1.11 and v3.3.7 was discovered to contain a cross-site scripting (XSS) vulnerability via the Title parameter in /vendor/views/add_product.php.
In other words: The app doesn’t properly sanitize the user-supplied Title field when adding a product. So, if a user (or an attacker) enters specially crafted HTML/JavaScript in the Title, it will be stored and later rendered on the page, leading to XSS.
2. Vulnerable Code Example
Here’s a simplified version, in PHP, of what might be happening inside /vendor/views/add_product.php:
<!-- add_product.php (vulnerable snippet) -->
<form action="add_product.php" method="post">
<label for="title">Product Title:</label>
<input type="text" name="title" id="title" />
<!-- ...more fields... -->
<input type="submit" value="Add Product" />
</form>
<?php
if ($_SERVER['REQUEST_METHOD'] == 'POST') {
$title = $_POST['title'];
// ...code to save $title in the database...
echo "<h2>Product '$title' has been added!</h2>";
}
?>
Why Is This Vulnerable?
The $_POST['title'] value is taken directly from user input and displayed inside an HTML tag without any kind of sanitization or escaping. That means anyone can input HTML/JavaScript that the browser will run as real code.
An attacker could enter a title like this
<script>alert('XSS');</script>
Here’s how it would play out for an unsuspecting admin
1. Attacker goes to the "Add Product" form and sets the title to <script>alert('XSS');</script>.
The page displays:
Product '<script>alert('XSS');</script>' has been added!
The browser hits the <script> tag and runs alert('XSS').
BOOM! Now, the attacker can run any JavaScript they want in the context of that page.
This could be escalated, for example, to steal session cookies or perform actions as the logged-in user.
Go to /vendor/views/add_product.php and in the title field, enter
"><script>alert(document.cookie)</script>
The page will respond with
<h2>Product '"><script>alert(document.cookie)</script>' has been added!</h2>
The browser parses the injected script, and you get a popup with the current cookie.
5. Why Did This Happen in Bootstrap v3.1.11 and v3.3.7?
While Bootstrap is mainly a frontend framework, many templates (especially older ones) used plain PHP without best practices for output encoding. The included sample code, or 3rd party projects built on Bootstrap, sometimes skipped sanitizing outputs, especially user inputs like product titles.
The vulnerability is not in Bootstrap's core JavaScript/CSS, but in how its sample code or reliant projects (like admin panels) used it.
Sanitize all user input before displaying it. In PHP, always use htmlspecialchars() or similar
echo "<h2>Product '" . htmlspecialchars($title, ENT_QUOTES, 'UTF-8') . "' has been added!</h2>";
Or, use frameworks and template engines that auto-escape outputs.
Never trust user input! Even if it “looks safe.”
7. References
- CVE-2022-26624 at NVD
- OWASP XSS Cheat Sheet
- Bootstrap’s docs
8. Final Thoughts
CVE-2022-26624 is a simple but dangerous XSS found in Bootstrap-based PHP pages. If you ever write a web form, never output user-supplied values without proper sanitizing. XSS is easy to introduce, but also easy to prevent once you get used to escaping all outputs.
Have you checked your own code lately? Stay safe out there!
Timeline
Published on: 04/08/2022 09:15:00 UTC
Last modified on: 04/22/2022 13:56:00 UTC