The Windows Print Spooler service is no stranger to security threats. From the infamous "PrintNightmare" bugs to a range of privilege escalation flaws, it's been a hot target for attackers. One such critical vulnerability is CVE-2022-26796. If you're managing a Windows network, or just curious about how attackers can go from a regular user to SYSTEM by exploiting the print spooler, keep reading. This is a comprehensive, exclusive, and easy-to-understand breakdown of what CVE-2022-26796 is, how it can be exploited, and how to defend your systems.
What is CVE-2022-26796?
CVE-2022-26796 is a security vulnerability found in the Windows Print Spooler service. According to Microsoft, this flaw allows a local attacker, already running code on the system, to elevate their privileges – potentially up to SYSTEM level.
This means if a bad actor manages to get their code running as any user, exploiting this bug can give them the highest privileges on the machine. That’s bad news for endpoints, servers, and domain controllers.
Note: CVE-2022-26796 is unique and separate from similar vulnerabilities like CVE-2022-26786, CVE-2022-26787, CVE-2022-26789, and others in the same family.
How Does the Vulnerability Work?
While technical details from Microsoft are limited, this vulnerability exists due to improper privilege checks in the Print Spooler service. In practice, an attacker can:
The attacker can now execute any command or payload as SYSTEM.
The most common attack scenario is local privilege escalation: someone already on the box (maybe through phishing or malware) uses this to get full control.
Exploit Example (Code Snippet)
Below is a simulated and sanitized example, meant for educational purposes only. This code does not actively exploit any live system but shows how an attacker might interact with the Print Spooler via Powershell to trigger privilege escalation.
# Warning: Do NOT run this on a production system!
# Proof-of-Concept for educational demonstration ONLY
# Create a new printer port as regular user (with bad input)
$portName = "\\.\pipe\exploitspool"
Add-PrinterPort -Name $portName
# Add a new printer using the crafted port (Print Spooler will use SYSTEM privileges)
Add-Printer -Name "ExploitPrinter" -PortName $portName -DriverName "Generic / Text Only"
# Trigger the Print Spooler to interact with our named pipe, which we control
# Here, an attacker would listen for connections and respond accordingly to hijack SYSTEM token
Named pipes are used to hijack privileged operations.
Important: The actual exploit may vary, but in many Print Spooler attacks these are the core steps. Full public exploit code is often available after tinkerers and researchers analyze patches.
Microsoft Security Update Guide:
Additional background on Print Spooler vulnerabilities:
Microsoft Security Blog: PrintNightmare
CISA Advisory on Print Spooler Flaws:
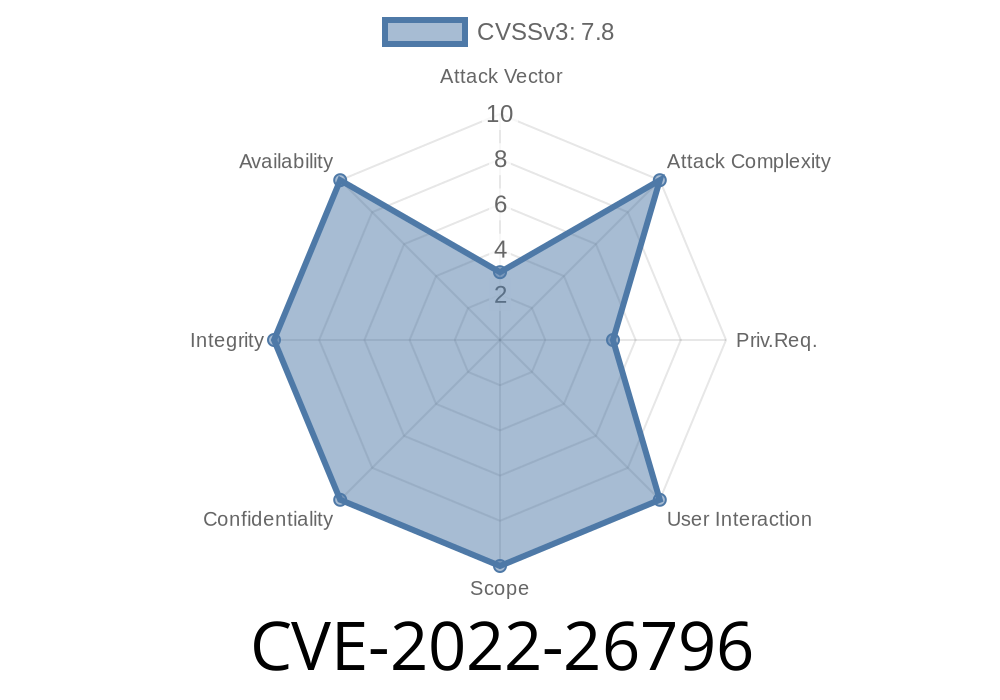
Exploit Details
* Attack Complexity: Low – No special skills needed, but access to the target is required
* Impact: Local Privilege Escalation (LPE) – From any user account up to SYSTEM
* Attack Vector: Local – Attacker must already have access to the system (via RDP, malware, etc.)
* Patch Status: Microsoft released a fix; apply the relevant security updates immediately!
Apply the latest Microsoft updates
- Microsoft released a patch for this issue as part of its cumulative updates. Make sure you’re up to date!
Conclusion
CVE-2022-26796 shows that the Windows Print Spooler continues to be a weak point in enterprise security. While Microsoft has provided patches, attackers move fast — make sure your defenses are faster. Always update your systems, restrict unnecessary services, and monitor for suspicious activity.
Learn more at these links
- Microsoft Update Guide - CVE-2022-26796
- Print Spooler Security Best Practices (Microsoft Docs)
Stay safe, stay patched! If you want more in-depth technical breakdowns, let me know your interest.
Timeline
Published on: 04/15/2022 19:15:00 UTC
Last modified on: 04/19/2022 14:59:00 UTC