This vulnerability is due to Microsoft Office improperly handling objects in memory when parsing maliciously modified files. An attacker could exploit this vulnerability by sending malicious files to a user who has Microsoft Office installed on their system. Microsoft Office will fail to handle objects properly when parsing maliciously modified files. An attacker could exploit this vulnerability by sending a user a specially crafted file via email. Typically, users open email messages sent from colleagues or clients. An attacker could exploit this vulnerability by persuading a user to open a specially crafted file sent via email. Microsoft Outlook is vulnerable to this issue. Microsoft Word is also vulnerable to this issue. Microsoft Excel is also vulnerable to this issue. This vulnerability could be exploited when a user opens a specially crafted file. As a result, the user could be exposed to code that could run with the privileges of the user’s account.
Vulnerability in Microsoft Office Software:
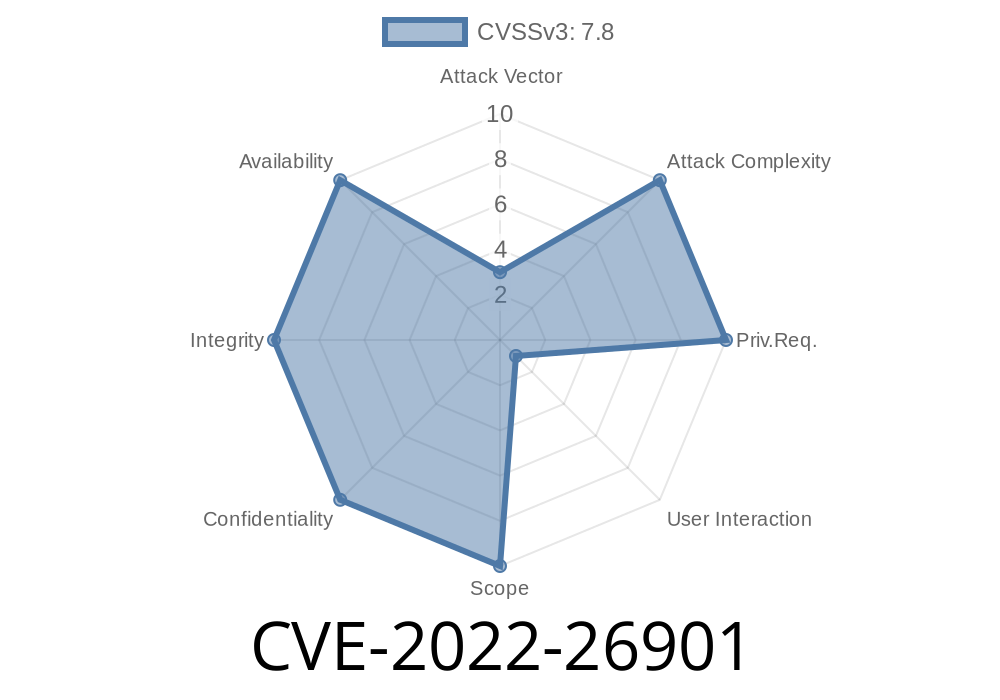
-CVE-2022-26901 is due to Microsoft Office improperly handling objects in memory when parsing maliciously modified files.
-An attacker could exploit this vulnerability by sending a user a specially crafted file via email.
-Typically, users open email messages sent from colleagues or clients.
-An attacker could exploit this vulnerability by persuading a user to open a specially crafted file sent via email.
Vulnerability in Microsoft Office Could Allow Remote Code Execution
This vulnerability is a remote code-execution vulnerability. An attacker could exploit this vulnerability by convincing an unsuspecting user to open a specially crafted file. As a result, the user could be exposed to code that could run with the privileges of the user’s account.
Such malicious files are often delivered via email. Microsoft Outlook is vulnerable to this issue. Microsoft Word is also vulnerable to this issue. Microsoft Excel is also vulnerable to this issue. This vulnerability could be exploited when a user opens a specially crafted file sent via email.
Vulnerability overview:
CVE-2022-26901 is a vulnerability in Microsoft Office that could allow attackers to run code with the privileges of the user’s account. This vulnerability is due to Microsoft Office improperly handling objects when parsing maliciously modified files in memory. An attacker would have to send a specially crafted file via email. Typical users open email messages sent from colleagues or clients, so this vulnerability could be exploited when a user opens a specially crafted file sent via email.
This vulnerability was found in November 2017 and patched in February 2018 by Microsoft Patch Tuesday.
Microsoft Word and Microsoft Excel
The vulnerability affects Microsoft Word and Microsoft Excel. This vulnerability is rated as critical. An attacker could exploit this vulnerability by sending a user a specially crafted file via email. Typically, users open email messages sent from colleagues or clients. An attacker could exploit this vulnerability by persuasion to open a specially crafted file sent via email.
Microsoft Excel Vulnerability
Microsoft Excel is a very popular spreadsheet program. It has been around for a long time and is used by people across the world. This particular vulnerability affects Microsoft Excel on Windows systems and was discovered in October, 2017.
Microsoft Office ids vulnerable to this issue because it processes specially crafted files that could lead to code execution with privileges of the user’s account. So, if someone wanted to steal your data or get into your account, they could send you a maliciously modified file via email that would exploit this vulnerability. If you are running Microsoft Office on Windows, be sure to update your software immediately.
Timeline
Published on: 04/15/2022 19:15:00 UTC
Last modified on: 04/26/2022 13:34:00 UTC