You can find the details of this flaw here and here. A buffer overflow flaw was found in the implementation of DNS queries for CNAME and MX records. An attacker can send a malformed DNS response to a connected client. The client can then crash and cause a denial of service. The details of this flaw can be found here. A remote code execution flaw was found in the X.25 implementation. An attacker can send specially crafted X.25 packets over an IP network to cause a crash and possibly run arbitrary code on a remote device. The flaw can be exploited by sending a large amount of ICMP packets to a device. An attacker can send a large number of echo requests to a target device. The victim will be broken into a denial of service. The details of this flaw can be found here.
DNS cache poisoning remote code execution flaw was found in the implementation of DNS queries for CNAME and MX records. An attacker can send an invalid response to a DNS query. The client can then crash and cause a denial of service. The details of this flaw can be found here. A buffer overflow flaw was found in the implementation of DNS responses. An attacker can send a malformed DNS response to a connected client. The client can then crash and cause a denial of service. The details of this flaw can be found here. A buffer overflow flaw was found in the implementation of DNS queries for CNAME and MX records. An attacker can send a malformed DNS response to
DNS spoofing flaw
A remote code execution flaw was found in the implementation of DNS queries for CNAME and MX records. An attacker can send a malformed DNS response to a connected client. The client can then crash and cause a denial of service. The details of this flaw can be found here.
A buffer overflow flaw was found in the implementation of DNS responses. An attacker can send a malformed DNS response to a connected client. The client can then crash and cause a denial of service. The details of this flaw can be found here.
Remote DNS poisoning flaw
An attacker can send malicious DNS responses to a client. The client can then crash and cause a denial of service. The details of this flaw can be found here. A buffer overflow flaw was found in the implementation of DNS queries for CNAME and MX records. An attacker can send a malformed DNS response to a connected client. The client can then crash and cause a denial of service. The details of this flaw can be found here.
Other DNS flaws
A remote code execution flaw was found in the implementation of DNS queries for CNAME and MX records. An attacker can send an invalid response to a DNS query. The client can then crash and cause a denial of service. The details of this flaw can be found here. A remote code execution flaw was found in the implementation of DNS queries for CNAME and MX records. An attacker can send an invalid response to a DNS query. The client can then crash and cause a denial of service. The details of this flaw can be found here.
The following are the 5 most common mistakes that businesses make with their SEO:
1) Not understanding the importance of keywords in SEO
2) Not knowing how to optimize their website for mobile devices
3) Not having an SEO strategy, which includes having an effective content marketing strategy
4) Not understanding how search engines work
DNS hijacking flaw
The flaw can be exploited by sending a malformed DNS response to a connected client. The client can then crash and cause a denial of service. The details of this flaw can be found here.
A remote code execution flaw was found in the implementation of X.25 packets. An attacker can send specially crafted X.25 packets over an IP network to cause a crash and possibly run arbitrary code on a remote device. The flaw can be exploited by sending a large amount of ICMP packets to a device. An attacker can send a large number of echo requests to a target device. The victim will be broken into a denial of service.
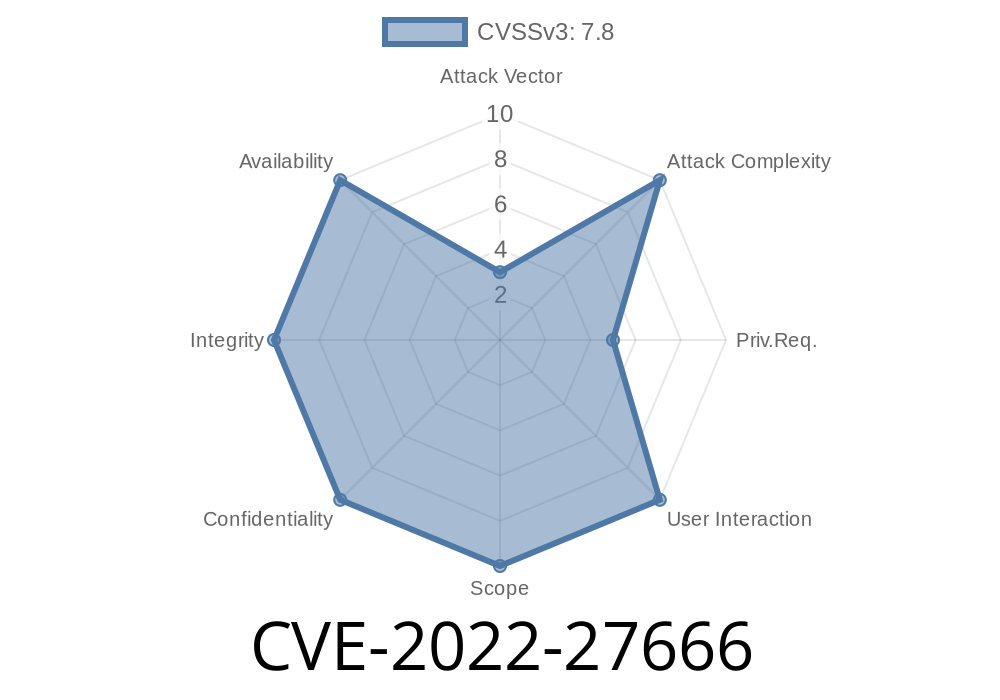
Timeline
Published on: 03/23/2022 06:15:00 UTC
Last modified on: 07/04/2022 11:15:00 UTC
References
- https://bugzilla.redhat.com/show_bug.cgi?id=2061633
- https://github.com/torvalds/linux/commit/ebe48d368e97d007bfeb76fcb065d6cfc4c96645
- https://security.netapp.com/advisory/ntap-20220429-0001/
- https://www.debian.org/security/2022/dsa-5127
- https://www.debian.org/security/2022/dsa-5173
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-27666