To trigger this vulnerability an attacker has to place a malicious SVG file in the ‘Insert SVG’ procedure. The user has to open the malicious SVG file in Autodesk Fusion 360 before it is parsed and executed in the application. It is important to note that the user does not need to open the malicious SVG file in Autodesk Fusion 360 itself. The attacker can place the malicious SVG file in any external application that allows users to open SVG files. In addition, the user does not need to open the file using the application itself. An attacker can force the user to open the malicious SVG file in an external application through social engineering. This vulnerability can be exploited by an attacker to obtain sensitive information such as the victim’s public IP address.
Vulnerability Details
This vulnerability allows an attacker to exploit Autodesk Fusion 360 and extract sensitive information like the victim’s public IP address. This can be achieved by placing a malicious SVG file in the ‘Insert SVG’ procedure.
An attacker must be able to place a malicious SVG file in the ‘Insert SVG’ procedure before it is parsed and executed in the application. The user does not need to open the malicious SVG file in Autodesk Fusion 360 itself. The attacker can place the malicious SVG file in any external application that allows users to open SVG files. In addition, the user does not need to open the file using the application itself. An attacker can force the user to open the malicious SVG file in an external application through social engineering.
Remote Code Execution (RCE)
To trigger this vulnerability an attacker has to place a malicious SVG file in the ‘Insert SVG’ procedure. The user has to open the malicious SVG file in Autodesk Fusion 360 before it is parsed and executed in the application. It is important to note that the user does not need to open the malicious SVG file in Autodesk Fusion 360 itself. The attacker can place the malicious SVG file in any external application that allows users to open SVG files. In addition, the user does not need to open the file using the application itself. An attacker can force the user to open the malicious SVG file in an external application through social engineering. This vulnerability can be exploited by an attacker to obtain sensitive information such as the victim’s public IP address.
Vulnerability Finding Tips
There are several ways an attacker can find this vulnerability.
1. The attacker can use social engineering to exploit the vulnerability and then collect sensitive information like the victim’s public IP address.
2. The attacker can search for similar vulnerabilities in Autodesk Fusion 360 and test these vulnerabilities by downloading them to the host computer and testing them out through experimentation on the target system.
3. The attacker can search for similar vulnerabilities in other software products that allow users to import SVG files.
4. The attacker can scan publicly available services that accept external SVG files from other applications and test if they are vulnerable to this attack vector.
Vulnerable WooCommerce Extension
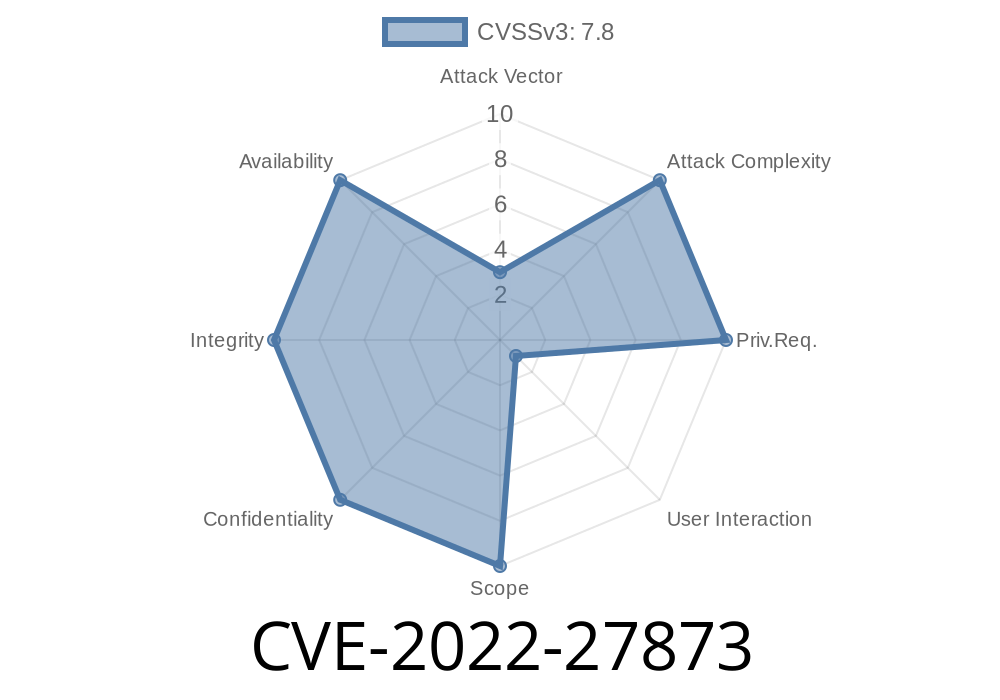
The WooCommerce extension is vulnerable to CVE-2022-27873. The vulnerability is located in the ‘Insert SVG’ procedure in the application and can be exploited by an attacker to obtain sensitive information such as the victim’s public IP address.
Timeline
Published on: 07/29/2022 16:15:00 UTC
Last modified on: 08/05/2022 18:49:00 UTC