XSS is when data from one site is injected into another site via a vulnerable script. GitHub is a great example of this. As user data can be sent from one site to another, it enables attackers to exploit the data in ways that were not possible before. Today we are going to go over how XSS works and how you can prevent it on your site. XSS comes in many different flavors. By far the most common type is called Stored XSS. It happens when one site embeds data directly from another site. For example, if a user was logged into a WordPress site, Stored XSS would allow someone to inject malicious code into that WordPress site. This is a very common type of XSS that happens across many different types of websites.
What is Stored XSS?
Stored XSS happens when a vulnerable script is injected into a site that allows data to be sent back and forth between sites. For example, if you were logged into a WordPress site, someone could inject malicious code into that WordPress site. They would then use the data from the WordPress site to send it back to their website. This type of XSS occurs because the two sites are communicating with each other and both sites lack proper protection against XSS vulnerabilities.
How Stored XSS Works
When a site embeds data from another site, there are two different ways the process can go wrong. The first way is when an attacker injects data into the page that is visible to users but is not stored on the page. For example, if an attacker injected some HTML code that contained JavaScript within that HTML code which would then execute on the page, this would be a visible XSS attack and would not be as harmful as one that was stored on your website.
The second type of Stored XSS attack happens when an attacker injects data into your website directly. For example, if someone injected malicious code into a WordPress site via URL shortening services like bitly or goo.gl, this would be considered a Stored XSS attack. This type of attack has much higher consequences because it allows attackers to modify the content on your site in any way they want including actions such as changing your password or adding malicious code to your site. This type of attack is often very hard to detect because most people don’t know to look for it in specific places like an intended URL shortener service.
What is XSS?
Cross-site scripting (XSS) is a type of computer security vulnerability that occurs when an attacker uses a web application running on one server to obtain information from another web application running on another server, which the attacker then displays.
In order to exploit this vulnerability, the attacker needs to trick the victim into clicking on a malicious link or to open an attachment that contains malicious code. If a user is tricked into visiting a website under control of the attacker, they can be infected with malware or their account credentials can be stolen. XSS can also be used for clickjacking, where the user does not intend to visit any site but instead click on specific links in pop-up ads served by other websites.
Timeline
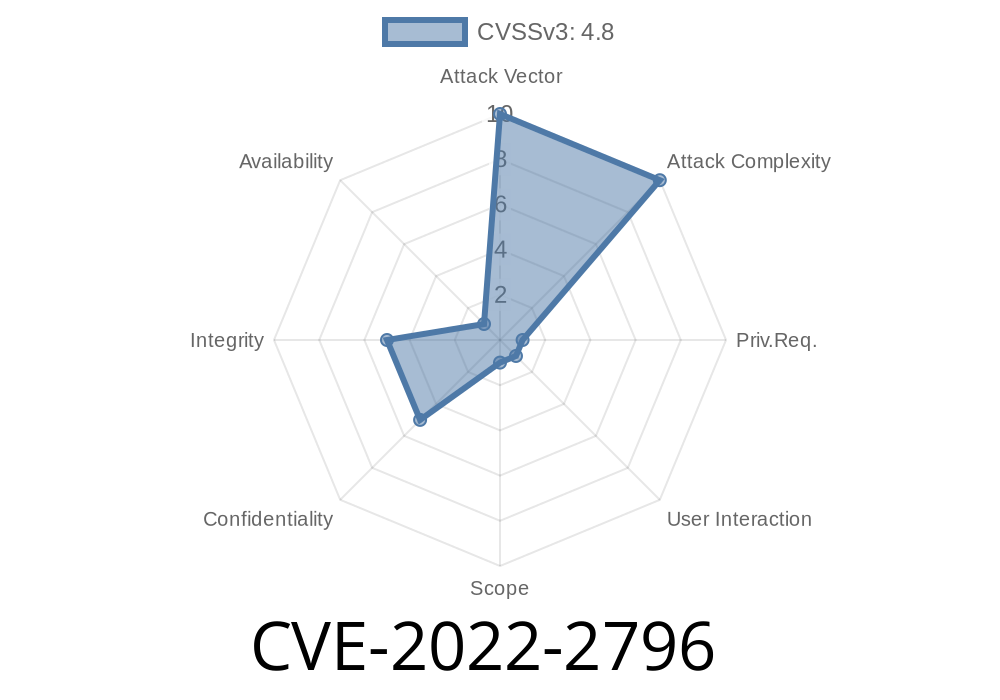
Published on: 08/23/2022 08:15:00 UTC
Last modified on: 08/24/2022 19:56:00 UTC