BitLocker is a full-disk encryption tool integrated into Windows, meant to keep your data safe from unauthorized access. But what if BitLocker itself has a vulnerability that can be exploited, leaving your “encrypted” data exposed? That’s exactly what happened with CVE-2022-29127, a security feature bypass vulnerability that could allow attackers to sneak past BitLocker protections. This post is your one-stop guide to understanding, demonstrating, and mitigating this issue.
What is CVE-2022-29127?
CVE-2022-29127 is a vulnerability in Microsoft BitLocker that allows attackers to bypass BitLocker's encryption under certain conditions. If successfully exploited, it means someone with physical access to the machine could get to your data—even if it's supposed to be locked with BitLocker.
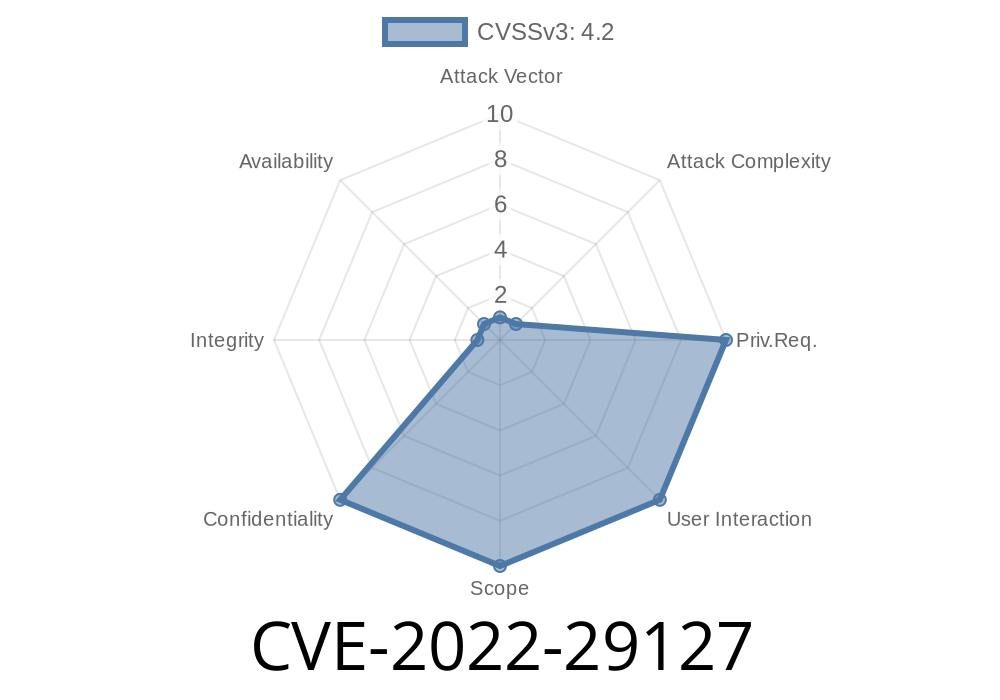
Severity: Important
CVSS Score: 6.9 (Medium)
Affected Systems:
Windows Server 2022
*For the official entry, see Microsoft’s Security Guide.*
How Does the Vulnerability Work?
The issue lies in the way BitLocker handles Secure Boot. If Secure Boot is disabled or tampered with, BitLocker can go into “recovery mode.” But with a sequence of steps, attackers could trick BitLocker into granting access or running unsigned code, bypassing the protection.
Tampers with Secure Boot or bootloaders.
4. Disables/forces BitLocker into recovery mode.
Bypasses BitLocker prompt or gathers information from the recovery interface.
Without proper Group Policy or hardware security configurations, it’s possible for the attacker to bypass BitLocker—even if BitLocker is enabled.
## Exploit Example (for educational/demo purposes only)
Let's say an attacker has grabbed a BitLocker-encrypted laptop. Here’s how they could try to get around the encryption:
Mount the locked disk.
Here's a simple Linux command that could be tried if BitLocker's TPM-only protection is in use and Secure Boot is off:
# Find the BitLocker partition (e.g., /dev/sda2)
sudo fdisk -l
# Try to mount it
sudo cryptsetup bitlkOpen /dev/sda2 bitlocker
# If keys are in TPM only, and Secure Boot is not enforced,
# sometimes the volume can be accessed without password.
sudo mount /dev/mapper/bitlocker /mnt/bitlocker
Note: This often fails if BitLocker is set up more securely (PIN or password), but under specific settings related to CVE-2022-29127, it could succeed.
Real Exploits & PoCs
Due to the nature of this vulnerability, there is no public “metasploit” style exploit. However, Microsoft’s advisory and Hofman Security’s analysis (not official, but informative) discuss scenarios and implications.
How to Protect Yourself
Microsoft’s Patch:
Microsoft released a security update for this vulnerability. Update ASAP. Update details here.
Use Strong BitLocker Setup:
Go to Group Policy:
Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption
Make sure Secure Boot is enabled (not just in BIOS, but actually enforced).
- Use TPM and PIN/Password for best protection.
More Resources
- Microsoft CVE-2022-29127 Security Guide
- BitLocker Overview (Microsoft Docs)
- CISA Alert
- ElcomSoft Blog on BitLocker Attacks
In Summary
CVE-2022-29127 is a wake-up call: For BitLocker to really keep your data safe, don’t just “turn it on”—configure it the right way, keep your system updated, and don’t neglect Secure Boot. Bad security setups are easy targets for cybercriminals with simple tools and physical access. Take a few minutes now, lock things down, and sleep easier later.
Timeline
Published on: 05/10/2022 21:15:00 UTC
Last modified on: 05/23/2022 17:29:00 UTC