Summary:
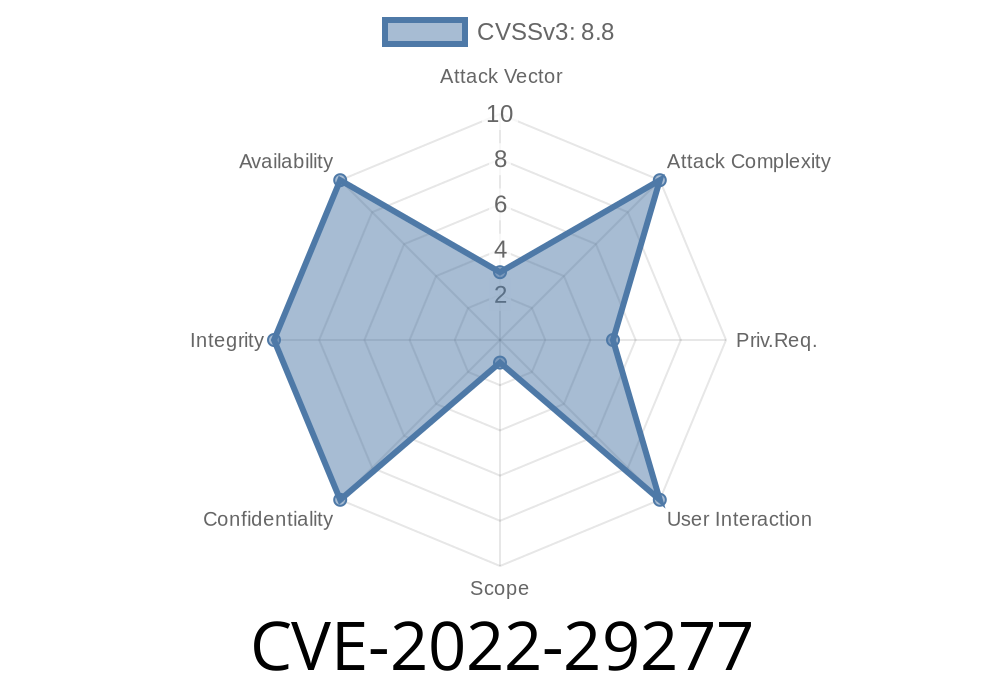
CVE-2022-29277 is a high-impact vulnerability that lurks inside the FwBlockServiceSmm driver. Incorrect pointer checks within the driver — especially during certain operations involving SpiAccessLib — allow attackers to modify any RAM address, including highly privileged SMRAM (System Management RAM). This can have devastating effects, letting malicious code take over protected memory on Intel and AMD platforms.
Below, we’ll break down how this bug works, where it hits, show a code snippet, talk about exploitation, and provide fixes. This is an exclusive, readable look at the vulnerability for security readers and sysadmins.
What is FwBlockServiceSmm?
The FwBlockServiceSmm driver is a part of the firmware layer operating in SMM (System Management Mode). This is a super-privileged context on x86 CPUs, mainly tasked with low-level system management. Anything running in SMM can bypass operating system protections — so vulnerabilities here are a *big deal*.
Where’s the Flaw?
During a security review, it was found that some pointer checks in FwBlockServiceSmm are insufficient when handling certain requests. Specifically, SPI (Serial Peripheral Interface) operations using SpiAccessLib can be tricked into writing the byte value xFF (all bits set) to any RAM address, including the critical SMRAM region.
This means an attacker could overwrite code, configuration, or even inject their own logic into secure firmware space, potentially taking over the whole system at boot or runtime.
Below is a simplified version of what happened. Suppose this function is inside the driver
EFI_STATUS WriteSpiData(EFI_PHYSICAL_ADDRESS* TargetAddr, UINT32 Len) {
if (TargetAddr == NULL) {
return EFI_INVALID_PARAMETER;
}
// BAD: No validation if TargetAddr is inside allowed range!
for (UINT32 i = ; i < Len; ++i) {
*(UINT8 *)(TargetAddr + i) = xFF; // Could touch arbitrary RAM!
}
return EFI_SUCCESS;
}
The problem:
There’s no check that TargetAddr actually points to SPI flash or another safe region — an attacker could supply a pointer to *any* location in RAM or even in protected memory.
An attacker (local or with physical access, possibly remote via a chain of exploits) could
1. Craft a special input/request to the driver from a lower-permission environment (maybe via an OS-level or hypervisor-level vulnerability).
2. Target a critical address — such as system kernel code, control structures, or even SMM handler code.
Force the driver to write xFF to that memory location, corrupting data or code pointers.
4. Cause code execution or system instability. In the worst case, a persistent SMM backdoor could be planted.
Which Hardware is Affected?
This is a cross-vendor vulnerability — both Intel and AMD platforms with affected versions are at risk.
Eagle Stream: 05.44.25.0052
- Greenlow/Greenlow-R (Skylake/Kabylake): Trunk
- Mehlow/Mehlow-R (CoffeeLake-S): Trunk
Comet Lake-S: Trunk
- Tiger Lake H/UP3: 05.43.12.0052
Ryzen 500: 05.44.30.0004
- Embedded ROME/MILAN: Trunk
Hygon
- Hygon #1/#2: 05.36.26.0016
Who Found and Fixed It?
The vulnerability was analyzed and coordinated by Insyde Software as SA-202206 (“Arbitrary Write Defect in FwBlockServiceSmm”). The fix implements tighter pointer validation, rejecting any requests that give pointers outside the expected flash ranges.
Manufacturers have patched their firmware by
- Checking pointer ranges: Now the driver will make sure all pointers stay within allowed SPI-flash boundaries.
- Blocking SMRAM/RAM access: Requests that try to touch RAM/SMRAM are immediately rejected.
Yes, but generally as a second-stage attack. Exploitation usually requires
- Local OS/privileged code execution (or chaining from another vulnerability)
Outdated firmware
With admin rights or vendor tools, an attacker could try to issue a malicious FwBlockServiceSmm request targeting sensitive memory, achieving full system compromise.
How to Protect Yourself
1. Update your firmware: Always patch to the latest version from your board/system vendor.
2. Limit local admin/system access: Many firmware bugs require admin/physical rights.
3. Use secure boot and firmware integrity tools: Lock down system firmware against unauthorized changes.
References
- Insyde Security Advisory SA-202206
- NVD - CVE-2022-29277
- Intel Security Center
- AMD Product Security
Final Word
CVE-2022-29277 is one of those firmware vulnerabilities that can undermine even the best OS-and-app-level security. If you’re running hardware with affected firmware, upgrading is urgent. Remember: bad pointer checks in SMM aren’t just bugs — they’re backdoors waiting to happen.
*Stay safe, keep your firmware up to date, and keep an eye on security advisories!*
Timeline
Published on: 11/15/2022 22:15:00 UTC
Last modified on: 11/22/2022 19:45:00 UTC