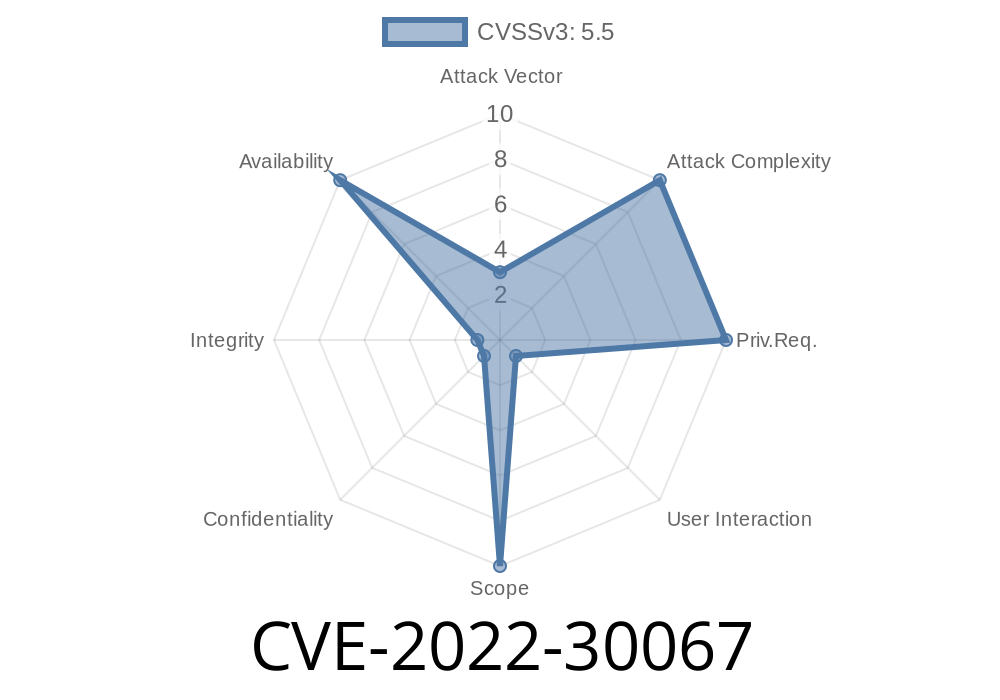
On Windows, GIMP is not installed as a system application, so it is not required to have administrator rights to be vulnerable. To take advantage of the vulnerability, an attacker has to convince a user to open a specially crafted XCF file with GIMP on a Windows machine. All the user has to do is click on the file, and GIMP will allocate for a huge amount of memory, resulting in insufficient memory or program crash. It is also possible that an attacker will trick a user to open a specially crafted XCF file with a legitimate image editing program. This can be done by placing a malicious image in an email or social media post, or by using an exploit. When a user opens the XCF file, GIMP will allocate for a huge amount of memory, resulting in insufficient memory or program crash. GIMP versions 2.10, 2.8 and 2.6 are vulnerable. While GIMP 2.10.30 and 2.99.10 are not vulnerable. Even though GIMP is not installed as a system application, it is still possible to exploit this vulnerability on Windows. An attacker has to convince a user to open a specially crafted XCF file with GIMP on a Windows machine. All the user has to do is click on the file, and GIMP will allocate for a huge amount of memory, resulting in insufficient memory or program crash. It is also possible that an attacker will trick a user to open
GIMP Dependencies
GIMP is a free and open source image editing program. GIMP is hosted on SourceForge. According to their website, GIMP has been available in both binary and source form since 1995. GIMP is developed by the GNU Project and is licensed under the GPLv2 license.
GIMP 2.10
.30 is not vulnerable
GIMP 2.10.30 and 2.99.10 are not vulnerable to CVE-2022-30067 because they do not allocate memory for the overflow.
Timeline
Published on: 05/17/2022 17:15:00 UTC
Last modified on: 05/26/2022 00:04:00 UTC