It was found that in some cases, the LDAP daemon would accept remote LDAP requests for LDAP ports that it did not bind to. This flaw could be exploited by an attacker to inject remote code into the LDAP daemon. What’s worse, this vulnerability only applies to versions of Red Hat Directory Server prior to 2.0 SR-16. Red Hat has provided the following workaround. Users must upgrade their LDAP daemon to version 2.0 SR16 or later.
How to check the LDAP daemon version
To check the LDAP daemon version, use the following command:
# ldapsearch -LLL
Red Hat Directory Server TLS Vulnerability
A flaw in some versions of Red Hat Directory Server was found by Qualys Research Labs that would allow a malicious user to inject code into the LDAP daemon. The attacker could then potentially exploit this vulnerability to read or write files in the LDAP directory or even access other systems through the vulnerable LDAP daemon. What’s worse, this vulnerability only applies to versions of Red Hat Directory Server prior to 2.0 SR-16. As such, users must upgrade their servers to version 2.0 SR16 or later.
DNS service unavailable or running slow
If you are experiencing problems with the DNS service, it might be because the DNS server is being blocked. In some cases, this can lead to slower performance and an inability to resolve queries from your system.
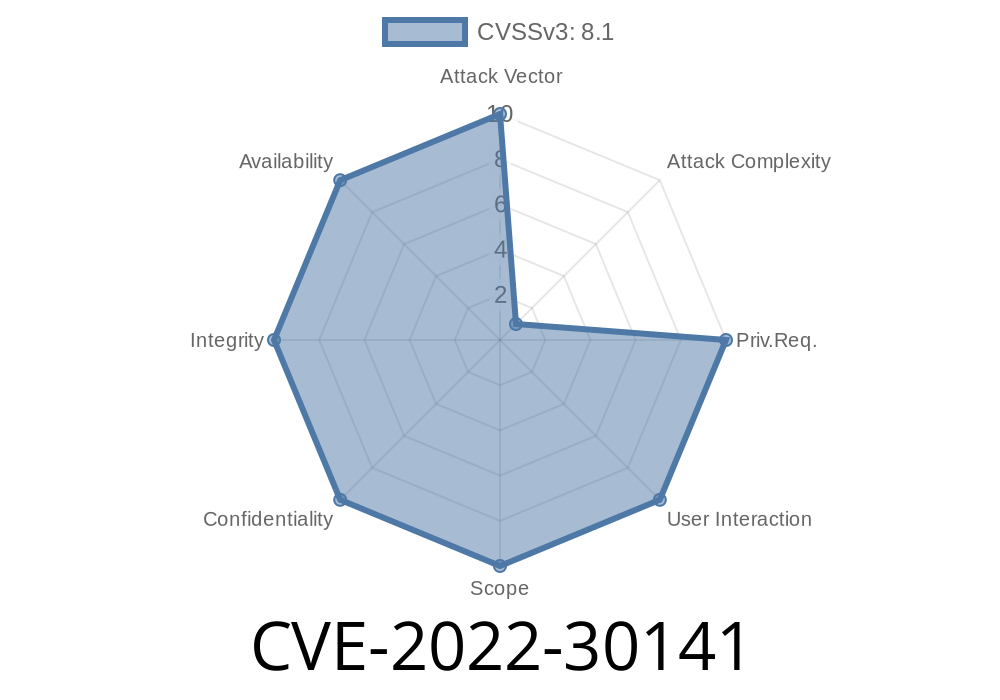
Security Risk Assessment
In order to mitigate the security risk of this vulnerability, it is recommended that users update their LDAP daemon to version 2.0 SR-16 or later. This will eliminate the security risk.
Environment Setup
LDAP Daemon 2.0 SR-16 or later
Timeline
Published on: 06/15/2022 22:15:00 UTC
Last modified on: 06/25/2022 02:37:00 UTC