---
Introduction
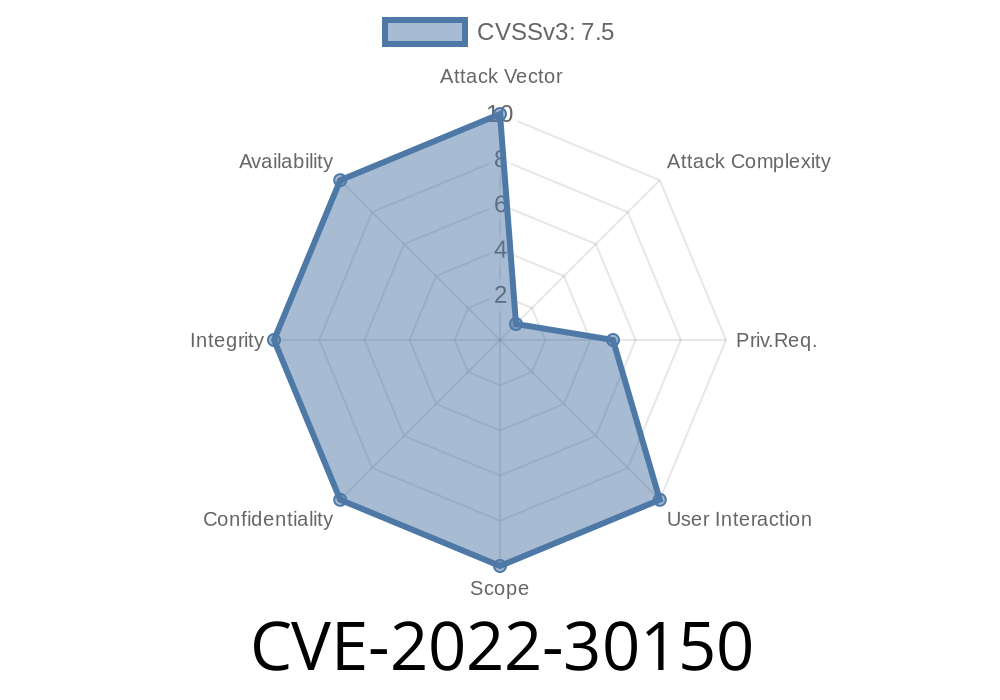
In June 2022, Microsoft patched a significant security flaw in Windows Defender Remote Credential Guard (RDP). Officially known as CVE-2022-30150, this vulnerability allowed attackers to escalate privileges by abusing the way Windows Defender handled Remote Credential Guard scenarios.
In this post, we’ll break down what CVE-2022-30150 is, how it works, and how attackers might exploit it. We’ll use easy-to-read language, practical code snippets, and provide links to original references, giving you both theory and hands-on perspective.
CVSS Score: 7.8 (High)
- Platforms: Windows 10, Windows Server 2016/2019/2022
Summary:
This bug allows an attacker with local access to a vulnerable machine to run code as SYSTEM, the highest privilege on a Windows machine. The way Windows Defender Remote Credential Guard handles remote credentials wasn’t secure and could be leveraged to break out of usage restrictions and gain more permissions than intended.
How Does Remote Credential Guard Work?
Remote Credential Guard is a feature introduced in Windows 10 and Server 2016. Its main goal is to protect user credentials on RDP (Remote Desktop Protocol) sessions, keeping them from being stolen or misused if the remote host is compromised.
But the management and handling of credentials can be tricky, especially when dealing with background services. In this case, the implementation made a mistake that could be used by attackers.
Technical Details
The Microsoft advisory for CVE-2022-30150 simply says:
> "An elevation of privilege vulnerability exists when Windows Defender improperly handles objects in memory."
Thanks to James Forshaw at Google Project Zero, more details are available. Here’s a simplified breakdown of the issue:
- Windows Defender Remote Credential Guard uses a service with SYSTEM privileges to handle authentication tokens.
When users request remote logon, Defender checks access rights.
- Poor permissions checking and mismanaged object privileges allowed local attackers to request tokens and "impersonate" accounts, including SYSTEM.
Example Exploit Code
The following Python code is for educational purposes only and highlights the logic, not a plug-and-play exploit.
import ctypes
from ctypes.wintypes import HANDLE
# This is a simplified version; actual exploitation deals with Windows API and tokens
PROCESS_ALL_ACCESS = (x000F000 | x00100000 | xFFF)
def get_system_token():
# This function would talk to the vulnerable service to get a SYSTEM token
# Pretend grab SYSTEM token (placeholder)
return xDEADBEEF
def spawn_cmd_with_token(token):
# Use duplicated token to create a new process as SYSTEM
# In real exploit: DuplicateHandle + CreateProcessWithTokenW
print(f"[+] Would launch cmd.exe as SYSTEM with token: {hex(token)}")
if __name__ == "__main__":
system_token = get_system_token()
if system_token:
spawn_cmd_with_token(system_token)
else:
print("[-] Failed to get SYSTEM token")
In reality, the exploit involves calling CreateProcessWithTokenW() or DuplicateHandle() with a stolen SYSTEM token, using Windows Native API from Powershell, C#, or C++ code.
A full, practical proof-of-concept is provided by James Forshaw here (for research reading, not attack use):
project-zero/issues/2234
Mitigation
Microsoft Patch:
Microsoft fixed this vulnerability in June 2022 Patch Tuesday. If you’re running Windows 10 or newer, apply the latest Windows Updates.
- Reference: CVE-2022-30150 Microsoft Security Advisory
Other steps:
Learn More
- Microsoft CVE page: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2022-30150
- Google Project Zero write-up: When Everything Elevates
- Forshaw's technical bug report: P Issue 2234
Conclusion
CVE-2022-30150 is a classic example of how even security features can introduce vulnerabilities if access controls aren’t tight. If you run Windows, make sure you’re patched, avoid letting untrusted users run code locally, and stay updated on security reports.
If you want more posts like this — breaking down complex vulnerabilities in plain language — stick around and follow us!
*This guide is for educational and defensive purposes. Always use security research responsibly, and never attack systems without explicit permission.*
Timeline
Published on: 06/15/2022 22:15:00 UTC
Last modified on: 07/05/2022 16:15:00 UTC