---
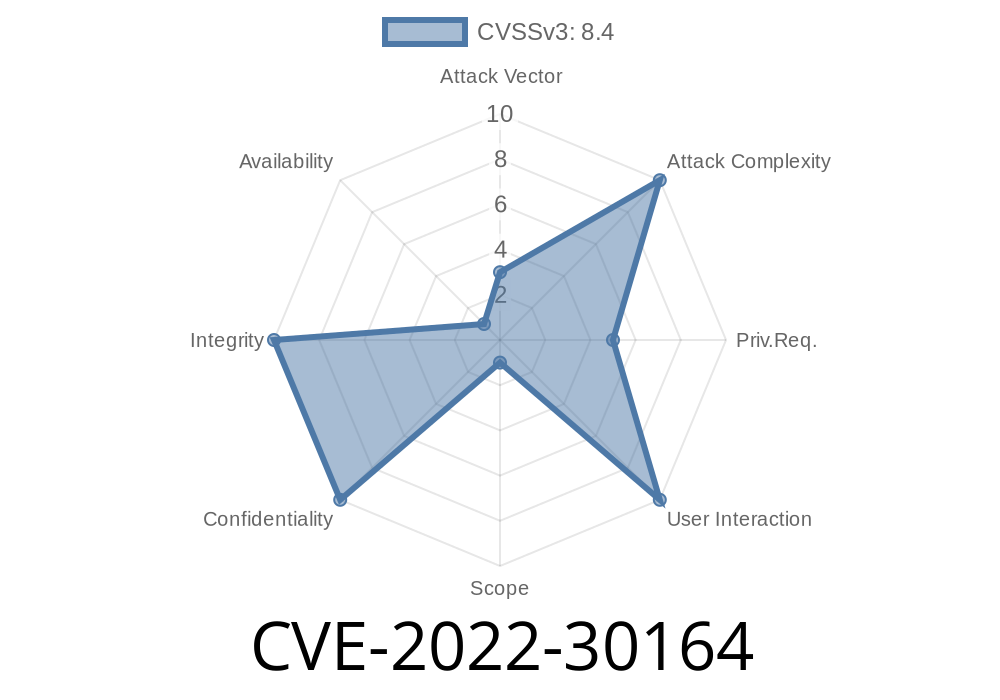
Kerberos is a widely used authentication protocol in Windows environments. In June 2022, Microsoft disclosed a security vulnerability—CVE-2022-30164—that affects how Kerberos handles security for AppContainers. This detailed post will walk you through what the vulnerability is, why it matters, how it can be exploited, and what you can do about it.
What is AppContainer?
AppContainer is a Windows security boundary used in sandboxing modern apps (such as those running on Microsoft Edge or certain Windows Store apps). It’s designed to isolate applications and limit their ability to cause damage or access sensitive resources.
You can read the official Microsoft advisory here
- Microsoft Security Response Center – CVE-2022-30164
The Vulnerability Explained
Normally, an application running within an AppContainer should not be able to authenticate as a different user or gain access to resources outside its security context. Due to a flaw in how Kerberos handled authentication tokens, it was possible for a compromised or malicious AppContainer application to bypass these restrictions and potentially obtain Kerberos tickets as another user.
In plain language:
*A sandboxed application could escape its box and act like someone else on the network.*
1. How Kerberos Handles AppContainer Tokens
Kerberos uses access tokens to confirm which permissions an application has. AppContainer tokens are specially marked to keep apps within their restricted sandbox.
// Pseudocode to check if a process is in AppContainer
BOOL IsAppContainer(HANDLE hToken) {
DWORD tokenInfo;
DWORD length;
return GetTokenInformation(
hToken,
TokenIsAppContainer,
&tokenInfo,
sizeof(tokenInfo),
&length
) && tokenInfo;
}
Windows and Kerberos should always enforce restrictions when a token comes from an AppContainer. Due to the bug, Kerberos was not checking this correctly.
The Setup
- Attacker gets code execution inside an AppContainer (maybe by getting you to run a malicious UWP app).
The Exploit Steps
1. The attacker’s app in the AppContainer requests a Kerberos ticket for a network resource (like a file share).
2. Due to the bug, Kerberos issues a service ticket that’s *not* properly limited to the AppContainer’s permissions.
The attacker can now use this ticket to access resources as if they weren’t sandboxed.
Proof-of-concept:
Here’s a simplified outline of what could be coded (for demonstration, not working exploit)
# Pseudo-code, not actual exploit!
import win32security
# Acquire an AppContainer token
token = win32security.OpenProcessToken(...)
# Request Kerberos ticket using API (with AppContainer token)
kerberos_ticket = get_kerberos_ticket(token, "cifs/targetserver")
# If vulnerable, the ticket is usable like a normal user ticket!
use_ticket_to_connect("cifs/targetserver", kerberos_ticket)
Note: The key is that Kerberos doesn’t limit the ticket, allowing improper network access.
Escalate privileges or steal sensitive data
Who is affected?
Mostly, this bug affects systems where AppContainers are in use—especially enterprises with strict sandboxing.
Official Patch
Microsoft released a fix in June 2022.
Apply all security updates!
- CVE-2022-30164 Patch Details
Final Thoughts
CVE-2022-30164 is another reminder that even advanced sandboxes like AppContainer can have escape hatches—especially when complex protocols like Kerberos are involved.
If you haven’t patched your Windows systems since June 2022, do it now.
References:
- Microsoft CVE-2022-30164 Advisory
- Kerberos Overview
- How AppContainers Work
*Stay safe, keep your software up-to-date, and always be cautious with sandboxed applications—the walls aren’t always as solid as they seem.*
Timeline
Published on: 06/15/2022 22:15:00 UTC
Last modified on: 07/07/2022 15:15:00 UTC