This vulnerability allowed the attacker to see all the details of the invoice. The vulnerability was in the service that receives the request for creating an invoice. The company did not have any security measures to protect its servers. The company did not have any security measures on the server where the images are stored. This allowed the attacker to access the server and steal all the images of the invoices. This vulnerability helps attackers to steal sensitive information such as credit card details, bank account numbers, etc. It is always recommended to have security measures in place to prevent attacks like this.
How to prevent Xero from being hacked?
In order to prevent Xero from being hacked, you need to take precautionary steps. First and foremost, it is important to secure your server. It is also recommended that you make sure that the operating system of your server is updated regularly so that hackers cannot use it easily. It is also important to minimize the number of people who have access to your server as well as ensuring that they are not untrusted with knowledge about the security measures of your company's servers. You should also make sure that you have a firewall installed on your servers and that these servers are protected by firewalls and IDS software.
An additional precautionary measure would be to ensure that all employees who have access to the server are aware and follow security guidelines for securing the system. Lastly, it is vital for companies in this industry to verify the legitimacy of any partners and contractors with whom they work with in order to protect their businesses from hackers.
Vulnerable URLs and Domains
To prevent this vulnerability, the company needs to tighten up its security measures. They need to make sure that the data is not stored on a server that is vulnerable to attack. This can be achieved by using encryption and password protection. Additionally, they must also make sure that there are no vulnerabilities in the website itself.
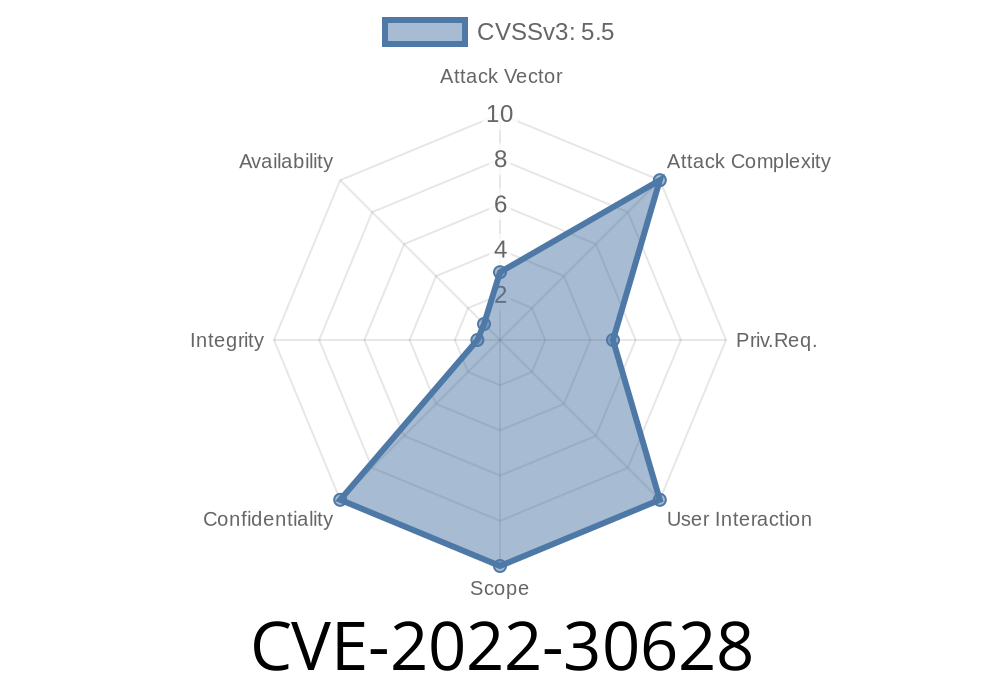
One example of this vulnerability is CVE-2022-30628. It allows attackers to see all the details of an invoice form and steal sensitive information like credit card and bank account numbers, etc. The company was vulnerable because it did not have any security measures for its server which has access to all the details of invoices being sent.
Timeline
Published on: 07/21/2022 16:15:00 UTC
Last modified on: 07/27/2022 22:35:00 UTC