*Discovered by Insyde engineering, patched in Insyde’s Kernel updates across multiple versions.*
Overview
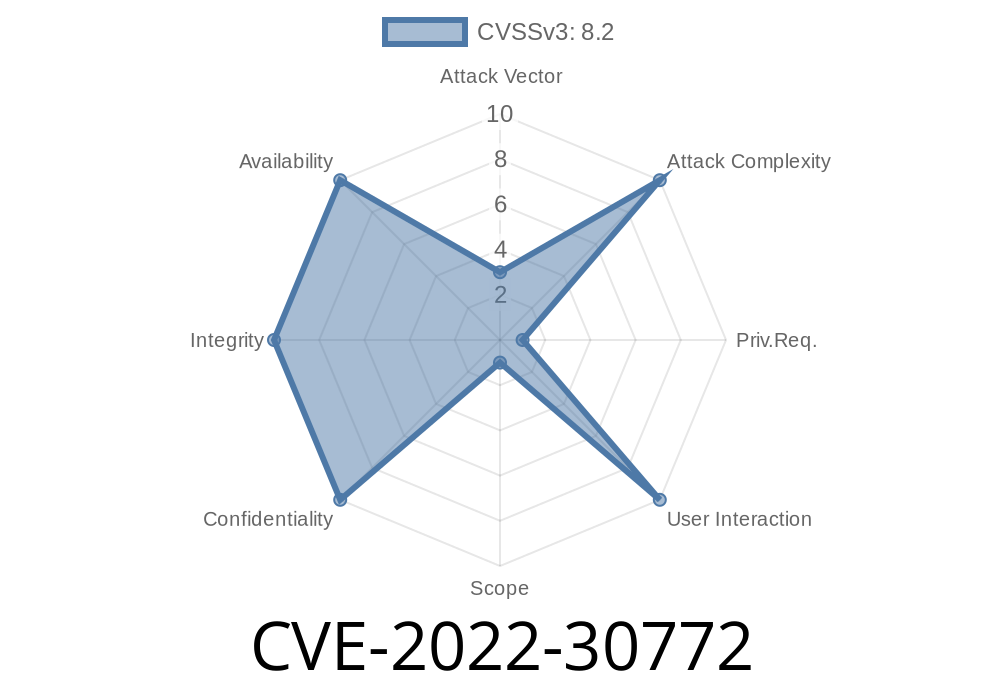
CVE-2022-30772 is a serious vulnerability found in the PnpSmm driver, specifically in its function code x52. In simple terms, if an attacker can manipulate the function’s input address, they could cause malicious code to overwrite key memory spaces—including SMRAM (System Management RAM) or crucial parts of the operating system kernel. This presents a dangerous opportunity for malware to escalate privileges or even fully compromise a device.
The vendor, Insyde Software, fixed this vulnerability across its supported kernels (see patch versions [below](#fixes-and-patches)). This post gives a practical breakdown of the issue, supported by code snippets and analysis, so you can understand how CVE-2022-30772 works and why it’s critical to patch.
What is PnpSmm and Function x52?
PnpSmm stands for “Plug & Play System Management Mode.” It’s a driver commonly found in UEFI firmware, responsible for system management tasks during booting and sometimes during system runtime.
A size (how much data to write).
The intent is for legit processes to update the SMBIOS table (which holds system info like BIOS vendor, version, etc). But what if malware tricks the driver into writing somewhere dangerous?
What’s the Problem?
The PnpSmm function x52 doesn’t properly check or restrict the input address. So, with enough know-how, an attacker could:
Call function x52.
2. Provide a malicious address that points to SMRAM (used by SMM, the most privileged CPU mode on x86) or a sensitive kernel memory location.
Overwrite that memory with their own payload.
SMRAM is supposed to be protected, since it holds SMM code and data. If compromised, attackers can use SMM privileges to bypass virtually all OS-level protections.
Suppose a simplified pseudocode for the vulnerable function
EFI_STATUS PnpSmmFunc52WriteToMemory(UINT8* WriteAddress, UINTN DataSize, void* Data) {
// [Missing: check if WriteAddress is safe!]
memcpy(WriteAddress, Data, DataSize);
return EFI_SUCCESS;
}
What’s missing?
A security check—such as making sure WriteAddress doesn’t point into SMRAM, kernel memory, or reserved regions.
Here’s how a simple exploit might go (pseudocode)
#define ADDRESS_TO_ATTACK xA000 // Hypothetical address in SMRAM or sensitive kernel space
// Craft data to inject (could be shellcode, etc.)
char evil_data[100] = {...};
// Call the vulnerable function
PnpSmmFunc52WriteToMemory((UINT8*)ADDRESS_TO_ATTACK, sizeof(evil_data), evil_data);
If successful, this would replace critical code/data with the attacker’s payload.
Impact
- Privilege Escalation: Attacker could inject code that runs at SMM or kernel level, bypassing OS protections.
Kernel 5.5: 05.52.30
Full security bulletin: SA-2022065 on Insyde's website
What Should You Do?
- Check your firmware version. If your device uses Insyde firmware, see if it’s been updated to one of the patched kernel versions.
Update firmware ASAP for affected devices.
- Watch for new system firmware updates from your manufacturer, as these fixes are usually distributed via system or motherboard vendors.
References
- Insyde Security Bulletin SA-2022065 (Original advisory)
- Official CVE Entry *(external site, may differ in detail)*
In Summary
CVE-2022-30772 shows why firmware vulnerabilities are serious business. When memory addresses are not checked, attackers can abuse even legitimate system services to break into SMRAM and the OS kernel’s most protected areas. This is why firmware security matters—and why you should always keep your devices updated!
If you manufacture or manage devices with Insyde firmware, patch now. If you’re a security researcher, dig into your platform’s firmware—there may be more risks lurking beneath the operating system surface.
Timeline
Published on: 11/15/2022 21:15:00 UTC
Last modified on: 11/23/2022 17:24:00 UTC