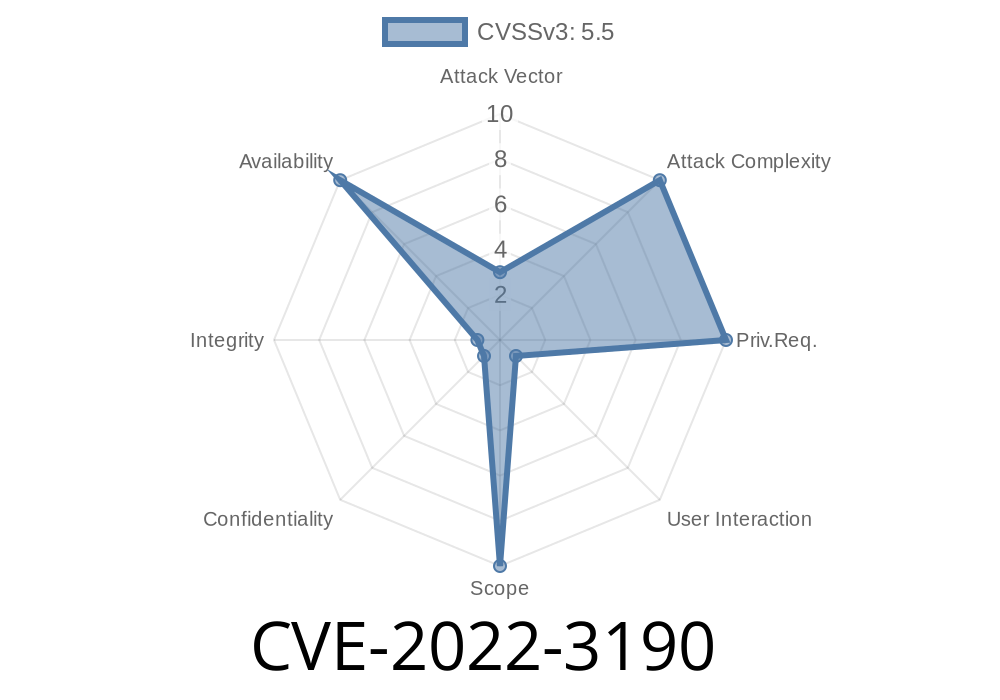
The Wireshark application, a widely-used network protocol analyzer, has been found to contain a vulnerability associated with CVE-2022-3190. This vulnerability is present in the F5 Ethernet Trailer protocol dissector, affecting the Wireshark versions 3.6. to 3.6.7 and 3.4. to 3.4.15. In this article, we will delve into the infinite loop in the F5 Ethernet Trailer protocol dissector, examine how the vulnerability can be exploited to perform denial of service (DoS) attacks via packet injection or crafted capture files, and discuss the original references.
The Vulnerability
The CVE-2022-3190 vulnerability lies in the F5 Ethernet Trailer protocol dissector, which is responsible for analyzing F5 Ethernet Trailer protocol packets. The infinite loop in this dissector occurs when it fails to properly handle malformed packets, eventually leading to an application crash or rendering the application unresponsive.
An attacker may exploit this vulnerability to launch a denial-of-service attack via two methods
1. Packet Injection: By injecting specifically tailored malformed packets into the network traffic, the attacker can cause the Wireshark application to enter an infinite loop, thereby leading to an application crash or making the application unresponsive. This approach requires that the attacker has access to the network and the ability to create and send malformed packets.
2. Crafted Capture Files: Another way to exploit this vulnerability is by sharing a specially crafted capture file with the target Wireshark user. Once the user opens this malformed capture file in Wireshark, the application enters the infinite loop, resulting in a denial-of-service condition.
Here is a simple Python code snippet to demonstrate the general idea of creating a malicious packet
import scapy.all as scapy
def create_malicious_packet():
# Create a malformed F5 Ethernet Trailer packet
packet = scapy.Ether(dst="00:00:00:00:00:00", src="00:00:00:00:00:00") / scapy.IP() / scapy.TCP() / bytes([x01, x23, x45, x67])
# Save the crafted packet to a .pcap file
scapy.wrpcap('malicious_packet.pcap', packet)
if __name__ == "__main__":
create_malicious_packet()
Please note that this snippet is for educational purposes only and should not be used for malicious intent.
Original References
The CVE-2022-3190 vulnerability was first discovered and reported by the Wireshark team and has been documented in the following resources:
1. Wireshark Security Advisory: WSA-2022-03
2. NIST National Vulnerability Database: CVE-2022-3190
Mitigation
To protect against this vulnerability, Wireshark users are advised to upgrade to the patched versions - Wireshark 3.6.8 or 3.4.16. These releases contain the necessary fixes to address the infinite loop issue in the F5 Ethernet Trailer protocol dissector.
Conclusion
The CVE-2022-3190 vulnerability in Wireshark's F5 Ethernet Trailer protocol dissector can result in a denial-of-service attack if exploited by an attacker. To mitigate this risk, users should update their Wireshark installations to the patched versions, 3.6.8 or 3.4.16, which resolve this issue. Additionally, users should always be cautious when opening capture files from untrusted sources, as this may prevent the exploitation of this vulnerability through crafted capture files.
Timeline
Published on: 09/13/2022 15:15:00 UTC
Last modified on: 09/14/2022 22:34:00 UTC