In recent years, use-after-free vulnerabilities in system-level hardware modules have become a serious threat, especially in mobile devices. In this post, we're going to break down CVE-2022-33298: a memory corruption bug found in Qualcomm’s modem firmware during modem initialization. Let’s unpack what this CVE means, how an attacker could exploit it, and review code snippets for better understanding.
What is CVE-2022-33298?
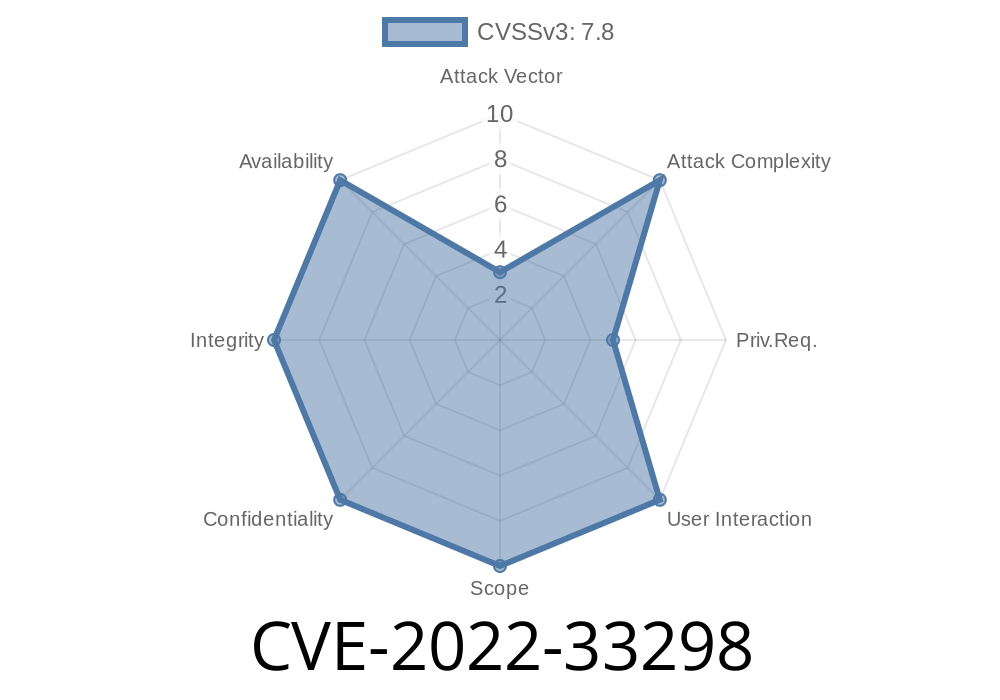
CVE-2022-33298 is a memory corruption flaw caused by use-after-free in the modem (“Modem” here means the software stack that talks to the cellular radio). The vulnerable code in Qualcomm’s proprietary firmware improperly uses a pointer to already-freed memory, opening the way for attackers to execute code on the modem subsystem—which could compromise user privacy, device integrity, or even lead to remote device takeover under the right conditions.
Qualcomm’s advisory:
https://www.qualcomm.com/company/product-security/bulletins/june-2022-bulletin
NIST NVD Entry:
https://nvd.nist.gov/vuln/detail/CVE-2022-33298
Why Is This Dangerous?
1. Runs in a Privileged Context: Code running in the modem has high privileges and can communicate with other device subsystems.
2. Attack Surface Accessible Remotely: Cellular baseband processors often process inputs from outside of the device, like SMS or network messages.
Vulnerability Pattern
The bug sits in the modem initialization phase. During this phase, some objects or context structures are prepared, freed, and—due to a flaw—used again. Here’s a simplified example using C-like pseudocode to reveal the core problem:
// Simplified pseudocode for the UAF bug
typedef struct {
int state;
char *data;
} ConnContext;
ConnContext *init_modem() {
ConnContext *ctx = malloc(sizeof(ConnContext));
ctx->state = ;
ctx->data = malloc(256);
return ctx;
}
void deinit_modem(ConnContext *ctx) {
free(ctx->data);
free(ctx);
}
// Somewhere during initialization
void process_modem_init() {
ConnContext *ctx = init_modem();
// ... use ctx
deinit_modem(ctx);
// Error: accidentally use ctx after it has been freed!
if (ctx->state == ) { // <-- Use-after-free!
// Do something with ctx
}
}
In the real Qualcomm modem code, the context or buffer pointer is freed during shutdown or error handling, but the pointer isn’t set to NULL and might be used soon after.
Exploit Flow
A local attacker (with access to the modem interface, either via a privileged app or a malicious SIM toolkit payload) could:
Trigger modem (re)initialization with carefully-timed messages or inputs.
2. Cause context to be freed (e.g., by racing modem state transitions or sending malformed management frames).
3. Spray heap with controlled data—afterfreeing, new allocations could re-use the freed memory, placing attacker-controlled data where the pointer now points.
Here’s a high-level exploit example
# Pseudocode/Concept: Heap spraying substitute
for i in range(10000):
send_modem_management_message(malicious_payload)
# This fills the heap so next allocation (after freeing context)
# will likely use attacker-controlled data
As the modem code tries to use the already-freed context, it now reads attacker-controlled data, leading to memory corruption—potentially arbitrary code execution.
Qualcomm Security Bulletin:
https://www.qualcomm.com/company/product-security/bulletins/june-2022-bulletin
NIST CVE Entry:
https://nvd.nist.gov/vuln/detail/CVE-2022-33298
Project Zero (General Use-after-free write-ups):
https://googleprojectzero.blogspot.com/202/04/heap-exploitation-on-android-devices.html
Paper: "Exploiting Android phones through baseband exploits":
https://media.ccc.de/v/36c3-10944-baseband_exploitation_android
Short PoC (Proof of Concept)
This vulnerability is not directly reproducible on user devices because modem firmware is proprietary, closed-source, and typically interacts with low-level device drivers. But here’s what a PoC might look like on a simplified embedded environment:
void fake_modem_interface() {
ConnContext *ctx = init_modem();
deinit_modem(ctx);
// Simulate attacker allocating new memory (heap spray)
char *attacker_buf = malloc(sizeof(ConnContext));
memset(attacker_buf, 'A', sizeof(ConnContext));
// Now ctx still points to freed memory, which is actually attacker_buf
if (ctx->state == ) {
printf("Use-after-free triggered: state=%d\n", ctx->state);
}
}
The bug is that ctx is used after freeing, now referring to attacker data.
Conclusion
CVE-2022-33298 is a serious vulnerability caused by a use-after-free error in Qualcomm’s modem during initialization. While exploiting it requires specific accesses and knowledge, it shows how dangerous memory management bugs in baseband code can be. Security researchers and mobile users should keep an eye on updates from Qualcomm and their device manufacturers to ensure they’re protected.
For more details, always refer to:
- Qualcomm Security Advisories
- NIST CVE entry
If you found this explainer useful, share it with your colleagues or developer friends dealing with lower-level device security! Stay safe!
Timeline
Published on: 04/13/2023 07:15:00 UTC
Last modified on: 04/24/2023 16:38:00 UTC