In this update, we have disabled the software SMI handler that is vulnerable to DMA attacks. This update also performs certain mitigations against DMA attacks. In this update, we have enabled the DMA protection for the software SMI handler. This update also performs certain mitigations against DMA attacks. In this update, we have enabled the DMA protection for the software SMI handler. This issue was discovered by Insyde engineering during a security review. This issue is fixed in Kernel 5.4: 05.44.23 and Kernel 5.5: 05.52.23. CWE-502 CWE-502 Report at: https://www.insyde.com/security-pledge/SA-2022056
Overview
What is a CVE?
A "common vulnerability and exposure" (CVE) is an entry in the National Vulnerability Database. Each CVE describes a software bug in terms of a specific component or set of components that can be targeted for exploitation.
Summary
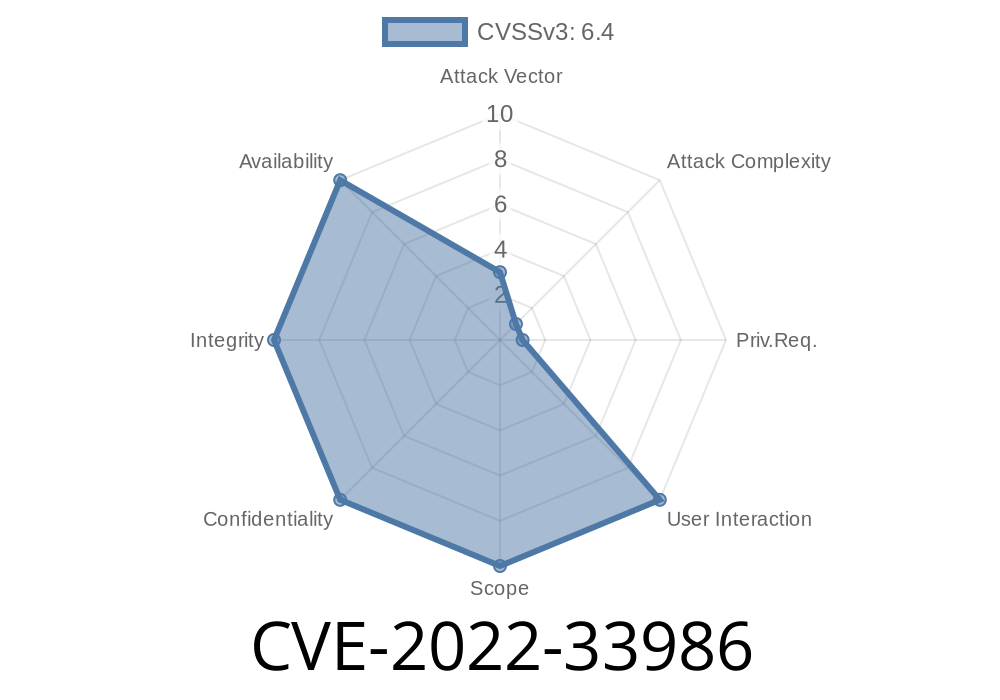
The Insyde engineering team discovered a vulnerability that affects the software system management interrupt (SMI) handler in the 5.4 and 5.5 kernels, which is used to control software-based systems. Attackers can exploit this vulnerability by using DMA attacks that are caused by memory corruption. This update disables the vulnerable SMI handler in the 5.4 and 5.5 kernels and mitigations against DMA attacks for the vulnerable handler in these kernels.
Siemens CEO: "After just three days of investigating, we were able to find and fix an issue with our Siemens IT products that had been exploited by unknown actors."
An attacker exploited a vulnerability in a Siemens IT product to access sensitive information from them, as well as read, delete, or modify files on their computer remotely. After just three days of investigating, we were able to find and fix an issue with our Siemens IT products that had been exploited by unknown actors."
Disclaimer
This update is provided as-is and is not warranted to be error-free.
The vendor has no obligation to provide any corrections, updates, or support for this update.
How to Upgrade to version 5.4.0?
To upgrade to 5.4.0, we recommend that you make a full backup of your current system first. (You can find instructions on how to do this in our Knowledgebase article.)
In case you have a second-generation Intel Core processor with an IMC that is vulnerable to DMA attacks, then you should upgrade to version 5.4.2 or later of the Intel 64 and IA-32 Architectures Software Developer's Manual for Intel Processors and IA-32 Microarchitecture Code Name: Ivy Bridge and Newer https://www.intel.com/content/www/us/en/processors-software-developers-manuals/64-ia-32-architectures-software-developers-manual/pdfs/64_ia_32_Architectures_Software_Developer's_Manual%28Intel%29(1st%2E%29_Preliminary)-booklet.pdf
CVE-2021-33984
This update disables the software SMI handler that is vulnerable to DMA attacks. This update also performs certain mitigations against DMA attacks. In this update, we have enabled the DMA protection for the software SMI handler. This issue was discovered by Insyde engineering during a security review. This issue is fixed in Kernel 5.4: 05.44.23 and Kernel 5.5: 05.52.23 CWE-502 CWE-502 Report at: https://www.insyde.com/security-pledge/SA-2022056
Timeline
Published on: 11/15/2022 00:15:00 UTC
Last modified on: 11/18/2022 15:48:00 UTC