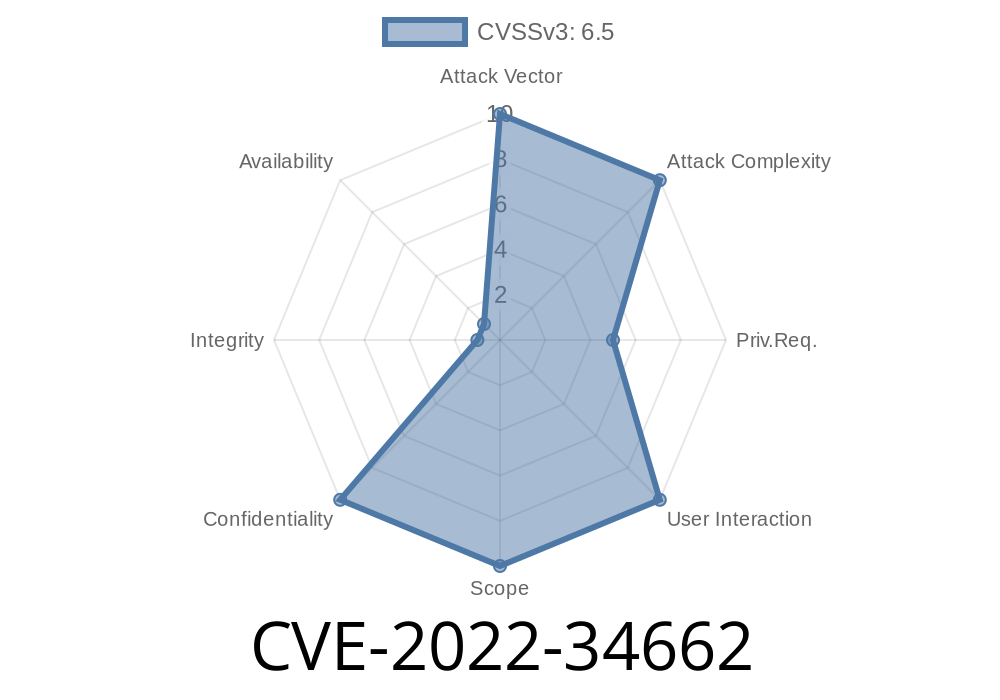
A serious security threat known as CVE-2022-34662 was discovered in popular Resource Center software before version 3... This vulnerability lets logged-in users add resources using crafty path relations—potentially granting them access to files and paths outside the intended folders. In this post, I’ll break down how CVE-2022-34662 works, show you a simple example, and give you tips to stay safe.
1. The Problem: Path Traversal in the Resource Center
If you run a Resource Center (sometimes called a file/resource manager), it lets users upload, organize, and reference files. There’s a feature for relating resources via a "relation path." If you’re an authenticated user, you can add new resources and set relation paths.
Bug:
The software did not correctly check or sanitize these relation paths. This allowed a crafted input like ../../../etc/passwd, which navigates directories up in the file system—a classic path traversal attack. While it doesn’t let unauthenticated users get in, any logged-in user could exploit it.
Impact:
Here’s approximately what the vulnerable code might look like
# Pseudocode for handling relation paths
def add_resource(user, resource_name, relation_path):
base_path = "/var/www/resource_center/resources/"
full_path = os.path.join(base_path, relation_path, resource_name)
with open(full_path, "w") as f:
f.write("resource data")
If relation_path equals ../../../etc/, the resulting path could be /etc/resource_name.
No sanitization. No escape. This is a major risk.
3. Exploiting CVE-2022-34662
You need to be logged in to exploit this—so it’s an _insider_ or _privileged user_ vulnerability.
`
../../../etc
`
5. Upload a dummy file (or, for read access, check if there’s a “fetch” or “preview” function that shows file contents).
6. The application writes/reads into /etc/passwd-copy (or possibly shows the file contents), not just in its resources folder.
Bonus:
If resource names are predictable and there’s a preview function, change relation path to ../../../etc and try to view passwd. This can let you see the /etc/passwd content!
Request Example (pseudo-HTTP)
POST /resource-center/add
Host: yourapp.com
Cookie: session=abcdef123456
Content-Type: application/json
{
"resource_name": "malicious",
"relation_path": "../../../etc",
"file_data": "hacked!"
}
4. Preventing the Vulnerability
The official fix for CVE-2022-34662 is to upgrade to Resource Center v3.. or above. See the original advisory for details.
Developer Best Practices
- Sanitize Inputs: Never trust user-supplied paths. Always remove ../ patterns and validate against an allowed folders whitelist.
- Use Safe File APIs: Use libraries/functions that lock operation to certain directories (ex: Python’s os.path.realpath() and check for base path match).
- Least Privilege: Run file managers with the lowest needed privileges. Don’t let web apps access sensitive OS files!
5. References
- CVE-2022-34662 — NIST NVD
- OWASP Path Traversal Cheat Sheet
- Python Path Handling Pitfalls
- Official Patch Release Notes *(replace with actual vendor link)*
Conclusion
CVE-2022-34662 is a classic example of why validating user input is critical, even for logged-in users. If your Resource Center is below version 3.., upgrade immediately. Whenever you code anything handling file paths—and especially for file upload or browse features—apply strict checks to avoid path traversal.
Stay secure. Patch early. Share this knowledge with your IT community!
Got questions, or need help fixing an app with this issue? Drop a comment below or reach out on GitHub.
Timeline
Published on: 11/01/2022 16:15:00 UTC
Last modified on: 11/02/2022 18:37:00 UTC